- Automated checks are run on every commit or pull request during continuous integration testing, which catches bugs before an artifact is released.
- The best CI testing strategies have clear quality gates, a mix of tests at different levels, and reliable pipelines that strike a balance between speed and depth.
- With smart test selection, incremental builds, and pipeline analytics, Harness helps teams do more CI testing.
Software changes quickly. Dependencies are always changing. With AI-generated code, security expectations go up quite frequently. That's why continuous integration testing is important: it makes every commit a quick, automated checkpoint, so broken builds and risky changes are found before they spread.
You can standardize those checkpoints across teams and repos, run tests at the same time, and keep feedback tight even as your codebase grows with a CI platform like Harness Continuous Integration. The end result is a pipeline that developers can trust and releases that don't depend on chance.
What Is Continuous Integration Testing?
Definition: Continuous integration testing is the practice of running automated tests and checks as part of every CI pipeline run. Every change is built, tested, and validated in a repeatable environment so failures show up early, when they’re cheapest to fix.
CI itself is about frequent merges and automated verification. This CI overview is a good refresher on the practice and why teams prioritize fast feedback loops.
What “Testing” Includes in CI
A modern CI run usually goes beyond unit tests. It commonly includes:
- Build verification: Does the code compile/package and produce an artifact?
- Automated tests: Unit, integration, component/contract, and smoke tests.
- Quality checks: Linting and static analysis.
- Security and compliance checks: Dependency risk, container scanning, and policy checks.
The output of CI testing is confidence: an artifact that’s buildable, testable, and safe enough to move forward.
How CI Testing Works in a Pipeline
A typical CI testing flow looks like this:
- A developer pushes code or opens a pull request.
- CI spins up a clean build environment.
- The pipeline runs fast checks first (lint/unit tests).
- Deeper checks run next (integration/security/license gates).
- If everything passes, CI publishes the artifact to a registry.
- Results report back to developers (and optionally block merges).
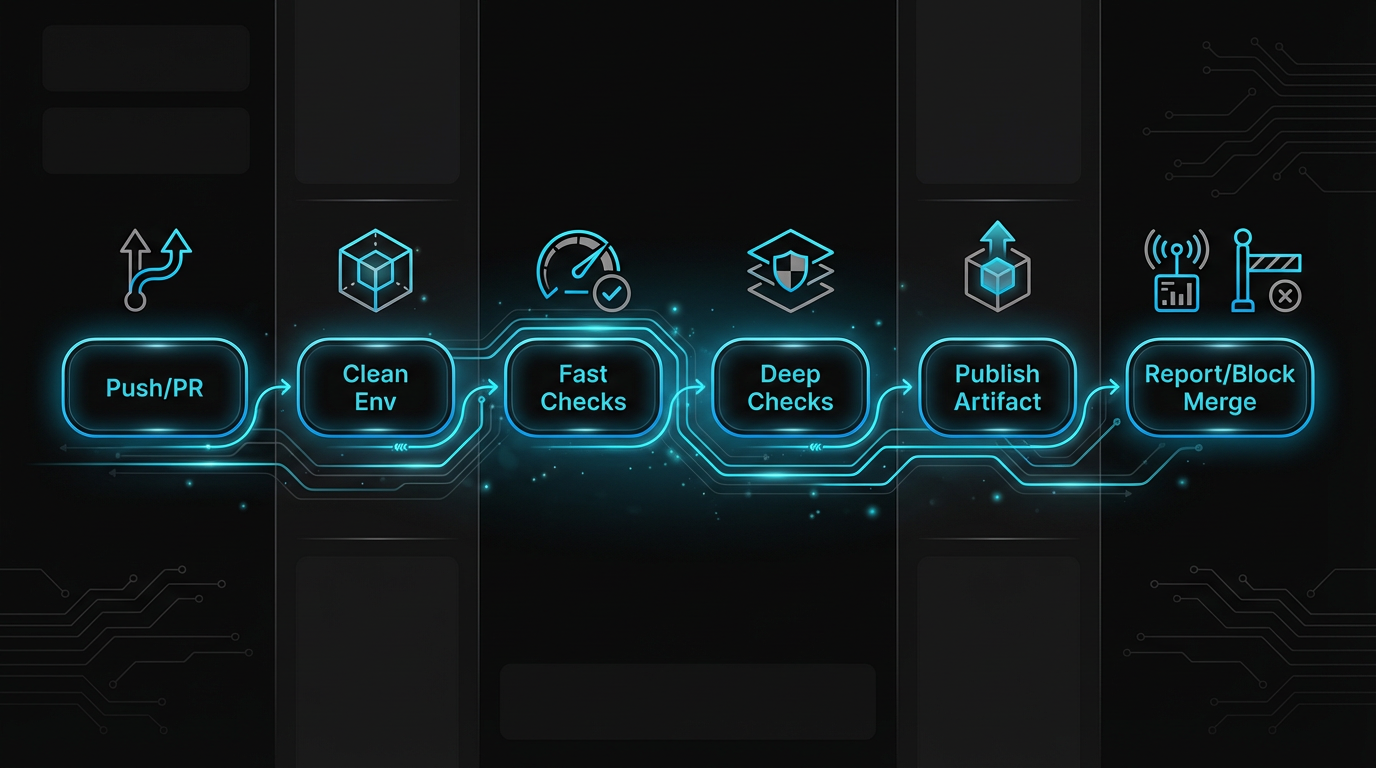
The best pipelines are designed to fail fast. Put the quickest, most deterministic checks first so developers get feedback while the context is still fresh.
On-Process vs. Off-Process Checks
It’s useful to separate CI testing into two categories:
- On-process testing runs directly on the CI runner (unit tests, linters, local static analysis).
- Off-process testing sends code or artifacts to external systems (container scanning, SAST/DAST services, SBOM generation, policy engines).
- DAST typically requires a running app and is often post-CI (or in a separate pipeline stage)
Most teams combine both. The goal is to keep on-process checks fast and make off-process checks targeted and policy-driven.
Types of Continuous Integration Tests to Run
You don’t need every test on every commit. You need the right mix, at the right time.
1. Code Quality and Static Analysis
Start CI runs with fast, low-flake checks:
- Formatting/linting
- Style rules and complexity checks
- Static analysis for common bug patterns
These checks catch issues before they become test failures downstream.
2. Unit Tests
Unit tests are the foundation of CI testing because they’re fast, deterministic, and isolate logic.
Best practice: Make unit tests a hard gate for merge.
3. Integration and Contract Tests
Integration tests validate how modules and services work together (API boundaries, shared libraries, data interactions). Contract tests are especially helpful in microservices because they verify expectations without requiring every service to be live in the same environment.
In CI, keep these tests:
- Ephemeral (spin up what you need, then tear it down)
- Scoped (focused on changed services and known dependencies)
- Parallel (split by service, package, or test suite)
4. Artifact and Supply Chain Checks (Security + License)
CI is where supply chain risk becomes visible. If your pipeline produces an artifact, you should know what’s inside it and whether it meets policy.
A few practices that hold up across industries:
- Follow a secure development baseline. NIST’s Secure Software Development Framework (SSDF) lays out recommended practices you can map to CI quality gates and release controls.
- Generate an SBOM for artifacts you release. CISA maintains practical SBOM guidance and resource collections, including community-led definitions of SBOM types.
- Use standard SBOM formats. CycloneDX is a widely used BOM format designed for software supply chain transparency.
- Harden build provenance. OpenSSF’s SLSA provides a maturity model for strengthening the integrity of build systems and artifacts.
- Sign and verify artifacts. Sigstore is a common choice for signing/verification workflows without long-lived key management.
You don’t need to implement everything at once. Start with the checks most likely to block a safe release: vulnerable dependencies, secret exposure, and container/image issues.
Continuous Integration Testing vs. Continuous Testing
These terms get conflated.
- Continuous integration testing focuses on fast, repeatable checks inside the CI pipeline to validate an artifact.
- Continuous testing spans the full delivery lifecycle, including performance tests, end-to-end tests in shared environments, and ongoing validation after deployment.
A simple rule: if a test requires a long-lived environment to be meaningful (examples: full perf suite, full E2E across shared env, long-running soak), it usually belongs after CI.
Best Practices for Reliable CI Testing
Great CI testing is less about “running more tests” and more about building a pipeline that developers trust. Use the practices below to keep feedback fast, results reliable, and gates meaningful as you scale.
Keep Feedback Loops Short
- Put the fastest checks first
- Parallelize by suite and service
- Cache dependencies and build outputs
Treat Quality Gates as Product Decisions
Quality gates define what “good enough” means to release. Make them explicit:
- What blocks a merge?
- What blocks artifact publishing?
- What’s allowed to warn while you ramp up?
Reduce Flakiness Ruthlessly
Flaky tests create alert fatigue and erode trust in CI.
- Isolate external dependencies
- Eliminate shared state between tests
- Quarantine and fix flaky tests (don’t normalize them)
Make Results Visible (and Actionable)
Track trends like duration, failure rate, and the most common failure causes. If teams can’t see what’s slowing them down, they can’t improve.
Recommended CI test mix by stage
How Harness Helps You Scale Continuous Integration Testing
Harness is built to keep CI testing fast and predictable as your codebase grows.
- Run CI on optimized infrastructure and standardize pipelines
- Shorten test cycles with intelligent test selection using Test Intelligence.
- Avoid rebuilding from scratch with Incremental Builds.
- Improve reliability over time using CI analytics and insights.
For teams getting started, the fastest path is to follow the onboarding guide and ship a first pipeline end-to-end.
Bringing Security and Compliance Into CI
If you want security checks to be first-class CI gates (without stitching together a dozen disconnected tools), Harness provides options for:
- Orchestrating scans and correlating results with Security Testing Orchestration
- Implementing SBOM generation and supply chain controls with Supply Chain Security
Once an artifact is validated in CI, it can flow into release pipelines for progressive delivery and governance using Harness Continuous Delivery.
Improve CI Testing Without Slowing Teams Down
Continuous integration testing works when it’s faster than debugging in staging, and trusted enough that teams don’t “click through” failures.
If you want to modernize CI testing across teams, start with these moves: make unit tests and build verification mandatory, add integration tests that can run in ephemeral environments, shift supply chain checks left (SBOM + dependency risk + artifact policy), and optimize speed with test selection, caching, and parallelism
Want to see what a faster, more observable CI testing workflow looks like in practice? Request a Harness platform demo.
Continuous Integration Testing: Frequently Asked Questions (FAQs)
These are the most common questions teams ask when they’re tightening CI quality gates or speeding up pipelines. Use the answers below as quick guidance.
What is continuous integration testing?
Automated testing and validation that runs inside CI pipelines every time code is changed is called continuous integration testing. It usually has unit tests, integration checks, static analysis, and early security and compliance checks.
Which tests should run in CI?
At minimum: build verification, unit tests, and fast quality checks. Many teams then add scoped integration/contract tests plus dependency and artifact security checks before publishing.
How fast should CI testing be?
Fast enough that developers can fix issues immediately, usually within minutes, not hours. Achieving that often requires parallelism, caching, and running only the tests impacted by a change.
What’s the difference between CI testing and continuous testing?
CI testing validates the artifact inside the build pipeline. Continuous testing covers the full lifecycle, including performance/end-to-end testing in realistic environments and validation after deployments.
How does Harness help with continuous integration testing?
Harness CI helps teams speed up and grow CI testing with features like smart test selection, incremental builds, and analytics. It also has optional security orchestration and supply chain controls for when you need policy-backed gates.
