
Visualizing the DNA of Distributed Attacks
We are thrilled to announce the launch of Radar, a major update to Harness Bot & Abuse Protection that fundamentally changes how security teams investigate and respond to sophisticated threats.
Sophisticated bot attacks are rarely isolated incidents. They are complex networks of connected identities, shared fingerprints, and coordinated behaviors. Traditional lists and tables pulled from disparate logs and event data fail to capture this reality, forcing SOC analysts to manually correlate relevant attack data—a process that costs hours when seconds matter in a potential breach.
Introducing Radar in Harness Bot & Abuse Protection
Radar changes the game for bot attack response. It is an intelligent threat visualization engine that instantly unmasks hidden relationships in bot attacks, turning the abstract "DNA" of an automated threat into a clear, interactive map.
It helps with
- Speed to Verdict: What used to take hours of manual cross-referencing now takes seconds of visual inspection.
- Explainable Security: Radar "white-boxes" our detection logic, giving you visual proof of why we flagged a cluster of users.
- Enterprise-Grade Depth: Built to meet the rigorous demands of leading financial institutions and E-Commerce, Radar handles the complexity of high-stakes fraud investigations with ease.
Why SecOps Teams Need Threat Visualization
SOC analysts struggle to quickly respond to advanced threats and bot attacks targeting their organization’s systems. Analysis of recent breach data shows that on average organizations take roughly six months to identify the related incident. Advanced automated bot and abuse attacks, increasingly accelerated with AI, frequently go undiscovered for this time period. The harsh reality is that data relationships and system interconnects in enterprise environments are complex to unwind as automated threats play out, leaving significant incident response gaps for threat detection.
- Inhibited response: Security teams spend days, weeks, or months manually cross-referencing siloed data, delaying incident response when speed is critical.
- Opaque Security: Detection logic in other bot mitigation offerings is a black box, leaving SecOps teams with little insight or evidence to justify why users or clusters are flagged.
- Limited Depth: Existing tools struggle to handle the complexity and scale of high-stakes fraud investigations, falling short of enterprise requirements for financial institutions and e-commerce.
Radar Key Capabilities
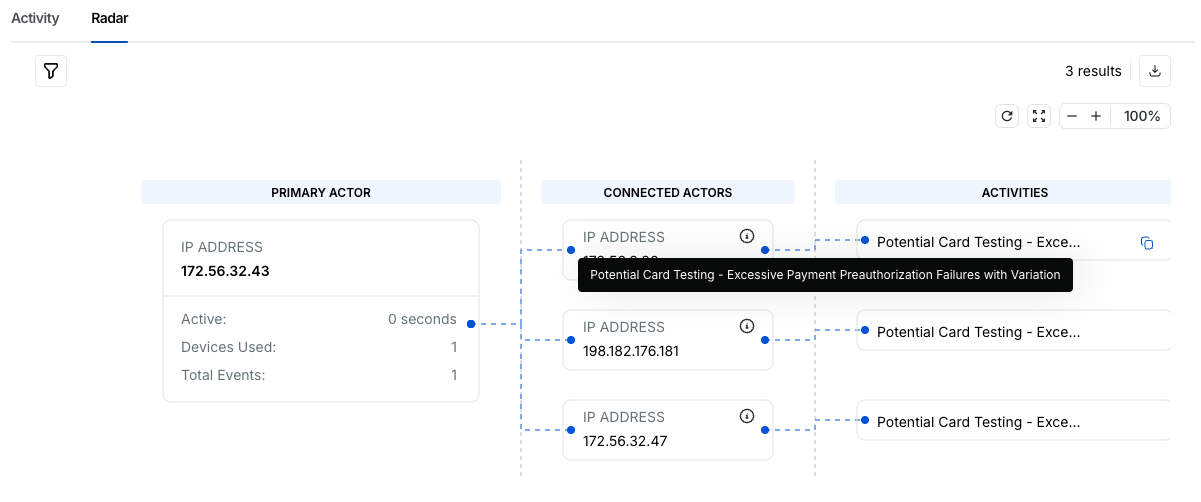
1. The Unified Threat Canvas
Stop investigating accounts in silos. Radar projects user connections onto an interactive graph, instantly revealing the shared threat signatures—such as IP subnets, device fingerprints, and behavioral patterns—that bind disparate accounts and activities together. You can now see the shape of the attack campaign at a glance.
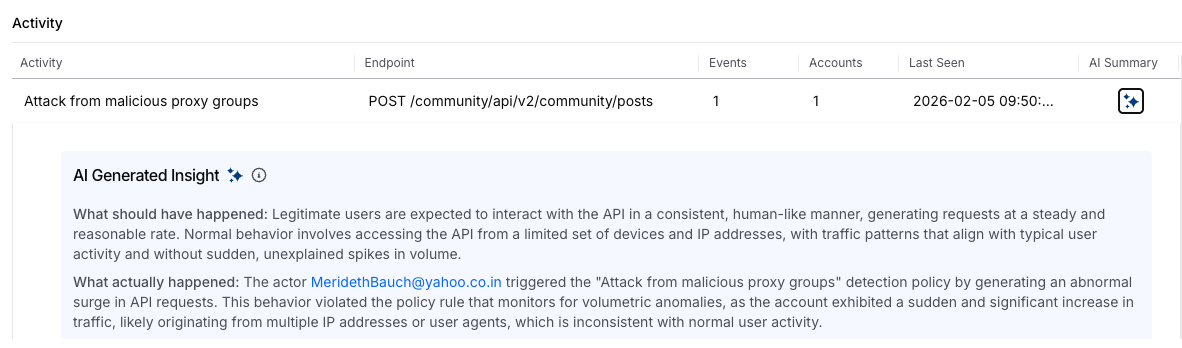
2. AI-Powered Context
Understanding why accounts are connected is just as important as knowing that they are connected. Radar integrates deep AI insights that analyze the cluster to provide a narrative summary of the attack. Whether it's a "distributed credential stuffing attack via a residential proxy ring" or "coordinated inventory hoarding," Harness AI explains the security context so you don't have to guess.
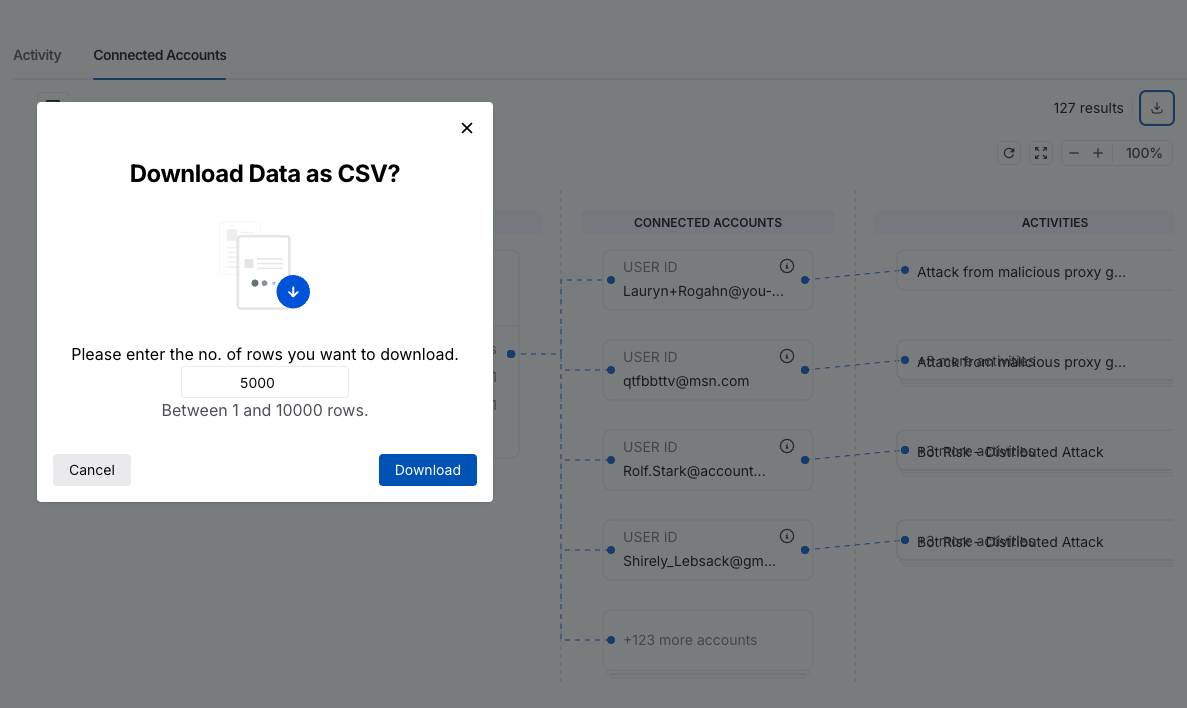
3. Portable Forensics
We know your investigation doesn't always end in our console. Radar features a robust export engine that packages every data point—user details, threat activities, and linkage evidence—into a comprehensive format ready for your SIEM and SOAR tools or related DFIR workflows.
Get Started Today
Radar is available immediately with your existing Harness Bot & Abuse Protection subscription. There is no additional cost or setup required.
- Current Customers: Log in to your dashboard today to start exploring your threat data in a whole new dimension.
- New to the Platform? If you aren't yet protected, contact us to schedule a personalized demo of Radar in action.

