Featured Blogs

- Harness IaCM introduces native Terragrunt support, enabling true enterprise-grade orchestration at scale.
- Teams can now manage Terraform, OpenTofu, and Terragrunt in a single platform without fragmented tooling.
- Built-in governance, policy enforcement, and approvals streamline secure infrastructure operations.
- End-to-end visibility and drift detection improve reliability across complex, multi-environment deployments.
- The launch marks a major step toward a unified, multi-IaC control plane for modern infrastructure teams.
Bringing First-Class Terragrunt Support to IaCM
“We’ve been operating in a hybrid environment with both OpenTofu and Terragrunt, and Harness has made it much easier to bring those workflows together into a single, consistent platform with IaCM. The addition of Terragrunt support is a valuable step toward simplifying how we manage infrastructure at scale.”
— Lead Platform Engineer, Enterprise Customer
Infrastructure as Code is now a standard for modern cloud operations, with most enterprises using IaC to provision and manage environments. However, as adoption grows, so does complexity. Teams are no longer managing a handful of environments. They are operating across multiple regions, accounts, and services, often at massive scale.
This is where traditional approaches begin to fall short.
As organizations scale their infrastructure, Terraform alone is often not enough. Teams adopt Terragrunt to manage complex, multi-environment deployments, but they are often forced to stitch together fragmented tooling that lacks visibility, governance, and consistency.
At Harness, we are changing that.
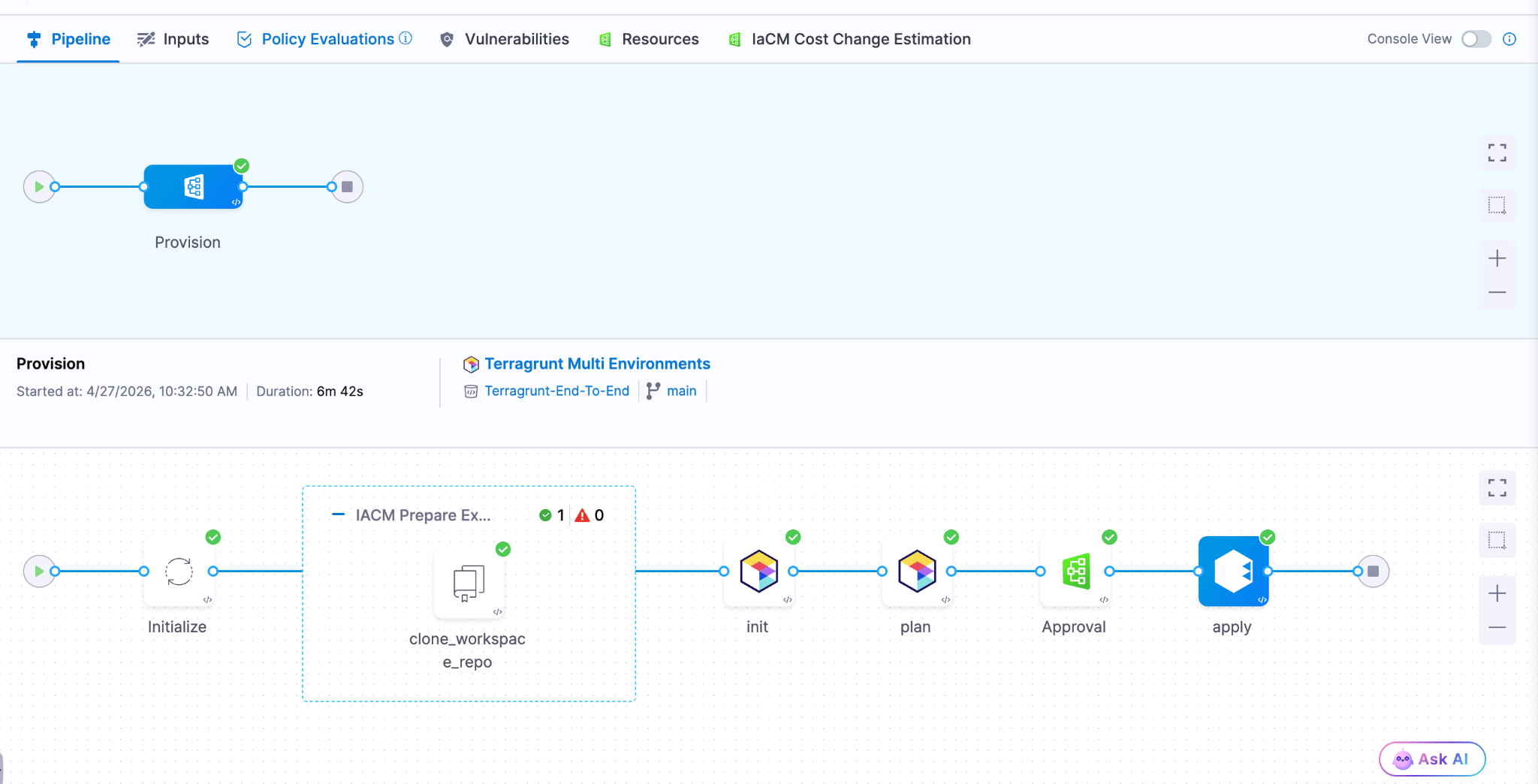
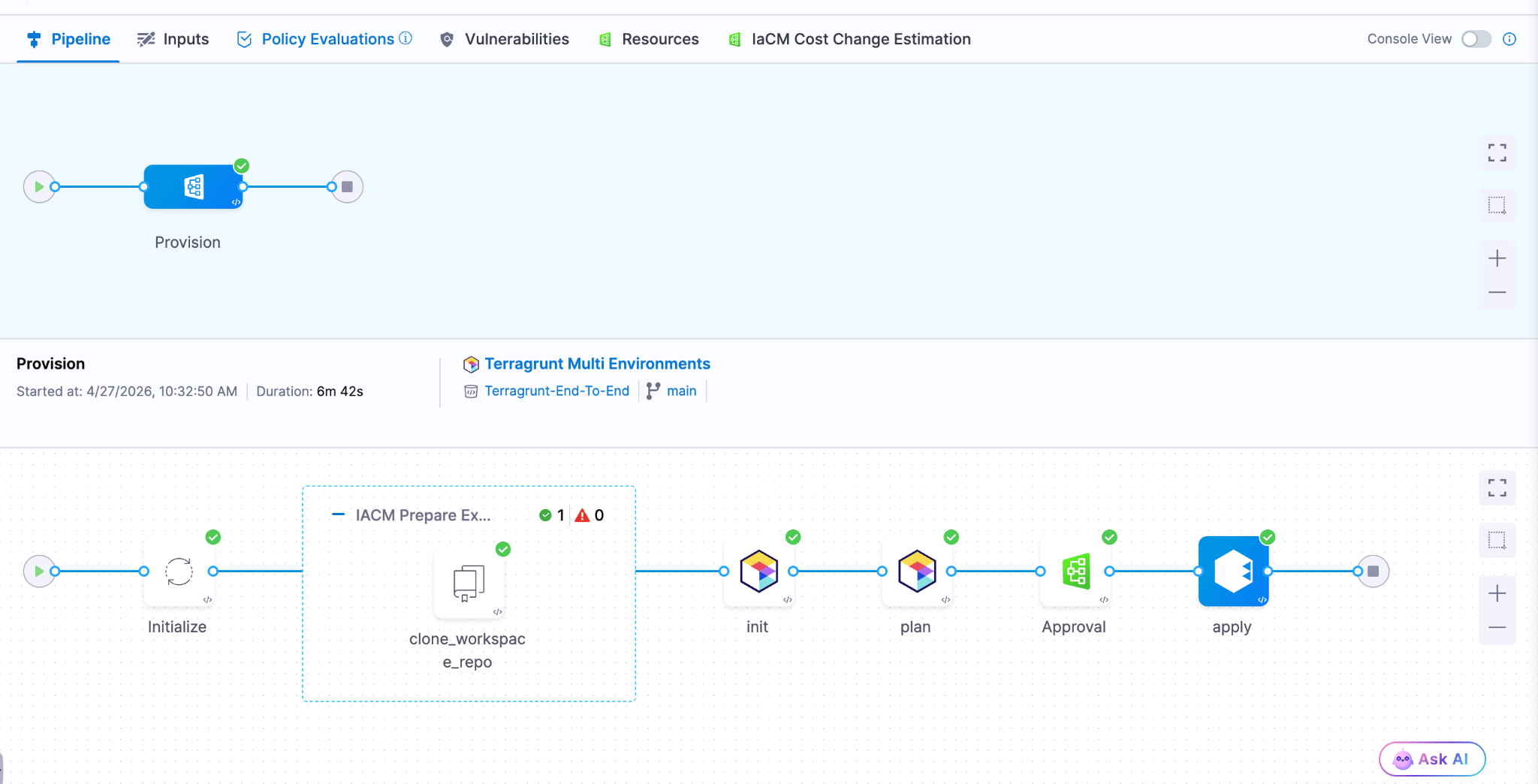
Today, we are excited to announce native Terragrunt support in Harness IaCM, bringing it to full parity with Terraform and OpenTofu while delivering capabilities that go beyond what is available in standalone tooling. This is more than support. It is about making Terragrunt a first-class platform for enterprise infrastructure management.
With Harness IaCM, teams can now:
- Orchestrate complex Terragrunt environments with full visibility across all units
- Apply cost estimation, approvals, and policy enforcement natively
- Detect and manage drift across environments with granular insights
- View infrastructure changes at the resource level across orchestrated deployments
Terragrunt has become a critical layer for managing infrastructure at scale because it simplifies how teams structure and reuse configurations across environments. Harness builds on that foundation with deep, native integration, enabling platform teams to operate with both flexibility and control.
This is especially important for enterprises where a single deployment spans multiple environments and services. Harness abstracts that complexity while maintaining governance, auditability, and consistency.
Extending IaCM to a Multi-IaC Future
Terragrunt is part of a broader shift toward multi-tool infrastructure strategies.
Modern teams are no longer standardized on a single IaC tool. Instead, they operate across:
- Terraform and OpenTofu for provisioning
- Terragrunt for orchestration
- CDK for developer-driven infrastructure
- Ansible for configuration and automation

This creates challenges around consistency, visibility, and governance. Harness IaCM is built for this reality. We are evolving IaCM into a unified control plane for multi-IaC workflows, where teams can manage different frameworks with a consistent experience, shared policies, and centralized visibility.
This means:
- Eliminating fragmented pipelines across tools
- Standardizing governance across environments
- Gaining full visibility into infrastructure state and changes
Instead of managing infrastructure in silos, teams can now operate from a single platform across the entire lifecycle.
What’s Next for Infrastructure as Code?
The next phase of Infrastructure as Code is not just about supporting more tools. It is about making infrastructure systems more intelligent and automated.
We are investing in two key areas:
Expanded IaC Support
We are continuing to support modern frameworks like AWS CDK, enabling developer-centric infrastructure workflows alongside provisioning, configuration, and orchestration tools.
AI-Driven Automation
We are introducing intelligence into IaC workflows to simplify tasks such as drift management and optimization. This helps teams reduce manual effort and operate more efficiently at scale.
Together, these investments move IaCM toward a unified, multi-IaC platform that combines flexibility, governance, and automation. Terragrunt has become essential for managing infrastructure at scale but until now, it hasn’t had a platform that truly supports it. As infrastructure continues to grow in complexity, our focus remains the same. Helping teams move faster, reduce risk, and scale with confidence no matter which IaC tools they use.
Latest Blogs


Harness Expands Infrastructure as Code Management with Native Terragrunt Support and Multi-IaC Innovation
- Harness IaCM introduces native Terragrunt support, enabling true enterprise-grade orchestration at scale.
- Teams can now manage Terraform, OpenTofu, and Terragrunt in a single platform without fragmented tooling.
- Built-in governance, policy enforcement, and approvals streamline secure infrastructure operations.
- End-to-end visibility and drift detection improve reliability across complex, multi-environment deployments.
- The launch marks a major step toward a unified, multi-IaC control plane for modern infrastructure teams.
Bringing First-Class Terragrunt Support to IaCM
“We’ve been operating in a hybrid environment with both OpenTofu and Terragrunt, and Harness has made it much easier to bring those workflows together into a single, consistent platform with IaCM. The addition of Terragrunt support is a valuable step toward simplifying how we manage infrastructure at scale.”
— Lead Platform Engineer, Enterprise Customer
Infrastructure as Code is now a standard for modern cloud operations, with most enterprises using IaC to provision and manage environments. However, as adoption grows, so does complexity. Teams are no longer managing a handful of environments. They are operating across multiple regions, accounts, and services, often at massive scale.
This is where traditional approaches begin to fall short.
As organizations scale their infrastructure, Terraform alone is often not enough. Teams adopt Terragrunt to manage complex, multi-environment deployments, but they are often forced to stitch together fragmented tooling that lacks visibility, governance, and consistency.
At Harness, we are changing that.
Today, we are excited to announce native Terragrunt support in Harness IaCM, bringing it to full parity with Terraform and OpenTofu while delivering capabilities that go beyond what is available in standalone tooling. This is more than support. It is about making Terragrunt a first-class platform for enterprise infrastructure management.
With Harness IaCM, teams can now:
- Orchestrate complex Terragrunt environments with full visibility across all units
- Apply cost estimation, approvals, and policy enforcement natively
- Detect and manage drift across environments with granular insights
- View infrastructure changes at the resource level across orchestrated deployments
Terragrunt has become a critical layer for managing infrastructure at scale because it simplifies how teams structure and reuse configurations across environments. Harness builds on that foundation with deep, native integration, enabling platform teams to operate with both flexibility and control.
This is especially important for enterprises where a single deployment spans multiple environments and services. Harness abstracts that complexity while maintaining governance, auditability, and consistency.
Extending IaCM to a Multi-IaC Future
Terragrunt is part of a broader shift toward multi-tool infrastructure strategies.
Modern teams are no longer standardized on a single IaC tool. Instead, they operate across:
- Terraform and OpenTofu for provisioning
- Terragrunt for orchestration
- CDK for developer-driven infrastructure
- Ansible for configuration and automation

This creates challenges around consistency, visibility, and governance. Harness IaCM is built for this reality. We are evolving IaCM into a unified control plane for multi-IaC workflows, where teams can manage different frameworks with a consistent experience, shared policies, and centralized visibility.
This means:
- Eliminating fragmented pipelines across tools
- Standardizing governance across environments
- Gaining full visibility into infrastructure state and changes
Instead of managing infrastructure in silos, teams can now operate from a single platform across the entire lifecycle.
What’s Next for Infrastructure as Code?
The next phase of Infrastructure as Code is not just about supporting more tools. It is about making infrastructure systems more intelligent and automated.
We are investing in two key areas:
Expanded IaC Support
We are continuing to support modern frameworks like AWS CDK, enabling developer-centric infrastructure workflows alongside provisioning, configuration, and orchestration tools.
AI-Driven Automation
We are introducing intelligence into IaC workflows to simplify tasks such as drift management and optimization. This helps teams reduce manual effort and operate more efficiently at scale.
Together, these investments move IaCM toward a unified, multi-IaC platform that combines flexibility, governance, and automation. Terragrunt has become essential for managing infrastructure at scale but until now, it hasn’t had a platform that truly supports it. As infrastructure continues to grow in complexity, our focus remains the same. Helping teams move faster, reduce risk, and scale with confidence no matter which IaC tools they use.


Infrastructure as Code Management: Terragrunt & Multi-IaC
What happens when your Infrastructure as Code management strategy works perfectly in dev, scales reasonably well in staging, and then quietly fractures across seventeen production workspaces because nobody documented which Terragrunt wrapper goes with which AWS account? You spend Friday afternoon reverse-engineering DRY patterns that made sense six months ago, wondering why your team is managing three different IaC execution engines with four incompatible workflow philosophies.
This scenario isn't hypothetical. It's the reality of organizations that adopted IaC incrementally, layer by layer, without a unified management approach. One team standardized on OpenTofu for new infrastructure. Another maintained legacy Terraform configurations because migration felt risky. A third discovered Terragrunt and used it to wrangle complexity across AWS regions, but now those wrappers exist outside any centralized governance model. Each decision was rational in isolation. Together, they created an orchestration problem masquerading as a tooling problem.
The actual challenge isn't choosing between Terraform, OpenTofu, or Terragrunt. It's managing their outputs, enforcing policy consistently across execution contexts, and ensuring that infrastructure changes don't outpace your ability to understand what's deployed.
The Hidden Complexity of Multi-IaC Environments
Most platform teams don't set out to run multiple IaC tools simultaneously. They inherit Terraform state from acquisitions, adopt OpenTofu for licensing predictability, and introduce Terragrunt because someone needed to stop copying backend configurations across 40 AWS accounts. The tools themselves aren't the problem. The problem is that each tool introduces its own state management assumptions, module resolution logic, and workflow expectations.
Terragrunt, for instance, exists specifically to solve Terraform's verbosity problem. It lets you define backend configurations once and reference them across environments. It supports dependency graphs so you can deploy a VPC before attempting to create subnets. These capabilities are valuable, but they also mean your actual infrastructure logic now spans two layers: the Terraform or OpenTofu code that defines resources, and the Terragrunt configuration that orchestrates execution.
When you lack centralized Infrastructure as Code management, those layers drift independently. Someone updates a Terragrunt dependency graph without realizing it breaks a downstream workspace. Another engineer modifies an OpenTofu module but forgets that three different Terragrunt configurations depend on its output structure. You don't discover these issues until a deployment fails in production, and the postmortem reveals that nobody had visibility into the full dependency chain.
Why Workflow Sprawl Defeats Governance at Scale
The typical response to multi-IaC complexity is to standardize on one tool and deprecate the others. That works if you're early in your IaC journey. It's impractical if you're managing hundreds of workspaces across regulated environments where compliance audits expect immutable infrastructure definitions and audit trails for every state change.
Here's what actually happens: platform teams create custom CI/CD pipelines for each tool. Terraform runs in Jenkins. OpenTofu runs in GitHub Actions. Terragrunt configurations use a shell script someone wrote during an incident. Each pipeline implements drift detection differently. Policy enforcement exists as scattered OPA rules that don't share a common evaluation context. When an auditor asks, "How do you prevent unapproved infrastructure changes?", the honest answer is, "We run some checks in some places, and we hope teams remember to use them."
This isn't negligence. It's what emerges when Infrastructure as Code management tooling doesn't natively support the reality of polyglot IaC environments. Teams need a system that treats OpenTofu, Terraform, and Terragrunt as execution details, not architectural boundaries. The workflow layer—plan generation, policy evaluation, approval gates, state locking—should remain consistent regardless of which engine interprets the configuration.
Infrastructure Automation Tools Need Orchestration, Not Just Execution
Running `terragrunt apply` successfully doesn't mean your infrastructure is well-managed. It means Terragrunt successfully invoked OpenTofu or Terraform and applied a configuration. The actual management work—validating inputs, enforcing cost policies, detecting drift, promoting changes through environments—exists outside the execution layer.
This is where most homegrown solutions collapse under their own weight. You build a wrapper script that runs Terragrunt with the right flags. Then you add pre-commit hooks for policy checks. Then you integrate Sentinel or OPA, but only for workspaces that someone remembered to configure. Then you add Slack notifications so people know when drift occurs, but the notifications don't include enough context to act on them. Eventually, you have a Rube Goldberg machine that works until it doesn't, and debugging requires institutional knowledge that exists in one person's head.
The fundamental issue is that IaC workflow optimization requires thinking beyond execution engines. You need orchestration that understands module dependencies, workspace relationships, and policy boundaries. You need variable management that doesn't require copying YAML files between repositories. You need drift detection that runs automatically and surfaces meaningful deltas, not raw Terraform output dumped into a log file.
Terragrunt Support as a First-Class Workflow Primitive
Treating Terragrunt as an afterthought—something teams bolt onto existing Terraform or OpenTofu pipelines—misses its architectural intent. Terragrunt exists because managing backend configurations, passing outputs between modules, and orchestrating multi-account deployments shouldn't require copying boilerplate across dozens of directories. When Infrastructure as Code management platforms support Terragrunt natively, they acknowledge this reality: the DRY principle applies to infrastructure orchestration, not just resource definitions.
Native Terragrunt support means the platform understands dependency graphs without requiring custom parsing logic. It means workspace templates can reference Terragrunt configurations directly, rather than forcing teams to flatten everything into monolithic Terraform modules. It means policy enforcement applies before Terragrunt invokes the underlying execution engine, catching invalid configurations before they generate failed plans.
This matters most in organizations running multi-region or multi-cloud architectures. A typical pattern: one Terragrunt configuration defines networking across AWS regions, another manages Kubernetes clusters, a third provisions databases. Each configuration depends on outputs from the others. Without native orchestration, teams either write brittle shell scripts to sequence these dependencies or accept that deployments sometimes fail halfway through because someone applied changes out of order.
Multi-IaC Tools Require Unified State and Policy Management
The real test of an Infrastructure as Code management platform isn't whether it runs OpenTofu or Terraform. It's whether it provides consistent state visibility, policy enforcement, and audit trails across both. If your platform requires separate workflows for each execution engine, you've automated the mechanics but not the governance.
Consider policy evaluation. A reasonable security requirement: no S3 buckets should allow public read access. With fragmented tooling, you implement this rule multiple times. Once for Terraform workspaces using Sentinel. Again for OpenTofu configurations using OPA. A third time for Terragrunt-managed infrastructure, where you're not sure which policy engine applies because Terragrunt is just orchestrating calls to Terraform or OpenTofu. When an audit occurs, you can't prove consistent enforcement because there's no unified policy evaluation layer.
The same fragmentation affects drift detection. Terraform Cloud detects drift for Terraform-managed resources. Your OpenTofu workspaces might run scheduled reconciliation jobs, or they might not—it depends on whether someone configured them. Terragrunt configurations drift silently unless you've built custom tooling to periodically run `terragrunt plan` and parse the output. The result: partial visibility across your infrastructure estate, where "managed by IaC" becomes aspirational rather than descriptive.
OpenTofu Integration and Terraform Alternatives in Practice
Organizations exploring Terraform alternatives often focus on licensing or community governance. Those considerations matter, but they don't address the operational question: how do you manage infrastructure deployed with multiple execution engines without creating parallel workflow systems?
OpenTofu integration means more than "we can run OpenTofu commands." It means workspaces provisioned for OpenTofu behave identically to Terraform workspaces at the orchestration layer. Variable sets apply consistently. Policy evaluation uses the same rule sets. Drift detection runs on the same schedule. Approval workflows follow the same governance model. The execution engine becomes an implementation detail, not a workflow boundary.
This distinction matters during migrations. Teams don't flip entire infrastructure estates from Terraform to OpenTofu overnight. They migrate incrementally, starting with non-critical workspaces and expanding as confidence grows. If your Infrastructure as Code management platform treats each engine as a separate silo, you're managing two parallel systems during the transition. If the platform abstracts execution details behind a unified orchestration layer, the migration becomes a configuration change, not an architectural overhaul.
IaC Orchestration Beyond Engine Selection
The hard problems in infrastructure management aren't technical; they're organizational. How do you ensure that 40 engineers across six teams follow the same approval process for production changes? How do you enforce cost policies without blocking legitimate deployments? How do you maintain audit trails that satisfy compliance requirements without turning every infrastructure change into a bureaucratic ordeal?
IaC orchestration platforms solve these problems by decoupling policy from execution. Instead of embedding governance rules in CI/CD pipelines—where they're invisible, untestable, and easy to bypass—you define them once at the platform level. Instead of writing custom scripts to sequence Terragrunt dependencies, you describe the dependency graph declaratively and let the platform handle execution order. Instead of building bespoke drift detection logic, you configure detection schedules and let the platform surface meaningful deltas.
This approach doesn't eliminate complexity. It consolidates complexity into a layer designed to manage it. Your IaC configurations remain simple: modules that define resources, Terragrunt wrappers that eliminate boilerplate, workspace configurations that specify execution context. The orchestration platform handles everything else: state locking, policy evaluation, approval workflows, audit logging, drift remediation.
Harness IaCM: Orchestration for Multi-IaC Environments
Harness Infrastructure as Code Management approaches these challenges by treating the execution engine as a deployment detail, not an architectural constraint. Whether you're running OpenTofu, Terraform, or Terragrunt, the orchestration layer remains consistent: standardized pipelines for plan generation and apply operations, unified policy enforcement across all workspaces, centralized drift detection that surfaces actionable insights.
- Native Terragrunt support means dependency graphs defined in Terragrunt configurations are understood and respected during execution. You don't need custom scripts to sequence deployments across modules or AWS accounts. The platform interprets dependencies and orchestrates execution accordingly, applying changes in the correct order while maintaining state consistency.
- The Module and Provider Registry provides a centralized source of truth for infrastructure components, whether they're Terraform modules, OpenTofu modules, or Terragrunt configurations. Variable Sets and Workspace Templates eliminate configuration duplication, letting you define environment-specific values once and reference them across workspaces. Default plan and apply pipelines ensure consistent execution patterns without requiring custom CI/CD configurations for each workspace.
- Policy enforcement happens before execution, not after. Whether you're using Terraform, OpenTofu, or Terragrunt, policies evaluate against the generated plan before any infrastructure changes occur. Drift detection runs automatically, comparing deployed infrastructure against IaC definitions and surfacing discrepancies through a unified interface. Audit trails capture every state change, policy evaluation, and approval decision, providing the compliance evidence required in regulated environments.
For teams managing infrastructure across multiple clouds, regions, or execution engines, Harness IaCM provides the orchestration layer that makes polyglot IaC environments manageable. The platform doesn't force you to standardize on a single tool. It provides governance, visibility, and workflow consistency regardless of which engine interprets your configurations.
Governance Enables Velocity in Multi-IaC Environments
The promise of Infrastructure as Code—reproducible deployments, version-controlled infrastructure, collaborative development—only materializes when you have consistent orchestration across execution engines. Running Terraform in one pipeline, OpenTofu in another, and Terragrunt through a shell script doesn't scale. It creates workflow fragmentation that defeats governance and slows teams down.
Effective Infrastructure as Code management platforms abstract execution details behind unified workflows. They treat Terragrunt as a first-class orchestration primitive, not an afterthought. They provide native support for OpenTofu alongside Terraform, recognizing that organizations migrate gradually, not overnight. Most importantly, they enforce policy, detect drift, and maintain audit trails consistently across all workspaces, regardless of which engine runs the actual infrastructure changes.
The technical lesson: orchestration complexity belongs in platforms designed to manage it, not scattered across custom scripts and fragmented CI/CD pipelines. The operational lesson: governance doesn't slow teams down when it's embedded in the workflow rather than bolted on afterward. Multi-IaC environments are manageable when you have the right orchestration layer. Without it, you're just running tools in parallel and hoping they don't conflict.
Explore how Harness Infrastructure as Code Management handles multi-IaC orchestration, or review the technical documentation or implementation details. The product roadmap outlines upcoming capabilities for workflow optimization and policy enforcement.


How to Install Terraform for Secure and Scalable Infrastructure Automation
- Setting up Terraform securely and consistently is essential for scaling your infrastructure and staying compliant.
- To achieve strong security, keep Terraform runs isolated, encrypt your state files and plans, and use lock files and trusted provider sources to ensure integrity.
- By automating Terraform setup and management in your CI/CD and GitOps pipelines, you keep versions consistent, speed up delivery, and stay compliant across many services.
- For enterprise teams, managing Terraform through an Infrastructure as Code Management tool, rather than standalone execution, ensures consistency, governance, and scalability.
If your Terraform install is insecure or inconsistent, it can quickly slow down your delivery. A single compromised file or a misconfigured backend can stop deployments for many services. Teams that set up Terraform correctly from the start can scale easily and avoid compliance issues.
The answer is to install Terraform with strong security measures right from the beginning. Use verified binaries, encrypt your state, and set up automated CI/CD integration from day one. This method includes OS-specific setup, security checklists, GitOps alignment, and governance that can grow with your company. Want to speed up secure infrastructure automation? Harness Infrastructure as Code Management offers AI-powered pipelines with built-in governance for enterprises.
Install Terraform Correctly on Every Platform: OS Prerequisites, Packages, and Verification
One misconfigured Terraform install can cause hours of pipeline failures across many services. When setting up Terraform on development machines, build agents, and production, focus on consistency and security for reliable automation. Start with verified binaries, pinned versions, and automated checks to keep your infrastructure stable.
Use Vendor-Backed Packages to Eliminate Supply Chain Risk
Always get Terraform from HashiCorp’s official repositories, not from third-party mirrors or unofficial packages. For macOS, use the official Homebrew tap (brew tap hashicorp/tap && brew install hashicorp/tap/terraform).
On Linux, add HashiCorp’s GPG-signed package repository instead of using versions from your distribution, which may be outdated. Windows users should download signed binaries directly from releases.hashicorp.com. This helps keep your infrastructure safe from compromised or outdated packages.
Pin Exact Versions and Verify SHA256 Checksums
To make builds reproducible, control the exact Terraform version in every environment. Download the specific version you need, such as from https://releases.hashicorp.com/terraform/1.6.0/terraform_1.6.0_linux_amd64.zip, and check the SHA256 checksum against HashiCorp’s signed SHASUMS file before extracting.
Keep your version-pinned install scripts in your infrastructure repository so teams can create identical environments. If you use Terraform with Harness, delegates manage versions for you, but local development still needs consistent versioning.
Automate Post-Install Verification to Prevent Configuration Drift
After installing Terraform, run terraform version to make sure the right version is active and in your PATH. Set up the plugin cache directory (TF_PLUGIN_CACHE_DIR) to avoid repeated provider downloads and check that you have write permissions.
Write a simple script to check the Terraform binary location, version, and basic provider setup. Run this script automatically in your CI/CD pipelines, container builds, and onboarding workflows to catch problems before they affect deployments. While local installation is useful for development, enterprise teams should standardize Terraform execution through an IaCM platform. This ensures consistent environments across developers, CI/CD pipelines, and production systems without relying on manual setup
Enterprise Security Hardening for Terraform Installation
Installing Terraform is only the beginning. In enterprise settings where you manage important infrastructure and need to meet regulations, hardening your Terraform setup turns a basic install into a system ready for production and governance. These controls are significantly easier to enforce when Terraform is managed through an IaCM platform that centralizes execution, credentials, and policy enforcement.
Credential Management and Execution Isolation:
- Run Terraform on dedicated build agents or through an IaCM platform that provides isolated, governed execution environments. Avoid putting long-term cloud credentials in developer profiles or local setups.
- Encrypt your Terraform plans by storing them in secrets managers instead of plain text files. This keeps sensitive infrastructure changes protected during the approval process.
Provider Security and Integrity:
- Use dependency lock files and private provider mirrors to control provider integrity. These steps enforce SHA256 checksum checks and stop unauthorized plugin downloads from public registries.
- Set up curated provider repositories with the Terraform providers mirror command. This creates trusted, version-controlled sources for your team, so you don’t have to rely on external registries in production.
State Management and Backend Security:
- Store your remote state in encrypted backends like S3 with KMS encryption. Set up bucket policies to limit access and turn on audit logging for all state changes.
- Set secure CLI defaults in your Terraform config files. This limits provider downloads to approved sources and blocks access to untrusted registries during runtime.
Automate Terraform Installation in CI/CD and GitOps Pipelines
Make your Terraform CI/CD setup consistent by including the binary in versioned container images or reusable templates that all services use. This prevents differences between developer machines, build agents, and production. This approach can become even more scalable when implemented through an IaCM tool integrated with your CI/CD platform where Terraform execution, policy checks, and governance are built into reusable workspaces and modules.
When updating Terraform versions or security patches, make changes in your template library instead of updating each pipeline one by one. We recommend this version-controlled method for enterprise customers.
Use Policy as Code checks to enforce governance by validating Terraform versions, approved modules, and provider rules before running any plans. OPA can review Terraform plans in your CI/CD pipeline, automatically approving safe changes and flagging risky ones for manual review.
Pair this with GitOps workflows, where pull requests start plans and approved merges triggers applies. This creates clear audit trails for compliance and keeps developers moving quickly. Instead of treating Terraform as a standalone CLI step, IaC tools allow you to manage infrastructure workflows as first-class citizens within your delivery pipelines.
Terraform Install FAQs: Security, Compliance, and Scale
DevOps teams running hundreds of services need Terraform installation methods that scale and stay secure and compliant. Here are practical answers to common questions from teams in regulated settings.
How do you install Terraform securely in an enterprise environment?
Start with package repositories that include GPG verification rather than direct binary downloads to prevent compromised or malicious software packages. Install from official HashiCorp repositories with signed packages, verify SHA256 checksums, and run Terraform from isolated build environments with limited-access credentials that only provide necessary permissions. Keep your state files in encrypted, secure storage with access controls and comprehensive audit logging.
What are the best practices for integrating Terraform installation with CI/CD pipelines?
Include Terraform in your container images with specific versions, or use custom binaries to keep all pipeline runs consistent. Pin exact builds in your pipeline templates and use policy-as-code to allow only approved releases before running plans. This keeps development and production in sync and maintains clear compliance records.
How can you automate Terraform installation for large-scale DevOps teams while meeting compliance requirements?
Make reusable install scripts that check checksums and pin builds, then share them through central config management or container registries. Use remote execution on dedicated infrastructure for security and audit trails. Apply OPA policies to control which Terraform releases and providers your teams can use.
Should you use local or remote Terraform execution for enterprise deployments?
Running Terraform remotely on dedicated infrastructure gives you better security and audit trails. Running it locally on developer machines can cause compliance and credential issues. Use isolated build environments or cloud-managed services that run Terraform plans with proper authentication and detailed logs for production. Even better, IaC platforms standardize this by enforcing remote execution with built-in security, auditability, and role-based access controls.
How do you maintain Terraform version consistency across multiple teams and services?
Set up golden path templates with pinned Terraform installs that update all services automatically. Distribute approved releases using container images or package managers, or use platforms that handle governance for you. IaC platforms automate this by centrally managing Terraform versions and enforcing them across all pipelines and environments.
From Installation to Enterprise Scale: Govern, Automate, and Evolve
Standardizing how you install Terraform sets the stage for everything else. Pinning versions, using verified binaries, and securing remote state help your teams work quickly and stay compliant. These best practices are the base for templates that scale to hundreds of services.
Once you have this foundation, the real benefits come when your install standards connect to automated pipelines and GitOps workflows. Using centralized templates and modules for Terraform means security updates are spread automatically, and developers keep their flexibility. Policy-as-code makes sure every deployment meets enterprise needs without slowing things down. At this stage, adopting an IaC Platform approach becomes the recommended path. By managing Terraform through platforms like Harness, teams can standardize execution, enforce governance, and scale infrastructure delivery without increasing operational overhead.”
Are you ready to move from manual installs to enterprise-level automation and governance? Harness Infrastructure as Code Management offers AI-powered templates, a central control plane, and automated checks to make your Terraform setup a real advantage.


What is Terragrunt and how does it simplify Terraform Workflows?
- Terragrunt significantly reduces operational complexity for enterprise teams by enabling DRY configuration, orchestrating multi-stack deployments, and standardizing remote state management across dozens of environments.
- While Terragrunt solves orchestration and consistency challenges at scale, it is best used in conjunction with a robust Continuous Delivery platform like Harness to achieve end-to-end governance, auditability, and automated release verification.
- Terragrunt is most valuable for organizations managing complex, multi-environment infrastructures, but can introduce unnecessary complexity for smaller teams or simple setups.
Managing Terraform across dozens of AWS accounts becomes a maintenance nightmare fast. Teams end up copy-pasting the same backend configurations, provider blocks, and variable definitions hundreds of times.
Terragrunt acts as an orchestrator above Terraform, eliminating this duplication through shared configuration inheritance and dependency management. When financial services teams manage 200+ microservices across multiple environments, these DRY patterns become essential for governance and consistency.
For regulated industries requiring strict audit trails and policy enforcement, understanding when Terragrunt pays off can mean the difference between scalable infrastructure and operational chaos. Harness Infrastructure as Code Management provides the enterprise control plane that orchestrates these complex, multi-stack deployments while maintaining the governance standards your organization demands.
What is Terragrunt?
Terragrunt is an open-source tool (built by Gruntwork) that runs Terraform for you, but with helpful superpowers:
- It reduces repeated Terraform code across environments (DRY).
- It makes it easier to manage remote state and locking consistently.
- It provides a clean pattern for multi-environment and multi-account setups.
- It can orchestrate running Terraform across many modules in dependency order.
At a high level, you keep writing normal Terraform modules (the .tf files you already know). Terragrunt adds a lightweight configuration file, typically terragrunt.hcl, that tells Terragrunt how to call Terraform for a given environment/module.
Think of Terraform as the engine, and Terragrunt as the driver who keeps you from taking wrong turns.
Why Terragrunt exists
Terraform is excellent at defining infrastructure, but large Terraform codebases tend to develop a few recurring issues.
1) Repeating the same config everywhere
Common examples:
- Repeating backend config (S3 bucket name, DynamoDB lock table, key path, region…)
- Repeating provider config patterns
- Repeating environment wiring (prod/staging/dev) for the same module
Terraform doesn’t let you parameterize everything the way you might want, and backend config in particular can get awkward (because backends are configured before variables load).
2) Keeping environments consistent
You want:
- Same module version pinned across environments
- Same state conventions
- Same tagging rules
- Same guardrails (like “don’t apply prod from your laptop at 2am”)
Terraform can do some of this with discipline and tooling, but Terragrunt makes consistency easier to enforce.
3) Running lots of Terraform in the right order
In real life, stacks are composed:
- Networking first (VPC/VNet)
- Then clusters/compute
- Then databases
- Then apps
Terraform can model dependencies within a root module, but if you split concerns into separate state files (common in large orgs), you need an orchestration system. Terragrunt helps you run multiple Terraform modules in dependency order.
How Terragrunt works (conceptually)
Terragrunt reads terragrunt.hcl, then:
- Creates a temporary working directory
- Pulls or references the Terraform module source you specify
- Injects inputs (variables), remote state config, and other settings
- Executes Terraform commands (init, plan, apply, etc.)
You still get standard Terraform behavior, plans, state, providers, and modules; Terragrunt just standardizes the how.
A typical Terragrunt layout separates:
- Reusable Terraform modules (pure Terraform, no env-specific stuff)
- Live configuration per environment (Terragrunt files that point to modules + pass inputs)
This separation alone is often the “aha” moment for teams.
Key features that make Terragrunt attractive
1) DRY configuration with inheritance
Terragrunt supports patterns where child configs inherit from parent configs.
For example:
- A root terragrunt.hcl might define remote state + common inputs.
- Environment-level config sets region/account specifics.
- Module-level config passes module-specific inputs.
This keeps your live environment folders small and readable.
2) Remote state made consistent (and less painful)
Remote state is not optional if you’re serious about Terraform in teams.
Terragrunt makes it easy to define remote state once and reuse it everywhere, including consistent naming conventions for state keys.
This matters because “remote state drift” (people making small differences between stacks) is one of the fastest ways to make infra harder than it needs to be.
3) Dependency handling between modules
Terragrunt can define dependencies between modules so you can:
- Apply foundational infra first
- Reference outputs from other modules cleanly
- Run “the whole stack” safely
This is especially helpful when you intentionally split state by domain (network, security, compute, etc.).
4) run-all orchestration
Terragrunt can run Terraform across multiple modules with commands like:
- terragrunt run-all plan
- terragrunt run-all apply
It will traverse your folder structure, respect dependencies, and execute in the right order.
Is that always the best approach? Not always (we’ll talk about that). But it’s very useful for bootstrapping or for teams that want controlled multi-module workflows.
5) Keeping Terraform modules clean
Terragrunt encourages a clean separation:
- Modules = reusable infrastructure building blocks
- Live config = environment wiring
That separation tends to improve module quality and reuse over time.
What Terragrunt is not (important expectations)
Terragrunt will not magically fix:
- Poor module design
- A lack of testing or review
- Unclear ownership of infrastructure
- Weak CI/CD practices
- Provider misconfigurations
It also doesn’t replace Terraform Cloud/Enterprise features like policy enforcement, run history UI, remote operations, etc. (though it can work alongside them depending on how you run Terraform).
Terragrunt is best thought of as a scaling tool for Terraform code organization and orchestration.
The disadvantages of Terragrunt
Before you adopt it, be honest about the costs.
1) Another tool to learn and maintain
Terragrunt uses HCL, so it feels familiar, but it’s still:
- Another CLI
- Another config layer
- Another set of conventions
New engineers must learn both Terraform and Terragrunt patterns in your repo.
2) Debugging can feel more indirect
When Terragrunt runs Terraform, it may:
- Generate temp directories
- Fetch modules dynamically
- Inject config you don’t see in your Terraform files
If someone is used to running Terraform directly inside a root module, the indirection can be confusing at first.
3) Repo structure becomes a “system”
Terragrunt shines with a consistent folder structure, but that also means your layout becomes a contract.
If teams disagree on structure or naming, Terragrunt can amplify friction.
4) run-all can be risky if you treat it like a hammer
Running everything everywhere is tempting. In large organizations, you generally want:
- Smaller blast radius
- Targeted changes
- Change windows and approvals for sensitive layers
Terragrunt can support disciplined workflows, but it can also enable “oops I applied 42 modules” if you don’t lock things down.
5) Terraform itself keeps improving
Terraform has evolved a lot, and tooling around Terraform has grown too (Terraform Cloud, wrappers, CI patterns, monorepo tooling). Some teams find that modern Terraform workflows reduce the need for Terragrunt, especially if they prefer fewer layers.
When is Terragrunt worth it
Terragrunt tends to be worth it when you check several of these boxes:
You have multiple environments and they’re getting repetitive
If you’ve got dev, staging, prod, and every change involves copying small differences across folders, Terragrunt’s DRY patterns can immediately pay off.
You manage multiple accounts/subscriptions/projects
If your infra spans:
- Multiple AWS accounts
- Multiple Azure subscriptions
- Multiple GCP projects
…Terragrunt can help standardize how each environment is wired and keep the “live” config manageable.
You want a clear split between modules and live configuration
If your Terraform code mixes reusable module logic with environment specifics, Terragrunt’s recommended pattern can make your repo cleaner, faster.
You intentionally split state into multiple components
If you keep separate state for networking, IAM, compute, and apps, Terragrunt’s dependency management and orchestration become genuinely useful.
Your team wants consistent conventions enforced by structure
If you want to enforce:
- how remote state is configured
- how modules are pinned
- how inputs are organized
Terragrunt provides a “pit of success” structure that helps teams do the right thing by default.
When Terragrunt might not be worth it
Terragrunt can be overkill when:
Your Terraform setup is small or stable
If you have a handful of root modules and only one environment, you’ll probably feel more overhead than benefit.
You rely heavily on Terraform Cloud/Enterprise workflows
If your whole workflow revolves around Terraform Cloud runs, policies, and UI-driven execution, you may prefer to keep things simple with native Terraform patterns.
You prefer “one root module per environment” and it’s working
Some teams keep a single root module per environment and use standard Terraform practices (workspaces or separate state) without orchestration. If that’s clean and disciplined, you might not need Terragrunt.
Your team is already tool-fatigued
Adding Terragrunt is a cultural choice as much as a technical one. If your org struggles with consistency or onboarding already, introducing another abstraction layer can slow you down.
A practical checklist: should we adopt it?
Here’s a quick decision framework you can use with your team.
Best practices if you do adopt Terragrunt
If you go for it, these practices reduce pain and increase payoff.
1) Keep Terraform modules pure
Avoid putting environment-specific assumptions inside modules. Let Terragrunt handle env wiring and inputs.
2) Pin module versions intentionally
Terragrunt makes it easy to point to a module source. Don’t leave it floating.
- Use version tags for git sources
- Use module registry versions where possible
3) Standardize state naming conventions early
Decide how state keys are formed and stick to it. Your future self will thank you.
4) Put guardrails around production
Examples:
- Require CI for prod applies
- Restrict who can run apply in prod directories
- Separate credentials and enforce least privilege
Terragrunt won’t do governance by itself, but it works well with governance.
5) Be careful with run-all apply
Use it deliberately:
- Great for bootstrapping or non-prod
- Use extra controls for prod
- Prefer targeted plans when possible
Terragrunt Frequently Asked Questions
Teams evaluating Terragrunt often have specific questions about when it adds value versus complexity. These answers focus on practical trade-offs, compliance implications, and common pitfalls that enterprise teams encounter.
What problems does Terragrunt solve that Terraform modules alone do not?
Terraform modules provide code reuse but don't address backend configuration duplication, cross-stack dependencies, or consistent CLI flag management. Terragrunt centralizes remote state configuration, orchestrates deployment order through dependency blocks, and eliminates repetitive variable files. It also enables immutable module promotion across environments using git refs, which modules alone cannot enforce.
How does Terragrunt impact security, compliance, and audit trails in regulated environments?
Building on these orchestration capabilities, Terragrunt standardizes remote state backends and locking mechanisms, reducing configuration drift that auditors identify as compliance risks. However, it doesn't provide built-in audit trails or policy enforcement. Teams need complementary tools like Harness governance features for OPA policies, RBAC, and immutable audit logs. Terragrunt's dependency orchestration can improve compliance by ensuring security groups deploy before applications.
When is Terragrunt overkill, and what are the common anti-patterns to avoid?
While Terragrunt solves important orchestration challenges, it adds unnecessary complexity for teams managing fewer than 10 environments or simple single-account setups. The most critical anti-pattern is multiple .terragrunt-cache directories causing disk bloat and operational friction. Teams also struggle with overly complex dependency chains that create deployment bottlenecks. Consider whether centralized orchestration tooling better serves your scaling needs.
Does Terragrunt replace the need for a continuous delivery platform?
Despite its orchestration strengths, Terragrunt handles infrastructure provisioning but lacks deployment verification, rollback automation, and release coordination across multiple services. Enterprise teams typically use Terragrunt for infrastructure provisioning within broader CD workflows. Platforms like Harness provide AI-powered verification, automated rollbacks, and release orchestration that Terragrunt cannot deliver alone.
How does Terragrunt integrate with existing GitOps workflows?
Recognizing these platform limitations, Terragrunt works well within GitOps by generating plan files and managing state through PR-driven workflows. However, teams often struggle with PR sprawl across environments and lack centralized visibility. Consider using an enterprise GitOps control plane to orchestrate Terragrunt execution, enforce policies, and provide unified dashboards across your entire GitOps estate while maintaining your existing ArgoCD investments.
Is Terragrunt Worth It? Practical Next Steps and How to Orchestrate at Scale
Terragrunt becomes worthwhile when you're managing infrastructure across dozens of environments and need standardized remote state, DRY inheritance, and cross-stack orchestration. The key benefits of using terragrunt for automated infrastructure deployment deliver maximum value at enterprise scale, when managing 66+ services manually takes more effort than adopting new automation patterns.
To get started, pilot in your non-production environment using a clear hierarchy for repo structure and promotion flows. Define your policies, audit controls, and SLOs before expanding across accounts. This approach reduces risk while proving value to stakeholders who need evidence before broader adoption.
Ready to orchestrate complex releases without the manual toil?, Harness Infrastructure as Code Management provides the enterprise control plane that complements your Terragrunt investments with AI-powered pipelines, automated verification, and policy-driven governance across your entire software delivery lifecycle.


Ansible vs Terraform Explained: Key Differences for Modern Infrastructure Automation
- Ansible and Terraform work well together. Terraform is best for setting up and managing infrastructure, while Ansible is great for configuration, orchestration, and ongoing operations.
- Using Ansible and Terraform together in managed GitOps workflows helps enterprise teams automate infrastructure at scale, keep records for audits, and meet compliance needs. This approach also removes manual steps and reduces configuration drift.
- Harness Continuous Delivery & GitOps offers a single, AI-powered control panel that manages both Terraform and Ansible. It brings together governance, visibility, and policy enforcement for complex deployment pipelines.
If DevOps teams mix up the roles of Ansible and Terraform, deployment pipelines can become unreliable. Manual handoffs slow down changes, and audits may find gaps where responsibilities overlap. Each tool solves different problems, so using them correctly avoids delays and compliance risks.
Are you dealing with scattered provisioning and configuration workflows? Harness Continuous Delivery offers an AI-powered control panel that manages both Terraform and Ansible, giving you unified visibility and policy enforcement.
Ansible vs Terraform: Core Concepts, Strengths, and Trade-Offs
Understanding the differences between Ansible and Terraform starts with recognizing that they solve complementary layers of infrastructure automation. Terraform excels at declaring and managing cloud resources, while Ansible shines at configuring the workloads that run on that infrastructure. Both tools are agentless and complement each other, but their architectural approaches and state-management philosophies yield distinct strengths and limitations.
Terraform: Declarative Provisioning and Lifecycle Management
Terraform specializes in infrastructure provisioning through declarative HashiCorp Configuration Language (HCL). It maintains a state file that tracks every resource it provisions, enabling planned changes and drift detection.
This stateful approach makes Terraform ideal for managing cloud resources like VPCs, databases, and Kubernetes clusters across multiple providers. Research shows Terraform's immutable infrastructure philosophy, replacing rather than modifying resources, reduces configuration drift and improves reproducibility at scale.
Ansible: Agentless Configuration and Orchestration
While Terraform sets up infrastructure, Ansible uses a task-based method with easy-to-read YAML playbooks run over SSH. Ansible does not keep a persistent state. Instead, it uses idempotent modules that give the same results no matter how many times you run them.
This makes Ansible a strong choice for configuring operating systems, deploying applications, and handling ongoing maintenance after the first setup. Studies describe Ansible as a tool for making changes directly on servers, which is useful for managing many machines at once.
State Management: Plans vs Push-Based Execution
The main difference between these tools is how they manage state. Terraform’s state file is the main record, letting you preview changes before making them. This setup helps detect drift and allows rollbacks using Infrastructure as Code tools.
On the other hand, Ansible sends configurations straight to target systems using idempotent tasks. This makes setup easier at first, but you need other ways to prevent drift and check changes in large environments.
Enterprise Scale: Governance and Visibility Matter
For large organizations, choosing the right tool is less important than having good governance and visibility. Using policy-as-code frameworks like Open Policy Agent, keeping audit trails, and using templates for consistency are all key.
Modern platforms provide GitOps control planes that orchestrate both Terraform provisioning and Ansible configuration within governed workflows, ensuring compliance without blocking developer productivity.
When to Choose Terraform for Provisioning at Scale
Terraform is best when you need to manage infrastructure across many cloud providers, environments, and teams. For large organizations with hundreds of services, using Terraform at scale helps ensure reliable and trackable infrastructure delivery.
- Set up cloud resources using Terraform’s plan-and-apply workflow. You can manage identity systems, VPCs, databases, Kubernetes clusters, and storage across AWS, Azure, and GCP. Any resource with an API can be managed as code.
- Enforce reusable standards through Terraform modules and registries that codify your organization's networking patterns, security baselines, and compliance requirements, preventing configuration drift across teams and regions.
- Organize workspaces by environment and team boundaries, following workspace best practices like separating stateful resources (databases) from volatile ones (compute) to minimize blast radius and enable safe parallel development.
- Use policy-as-code tools like OPA or Sentinel to automatically check resource settings, costs, and security before making any changes to production.
- Set up remote state management and deployment pipelines to track every infrastructure change from development to production. This creates permanent audit trails for compliance teams.
- Coordinate complex releases by integrating Terraform provisioning with GitOps workflows that can automatically create ephemeral environments, run verification tests, and promote successful changes across your infrastructure.
Ansible and Terraform Together in GitOps and CI/CD (2026 Best Practices)
The question of whether Ansible and Terraform can be used together has a clear answer: they work best as complementary layers in modern delivery pipelines. Define your cloud infrastructure with Terraform, then configure and orchestrate with Ansible, tying both to Git repositories and promotion workflows to reduce drift and manual handoffs. Terraform actions now support direct integration, enabling a single Terraform apply to dispatch Ansible Event-Driven Automation workflows while keeping inventories synchronized across both tools.
In practice, this setup works best when you use GitOps controllers like ArgoCD to deliver Kubernetes applications, while Terraform manages the clusters and cloud resources underneath.
This separation makes roles clear: Terraform sets up what you need, GitOps delivers your applications, and Ansible takes care of node setup, runbooks, and ongoing tasks that aren’t covered by Kubernetes.
For large organizations, centralize visibility and governance by using golden-path templates, OPA policy checks, and release management. This reduces manual work and helps keep compliance consistent.
Modern platforms solve Argo sprawl by offering a single control panel for managing multi-stage releases, enforcing policy-as-code, and keeping audit trails across all deployments. This helps teams deliver faster while keeping the governance needed for complex, regulated environments.
FAQ: Ansible vs Terraform for Enterprise DevOps Workflows
Enterprise teams managing hundreds of services often face complex decisions about when to use automated infrastructure setup versus hands-on system configuration. These frequently asked questions address practical concerns about combining both approaches while maintaining governance and visibility at scale.
What are the main differences between Ansible and Terraform for enterprise DevOps workflows?
Terraform excels at declarative infrastructure provisioning with state management and drift detection, making it ideal for cloud resources and lifecycle management. Ansible specializes in imperative system configuration, application deployment, and orchestration tasks across existing infrastructure. Air France-KLM successfully combined both, using Terraform for provisioning and Ansible for post-deployment setup, scaling to 7,200 workspaces supporting 450+ teams.
How do Ansible and Terraform compare for automating cloud infrastructure in 2026?
Terraform leads infrastructure provisioning with its declarative model and comprehensive cloud provider support, while Ansible remains the preferred choice for system configuration and Day 2 operations.
Which tool is better for CI/CD pipeline automation: Ansible or Terraform?
Both tools serve different pipeline stages rather than competing directly. Terraform handles infrastructure provisioning steps, while Ansible manages application setup and deployment tasks. Modern CI/CD platforms orchestrate both tools within unified pipelines, using failure strategies and conditional logic to coordinate Terraform applies followed by Ansible configuration runs based on environment and deployment context.
Can Ansible and Terraform be used together for scalable infrastructure management?
Yes, they work exceptionally well together. Enterprise teams typically use Terraform for infrastructure provisioning with S3-backed state management, followed by Ansible for OS setup and application installation. This separation of concerns enables teams to leverage each tool's strengths while maintaining clear boundaries between infrastructure lifecycle and system configuration responsibilities.
How should teams handle state, idempotence, and drift when combining Ansible and Terraform?
Terraform manages infrastructure state through remote backends with drift detection, while Ansible ensures idempotent system setup through declarative playbooks. Teams should establish clear ownership boundaries, use Terraform for stateful cloud resources, and leverage Ansible for application configuration that doesn't require persistent state tracking. Centralized GitOps platforms provide unified visibility across both tools' operations and drift detection.
What governance and compliance practices help standardize changes across 25+ clusters and 50+ repos?
Implement Policy as Code using Open Policy Agent (OPA) to enforce guardrails across both Terraform and Ansible workflows. Pre-written policy sets for compliance frameworks like NIST SP 800-53 accelerate adoption. Centralize policy management, use template-based approaches for consistency, and integrate policy checks into CI/CD pipelines to catch violations before deployment across distributed infrastructure.
From Tools to Outcomes: Standardize with Golden Paths and Governed GitOps
Choosing between Ansible and Terraform becomes simpler when you focus on outcomes rather than tools. Create golden-path templates that codify your Terraform provisioning and Ansible configuration processes together. Enforce OPA policies at every stage to maintain compliance without blocking developer velocity.
Meaningful scale happens when you centralize GitOps visibility to eliminate Argo sprawl across your infrastructure. Use AI to generate pipelines from natural language and automatically verify deployments with intelligent rollback capabilities. Start with one service, establish your workflow patterns, then propagate templates across all environments with automated governance that scales with your team.
Ready to move beyond manual pipeline creation and fragmented GitOps management? Harness Continuous Delivery transforms your Terraform and Ansible pipelines into AI-powered, policy-governed systems that deliver software faster and more securely.


Terraform Vendor Lock-In: How to Escape It
Did ecTerraform vendor lock-in just become your biggest operational risk without you noticing? When HashiCorp changed Terraform's license from MPL to BSL in August 2023, legal terms were not the only alteration. They fundamentally shifted the operational landscape for thousands of platform teams who built their infrastructure automation around what they believed was an open, community-driven tool. If your organization runs Terraform at scale, you're now facing a strategic decision that wasn't on your roadmap six months ago.
The uncomfortable truth is that most teams didn't architect for IaC portability. Why would they? Terraform was open source. It was the standard. And now, many organizations find themselves in a position they swore they'd never be in again after the Kubernetes wars: locked into a single vendor's roadmap, pricing model, and strategic priorities.
This isn't theoretical; it’s the very serious reality platform engineers are dealing with right now!
Why Terraform Lock-In Became Real Overnight
Terraform lock-in wasn't always a concern. For years, Terraform represented the opposite of vendor lock-in. It was open source, cloud-agnostic, and community-driven. Teams built entire operational models around it. They trained engineers, standardized on HCL, built module libraries, and integrated Terraform deeply into CI/CD pipelines. You’ve got to hand it to them; these aspects were very desirable.
Then HashiCorp moved to the Business Source License. Suddenly, the "open" in "open source" came with conditions. The BSL restricts certain commercial uses, and while many organizations technically fall outside those restrictions, the change introduced uncertainty.
- Could HashiCorp tighten the license further?
- Would future versions include features only available under commercial terms?
- What happens when your infrastructure automation depends on a tool whose strategic direction you no longer control?
The deeper problem is architectural. Most teams didn't design for IaC engine portability because they didn't need to. Terraform state files, provider interfaces, and workflow patterns became embedded assumptions. Module libraries assumed Terraform syntax. Pipelines called `terraform plan` and `terraform apply` directly. When every workflow is tightly coupled to a single tool's CLI and API, switching becomes expensive.
This is classic vendor lock-in, even if it happened gradually and without malice.
The Hidden Costs of Staying Locked In
The immediate cost of Terraform lock-in isn't the license itself, but rather related to what you can't do when you're locked in.
- You can't experiment with alternative IaC engines without rewriting modules.
- You can't adopt tools that might better suit specific use cases.
- You can't negotiate from a position of strength because your entire infrastructure automation stack depends on one vendor's roadmap.
If HashiCorp decides to sunset features, deprecate APIs, or introduce breaking changes, you either adapt or do without; stuck on an outdated version with mounting technical debt.
The operational risk compounds over time. When you're locked into a single IaC tool, you're also locked into its limitations. If drift detection isn't native, you build workarounds. If policy enforcement is bolted on, you maintain custom integrations. If the state backend causes performance issues at scale, you optimize around the bottleneck rather than solving the root problem.
And then there's the talent risk. If your team only knows Terraform, and the industry shifts toward other IaC paradigms, you're either retraining everyone or competing for a shrinking talent pool. Monocultures are fragile.
How to Escape Terraform Lock-In Without Rewriting Everything
The good news is that escaping Terraform lock-in doesn't require a full rewrite. It requires a deliberate strategy to introduce portability into your IaC architecture.
Start with OpenTofu as Your Baseline
OpenTofu emerged as the open-source fork of Terraform immediately after the license change. It's MPL-licensed, community-governed through the Linux Foundation, and API-compatible with Terraform 1.5.x. For most teams, OpenTofu migration is the lowest-friction path to regaining control over your IaC engine.
Migrating to OpenTofu doesn't mean abandoning your existing Terraform workflows. Because OpenTofu maintains compatibility with Terraform's core primitives, you can run OpenTofu side-by-side with Terraform during a transition. This lets you validate behavior, test edge cases, and build confidence before committing fully.
The strategic advantage of OpenTofu is not just licensing, optionality. Once you're no longer tied to HashiCorp's roadmap, you can evaluate IaC engines based on technical merit rather than sunk cost.
Decouple Your Workflows from Engine-Specific Assumptions
The harder part of escaping IaC vendor lock-in is decoupling your operational workflows from Terraform-specific patterns. This means abstracting your pipelines so they don't hardcode `terraform plan` and `terraform apply`. It means designing module interfaces that could theoretically support multiple engines. It means treating the IaC engine as an implementation detail rather than the foundation of your architecture.
This is where infrastructure as code portability becomes a design principle. If your pipelines call a generic "plan" and "apply" interface, switching engines becomes a simple configuration change, not a migration project.
Adopt Multi-IaC Tool Management from the Start
The reality is that most large organizations will eventually run multiple IaC tools. Some teams will use OpenTofu. Others will stick with Terraform for compatibility with existing state. New projects might adopt Terragrunt for DRY configurations or Pulumi for type-safe infrastructure definitions.
Fighting this diversity creates friction. Embracing it requires tooling that supports multi-IaC environments without forcing everyone into a lowest-common-denominator workflow. You need a platform that treats OpenTofu, Terraform, and other engines as first-class citizens, not as competing standards.
How Harness IaCM Enables Vendor-Neutral Infrastructure Management
Harness Infrastructure as Code Management was built to solve the multi-IaC problem that most teams are only now realizing they have. It doesn't force you to pick a single engine. It doesn't assume Terraform is the default. It treats OpenTofu and Terraform as equally supported engines, with workflows that abstract away engine-specific details while preserving the flexibility to use either.
This matters because escaping Terraform lock-in isn't just about switching tools. It's about building infrastructure automation that doesn't collapse the next time a vendor changes direction.
Harness IaCM supports OpenTofu and Terraform natively, which means you can run both engines in the same platform without maintaining separate toolchains. You get unified drift detection, policy enforcement, and workspace management across engines. If you're migrating from Terraform to OpenTofu, you can run both during the transition and compare results side-by-side.
The platform also supports Terragrunt, which means teams that have invested in DRY Terraform configurations don't have to throw away that work to gain vendor neutrality. You can keep your existing module structure while gaining the operational benefits of a managed IaC platform.
Beyond engine support, Harness IaCM addresses the systemic problems that make IaC vendor lock-in so painful. The built-in Module and Provider Registry means you're not dependent on third-party registries that could introduce their own lock-in. Variable Sets and Workspace Templates let you enforce consistency without hardcoding engine-specific logic into every pipeline. Default plan and apply pipelines abstract away the CLI layer, so switching engines doesn't require rewriting every workflow.
Drift detection runs continuously, which means you catch configuration drift before it becomes an incident. Policy enforcement happens at plan time, which means violations are blocked before they reach production. These aren't afterthoughts or plugins. They're native platform capabilities that work the same way regardless of which IaC engine you're using.
And because Harness IaCM is part of the broader Harness Platform, you can integrate IaC workflows with CI/CD, feature flags, and policy governance without duct-taping together disparate tools. This is the architectural model that makes multi-IaC tool management practical at scale.
Explore the Harness IaCM product or dive into the technical details in the IaCM docs.
The Path Forward: Portability as a Design Principle
Escaping Terraform lock-in is not about abandoning Terraform everywhere tomorrow. It's about regaining strategic control over your infrastructure automation. It's about designing for portability so that future licensing changes, roadmap shifts, or technical limitations don't force another painful migration.
The teams that will navigate this transition successfully are the ones that treat IaC engines as interchangeable components in a larger platform architecture. They're the ones that build workflows that abstract away engine-specific details. They're the ones that invest in tooling that supports multi-IaC environments without creating operational chaos.
If your organization is still locked into Terraform, now is the time to architect for optionality. Start by evaluating OpenTofu migration paths. Decouple your pipelines from engine-specific CLI calls. Adopt a platform that treats IaC engines as implementation details, not strategic dependencies.
Because the next time a vendor changes their license, you want to be in a position to evaluate your options, not scramble for a migration plan.
.png)
.png)
Build vs Buy IaC: Choosing the Right IaCM Strategy
Have you ever watched a “temporary” Infrastructure as Code script quietly become mission-critical, undocumented, and owned by someone who left the company two years ago? We can all related to a similar scenario, if not infrastructure-specific, and this is usually the moment teams realise the build vs buy IaC decision was made by accident, not design.
As your teams grow from managing a handful of environments to orchestrating hundreds of workspaces across multiple clouds, the limits of homegrown IaC pipeline management show up fast. It starts as a few shell scripts wrapping OpenTofu or Terraform commands often evolves into a fragile web of CI jobs, custom glue code, and tribal knowledge that no one feels confident changing.
The real question is not whether you can build your own IaC solution. Most teams can. The question is what it costs you in velocity, governance, and reliability once the platform becomes business-critical.
The Appeal and Cost of Custom IaC Pipelines
Building a custom IaC solution feels empowering at first. You control every detail. You understand exactly how plan and apply flows work. You can tailor pipelines to your team’s preferences without waiting on vendors or abstractions.
For small teams with simple requirements, this works. A basic OpenTofu or Terraform pipeline in GitHub Actions or GitLab CI can handle plan-on-pull-request and apply-on-merge patterns just fine. Add a manual approval step and a notification, and you are operational.
The problem is that infrastructure rarely stays simple.
As usage grows, the cracks start to appear:
- Governance gaps: Who is allowed to apply changes to production? How are policies enforced consistently? What happens when someone bypasses the pipeline and runs apply locally?
- State and workspace sprawl: Managing dozens or hundreds of state files, backend configurations, and locking behaviour becomes a coordination problem, not a scripting one.
- Workflow inconsistency: Each team builds its own version of “the pipeline.” What starts as flexibility turns into a support burden when every repository behaves differently.
- Security and audit blind spots: Secrets handling, access controls, audit trails, and drift detection are rarely first-class concerns in homegrown tooling. They become reactive fixes after something goes wrong.
At this point, the build vs buy IaC question stops being technical and becomes strategic.
What an IaCM Platform Is Actually Solving
We cannot simply label our infrastructure as code management platform as “CI for Terraform.” It exists to standardise how infrastructure changes are proposed, reviewed, approved, and applied across teams.
Instead of every team reinventing the same patterns, an IaCM platform provides shared primitives that scale.
Consistent Workspace Lifecycles
Workspaces are treated as first-class entities. Plans, approvals, applies, and execution history are visible in one place. When something fails, you do not have to reconstruct context from CI logs and commit messages.
Enforced IaC Governance
IaC governance stops being a best-practice document and becomes part of the workflow. Policy checks run automatically. Risky changes are surfaced early. Approval gates are applied consistently based on impact, not convention.
This matters regardless of whether teams are using OpenTofu as their open-source baseline or maintaining existing Terraform pipelines.
Centralised Variables and Secrets
Managing environment-specific configuration across large numbers of workspaces is one of the fastest ways to introduce mistakes. IaCM platforms provide variable sets and secure secret handling so values are managed once and applied consistently.
Drift Detection Without Custom Glue
Infrastructure drift is inevitable. Manual console changes, provider behaviour, and external automation all contribute. An IaCM platform detects drift continuously and surfaces it clearly, without relying on scheduled scripts parsing CLI output.
Module and Provider Governance
Reusable modules are essential for scaling IaC, but unmanaged reuse creates risk. A built-in module and provider registry ensures teams use approved, versioned components and reduces duplication across the organisation.
Why Building This Yourself Rarely Scales
Most platform teams underestimate how much work lives beyond the initial pipeline.
You will eventually need:
- Role-based access control.
- Approval workflows that vary by environment.
- Audit logs that satisfy compliance reviews.
- Concurrency controls and workspace locking.
- Safe ways to evolve pipelines without breaking dozens of teams.
None of these are hard in isolation. Together, they represent a long-term maintenance commitment. Unless building IaC tooling is your product, this effort rarely delivers competitive advantage.
How Harness IaCM Changes the Build vs Buy Equation
Harness Infrastructure as Code Management (IaCM) is designed for teams that want control without rebuilding the same platform components over and over again.
It supports both OpenTofu and Terraform, allowing teams to standardise workflows even as tooling evolves. OpenTofu fits naturally as an open-source execution baseline for new workloads, while Terraform remains supported where existing investment makes sense.
Harness IaCM provides:
- Default plan and apply pipelines that work out of the box.
- Workspace templates to enforce consistent backend configuration and governance.
- Module and provider registries to manage reuse safely.
- Policy enforcement, security checks, and cost visibility built directly into every run.
Instead of writing and maintaining custom orchestration logic, teams focus on infrastructure design and delivery.
Drift detection, approvals, and audit trails are handled consistently across every workspace, without bespoke scripts or CI hacks.
Making a Deliberate Build vs Buy IaC Decision
The build vs buy IaC decision should be intentional, not accidental.
If your organisation has a genuine need to own every layer of its tooling and the capacity to maintain it long-term, building can be justified. For most teams, however, the operational overhead outweighs the benefits.
An IaCM platform provides faster time-to-value, stronger governance, and fewer failure modes as infrastructure scales.
Harness Infrastructure as Code Management enables teams to operationalise best practices for OpenTofu and Terraform without locking themselves into brittle, homegrown solutions.
The real question is not whether you can build this yourself. It is whether you want to be maintaining it when the platform becomes critical.
Explore Harness IaCM and move beyond fragile IaC pipelines.


Terraform License Change: BSL vs Open Source Guide
Picture this. What should have been a routine Infrastructure as Code upgrade suddenly triggers a legal review, a compliance escalation, and an awkward platform meeting nobody planned for. Just the kind of chain reaction the Terraform license change set off for many teams, often long after the technical work was already done.
When HashiCorp announced its move from the Mozilla Public License v2.0 (MPL 2.0) to the Business Source License (BSL) in August 2023, the reaction extended beyond ‘just noise’ pretty quickly. It exposed how deeply Terraform had been assumed to be “safe, open, and predictable” infrastructure glue. Overnight, teams who thought they were managing purely technical risk found themselves pulled into licensing discussions they were never set up to handle.
The question quickly shifted from what changed to what does this mean for how we run infrastructure going forward?
Understanding the Terraform BSL License and What Changed
Before August 2023, Terraform’s open source MPL 2.0 license allowed broad reuse, modification, and redistribution, including for commercial services. This model made Terraform an easy default for internal platforms, consultancies, and SaaS providers building IaC-powered offerings. It removed friction, and over time, that frictionless adoption became an assumption.
The Business Source License changes that calculus. Under the Terraform BSL license, use is still permitted for many internal scenarios, but explicitly restricted when Terraform is used to build competing commercial services. That distinction matters more than it first appears.
If you are:
- Operating an internal platform team offering IaC as a shared service.
- Running managed infrastructure for customers.
- Embedding Terraform into a commercial product.
You are no longer operating in a clearly open space.
The HashiCorp license change paired legal challenges with uncertainty. Legal and compliance teams dislike ambiguity, and infrastructure teams rarely want to be the ones explaining why a core automation tool might fall into a gray area six months from now.
This is the context in which the BSL vs open source discussion actually matters: not ideology, but operational predictability.
OpenTofu vs Terraform: Why an Open Baseline Matters
In response to the license change, the community did what it has done many times before: it forked. OpenTofu emerged as a continuation of the last MPL-licensed Terraform release, governed under the Linux Foundation with an explicit commitment to open, community-driven development.
From a practical perspective, OpenTofu started life as a drop-in replacement. Existing configurations, state files, providers, and modules continued to work. That was intentional.
The goal was continuity without legal ambiguity.
Now, you and your team might ask, what makes OpenTofu compelling aside from feature novelty? And the biggest factor is governance clarity. OpenTofu provides an open source IaC tool whose roadmap, licensing, and contribution model are not tied to a single vendor’s commercial strategy. For organizations designing or evolving IaC platforms today, that matters…a lot.
Terraform, meanwhile, remains a powerful and widely adopted tool, particularly for teams already invested in Terraform Cloud or enterprise workflows. But its direction is now explicitly commercial-first. That does not make it wrong, but it does mean it is no longer the neutral baseline it once was.
This distinction is subtle but important. OpenTofu increasingly represents the default open path, while Terraform becomes a contextual choice driven by existing investment rather than long-term openness.
Common Pitfalls When Evaluating Terraform Alternatives
One of the biggest mistakes teams make after the Terraform license change is treating the decision as a simple binary swap. Replace the binary, update a few pipelines, move on. That approach works briefly, and then fails in production.
Migrating from Terraform requires more than CLI compatibility:
- Provider versions need validation.
- Module registries need auditing.
- State backends and locking mechanisms must be reviewed.
- CI/CD pipelines often hardcode assumptions that surface only under load.
Another common misstep is assuming ecosystem maturity is static. Terraform benefits from years of accumulated modules and institutional knowledge. OpenTofu is closing that gap quickly, but teams still need to inventory dependencies rather than assume universal parity.
Finally, many organizations ignore hybrid reality. Running OpenTofu for new workloads while maintaining Terraform for legacy environments is often the most pragmatic approach. The risk comes not from using both tools, but from managing them inconsistently.
Infrastructure as Code Licensing Is Now a Platform Concern
The Terraform license change highlighted a broader shift: infrastructure as code licensing is no longer a background concern. It is part of your platform architecture.
Infrastructure teams now have to think about:
- How licensing choices affect downstream products and services.
- Whether tooling decisions introduce future renegotiation risk.
- How easily execution engines can be swapped if assumptions change again?
This is where open source IaC tools regain their appeal. Not because they are “better,” but because they reduce surprise.
How Harness IaCM Supports OpenTofu and Terraform Without Lock-In
Regardless of where you land in the OpenTofu vs Terraform discussion, the operational challenge remains the same: running infrastructure changes safely, consistently, and with governance across teams.
Harness Infrastructure as Code Management (IaCM) is designed to absorb this kind of tooling evolution. It supports both OpenTofu and Terraform while treating the execution engine as an implementation detail rather than a strategic constraint.
With Harness IaCM:
- Module and Provider Registry standardizes reusable components across teams.
- Variable Sets and Workspace Templates ensure consistency without duplication.
- Default plan and apply pipelines enforce review, policy, and approval flows by default.
This approach allows teams to adopt OpenTofu where openness and governance matter most, while continuing to support Terraform where existing investment justifies it. Drift detection and policy enforcement apply uniformly, regardless of which tool is executing the plan.
Rather than forcing an immediate migration, Harness IaCM enables controlled evaluation and gradual transition, reducing the risk that licensing decisions fragment your platform.
Summary: Make Licensing a Design Decision, Not a Surprise
The Terraform license change was a reminder that infrastructure tooling choices have consequences beyond syntax and state files. The BSL vs open source distinction affects governance, risk tolerance, and long-term platform flexibility.
OpenTofu provides a clear open baseline for teams who want to avoid licensing ambiguity going forward. Terraform remains relevant, especially where commercial tooling is already embedded. The key is designing your platform so that this choice does not become a single point of failure.
Harness Infrastructure as Code Management helps teams do exactly that. By supporting both OpenTofu and Terraform with consistent workflows and guardrails, it allows organizations to adapt without disruption.
The question is no longer which tool you prefer. It is whether your infrastructure platform can handle change when the rules shift again.
Explore Harness IaCM and design your IaC workflows for flexibility, not assumptions.
Check out the Terraform to OpenTofu migration to bring this flexibility into play and take back control of your infrastructure.
Infrastructure Guardrails: Why Your IaC Stack Needs Them
Have you ever asked yourself, what is the fastest way to turn a harmless Infrastructure as Code change into a production incident and an awkward postmortem? We did, and found that usually, it's from letting it through without any guardrails.
Infrastructure guardrails in Infrastructure as Code (IaC) were once a nice-to-have. Today, they’re essential. Without clear boundaries and safety mechanisms, even well-designed IaC workflows can turn small mistakes into fast-moving, high-impact problems.
What Are Infrastructure Guardrails?
Infrastructure guardrails are preventive controls that help teams standardize and secure infrastructure deployments. They act as a safety net, ensuring changes consistently align with organizational policies, security best practices, and compliance requirements.
Think of infrastructure guardrails as the difference between letting developers drive on an open road with no lanes versus providing clear lane markings, speed limits, and crash barriers. Guardrails do not restrict innovation. They make it safe to move fast without losing control.
Why Infrastructure Guardrails Are Critical for Modern Cloud Operations
As organizations adopt cloud-native practices and infrastructure as code becomes the standard for deployment, the complexity and scale of infrastructure management increases exponentially. Here's why infrastructure guardrails have become non-negotiable:
Prevent Costly Mistakes
Without proper infrastructure guardrails, simple human errors can result in significant outages or security incidents. Consider these common scenarios:
- A developer accidentally provisions oversized instances across multiple regions
- Security groups are incorrectly configured, exposing sensitive services to the public internet
- Production environments are modified during testing due to misconfigured workspace variables
Each of these scenarios can lead to substantial financial impact, from unexpected cloud bills to costly security breaches and downtime. Infrastructure guardrails help prevent these issues before they manifest in your environment.
Enforce Infrastructure as Code Best Practices
Infrastructure guardrails ensure teams follow infrastructure as code best practices consistently. These include:
- Standardizing resource naming conventions
- Ensuring all resources have required tags for cost allocation
- Enforcing module versioning to prevent unexpected changes
- Requiring documentation for infrastructure components
When these practices are enforced through guardrails rather than through documentation alone, teams naturally develop better habits while reducing technical debt.
Key Types of Infrastructure Guardrails Your Stack Needs
Policy-Based Infrastructure Guardrails
Policy-based guardrails enforce rules across your entire infrastructure. Tools like Open Policy Agent (OPA) integrate with OpenTofu and Terraform to validate infrastructure changes against organizational policies before deployment.
These policies can be as simple or complex as needed:
Policy-based infrastructure guardrails provide the flexibility to codify any organizational requirement while ensuring consistent enforcement.
Compliance Controls
Both OpenTofu and Terraform benefit from specific guardrails that enhance their native capabilities:
- Module Registry Controls: Ensuring teams use only approved, tested modules from internal registries
- Variable Validation: Preventing deployments with invalid or potentially dangerous input values
- Custom Policy Frameworks (OpenTofu): Enforcing business and security rules
OpenTofu compliance controls can be particularly effective when integrated into CI/CD pipelines, creating automated checkpoints that validate changes before they reach production environments.
Infrastructure Drift Prevention
One of the most insidious challenges in infrastructure management is configuration drift. Without proper infrastructure guardrails, manual changes can occur outside the IaC workflow, creating inconsistencies between your code and the actual deployed resources.
Effective drift prevention guardrails include:
- Regular automated drift detection scans
- Remediation workflows that reconcile detected drift
- Prevention of manual changes through access controls
- Alerting systems that notify teams when drift occurs
Implement IaC Security Controls Within Your Guardrails
Infrastructure guardrails should incorporate robust IaC security controls to protect against both accidental and malicious security issues:
- Static Code Analysis: Scan IaC templates for security misconfigurations before deployment
- Secrets Management: Prevent hardcoded credentials in infrastructure code
- Least Privilege Enforcement: Ensure IAM roles and permissions follow principle of least p
- Network Security Validation: Verify that network configurations don't create unintended exposure
These security-focused infrastructure guardrails help organizations maintain a strong security posture even as infrastructure scales and evolves.
Cloud Infrastructure Governance Through Effective Guardrails
For organizations operating at scale, infrastructure guardrails form the foundation of cloud infrastructure governance. This governance framework provides:
- Visibility into all infrastructure resources across environments
- Accountability through detailed audit trails of changes
- Cost management through enforcement of resource constraints
- Compliance with industry regulations and internal policies
How Harness IaCM Enhances Your Infrastructure Guardrails
Harness Infrastructure as Code Management (IaCM) provides a comprehensive platform for implementing and maintaining effective infrastructure guardrails. Supporting both OpenTofu and Terraform, Harness IaCM addresses the challenges we've discussed through several key capabilities:
Built-in Policy Enforcement
Harness IaCM integrates policy-as-code directly into your infrastructure workflows. Teams can define, test, and enforce policies that validate infrastructure changes against security, compliance, and operational requirements. These policies run automatically during the plan phase, preventing non-compliant changes from being applied.
Standardization Through Module and Provider Registry
Harness IaCM includes a built-in registry for OpenTofu and Terraform modules and providers. This enables teams to:
- Publish approved, pre-validated infrastructure components
- Version modules to ensure controlled changes
- Share reusable components across teams with appropriate guardrails already built in
This standardization dramatically reduces the risk of configuration errors while improving developer productivity.
Controlled Deployment Workflows
With Harness IaCM, infrastructure deployments follow consistent, auditable workflows:
- Changes are proposed through version control
- Infrastructure guardrails validate the changes through policy enforcement
- Approvals are routed to appropriate stakeholders based on impact
- Deployments proceed only after all guardrails have been satisfied
These workflows provide the perfect balance between developer autonomy and operational control.
Drift Detection and Remediation
Harness IaCM continuously monitors your infrastructure for drift, automatically detecting when resources deviate from their expected state. When drift occurs, teams can:
- Receive immediate notifications
- Visualize exactly what changed
- Automatically remediate drift by reapplying the correct configuration
This ensures your infrastructure guardrails remain effective even after deployment.
Get Started with Infrastructure Guardrails
Implementing effective infrastructure guardrails doesn't have to be an all-or-nothing proposition. Start with these steps:
- Identify your highest-risk areas: Begin with guardrails that protect against your most common or costly errors
- Start with simple policies: Focus on basic security and cost management policies before adding complexity
- Integrate guardrails into your existing workflow: Use tools like Harness IaCM that work with your current processes
- Measure the impact: Track reduced incidents, faster deployments, and improved compliance
Conclusion: Infrastructure Guardrails as Enablers, Not Barriers
Effective infrastructure guardrails don't limit innovation, they enable it by providing a safe environment for experimentation and rapid deployment. By preventing costly errors, enforcing best practices, and ensuring compliance, guardrails give teams the confidence to move quickly without sacrificing reliability or security.
Harness Infrastructure as Code Management provides the ideal platform for implementing these guardrails, with native support for both OpenTofu and Terraform, built-in policy enforcement, and comprehensive drift management capabilities.
Ready to implement effective infrastructure guardrails in your environment? Explore how Harness IaCM can help your team deploy more confidently and securely while maintaining the flexibility developers need to innovate.


How Enterprises Modernize and Migrate to the Cloud Safely with Harness Automation
Cloud Migration Series | Part 1
Cloud migration has shifted from a tactical relocation exercise to a strategic modernization program. Enterprise teams no longer view migration as just the movement of compute and storage from one cloud to another. Instead, they see it as an opportunity to redesign infrastructure, streamline delivery practices, strengthen governance, and improve cost control, all while reducing manual effort and operational risk. This is especially true in regulated industries like banking and insurance, where compliance and reliability are essential.
This first installment in our cloud migration series introduces the high-level concepts and the automation framework that enables enterprise-scale transitions, without disrupting ongoing delivery work. Later entries will explore the technical architecture behind Infrastructure as Code Management (IaCM), deployment patterns for target clouds, Continuous Integration (CI) and Continuous Delivery (CD) modernization, and the financial operations required to keep migrations predictable.

Cloud Migration Is Broader Than Most Organizations Expect
Many organizations begin their migration journey with the assumption that only applications need to move. In reality, cloud migration affects five interconnected areas: infrastructure provisioning, application deployment workflows, CI and CD systems, governance and security policies, and cost management. All five layers must evolve together, or the migration unintentionally introduces new risks instead of reducing them.
Infrastructure and networking must be rebuilt in the target cloud with consistent, automated controls. Deployment workflows often require updates to support new environments or adopt GitOps practices. Legacy CI and CD tools vary widely across teams, which complicates standardization. Governance controls differ by cloud provider, so security models and policies must be reintroduced. Finally, cost structures shift when two clouds run in parallel, which can cause unpredictability without proper visibility.
Why Enterprises Pursue Cloud-to-Cloud Migration
Cloud migration is often motivated by a combination of compliance requirements, access to more suitable managed services, performance improvements, or cost efficiency goals. Some organizations move to support a multi-cloud strategy while others want to reduce dependence on a single provider. In many cases, migration becomes an opportunity to correct architectural debt accumulated over years.
Azure to AWS is one example of this pattern, but it is not the only one. Organizations regularly move between all major cloud providers as their business and regulatory conditions evolve. What remains consistent is the need for predictable, auditable, and secure migration processes that minimize engineering toil.
Challenges That Slow Down Enterprise Migration
The complexity of enterprise systems is the primary factor that makes cloud migration difficult. Infrastructure, platform, security, and application teams must coordinate changes across multiple domains. Old and new cloud environments often run side by side for months, and workloads need to operate reliably in both until cutover is complete.
Another challenge comes from the variety of CI and CD tools in use. Large organizations rarely rely on a single system. Azure DevOps, Jenkins, GitHub Actions, Bitbucket, and custom pipelines often coexist. Standardizing these workflows is part of the migration itself, and often a prerequisite for reliability at scale..
Security and policy enforcement also require attention. When two clouds differ in their identity models, network boundaries, or default configurations, misconfigurations can easily be introduced . Finally, cost becomes a concern when teams pay for two clouds at once. Without visibility, migration costs rise faster than expected.
How Harness Provides Structure and Control for Cloud Migration
Harness addresses these challenges by providing an automation layer that unifies infrastructure provisioning, application deployment, governance, and cost analysis. This creates a consistent operating model across both the current and target clouds.
Harness Internal Developer Portal (IDP) provides a centralized view of service inventory, ownership, and readiness, helping teams track standards and best-practice adoption throughout the migration lifecycle. Harness Infrastructure as Code Management (IaCM) defines and provisions target environments and enforces policies through OPA, ensuring every environment is created consistently and securely. It helps teams standardize IaC, detect drift, and manage approvals. Harness Continuous Delivery (CD) introduces consistent, repeatable deployment practices across clouds and supports progressive delivery techniques that reduce cutover risk. GitOps workflows create clear audit trails. Harness Cloud Cost Management (CCM) allows teams to compare cloud costs, detect anomalies, and govern spend during the transition before costs escalate.
A High-Level Migration Blueprint for Enterprises
A successful, low-risk cloud migration usually follows a predictable pattern. Teams begin by modeling both clouds using IaC so the target environment can be provisioned safely. Harness IaCM then creates the new cloud infrastructure while the existing cloud remains active. Once environments are ready, teams modernize their pipelines. This process is platform agnostic and applies whether the legacy pipelines were built in Azure DevOps, Jenkins, GitHub Actions, Bitbucket, or other systems. The new pipelines can run in parallel to ensure reliability before switching over.
Workloads typically migrate in waves. Stateless services move first, followed by stateful systems and other dependent components. Parallel runs between the source and target clouds provide confidence in performance, governance adherence, and deployment stability without slowing down release cycles. Throughout this process, Harness CCM monitors cloud costs to prevent unexpected increases. After the migration is complete, teams can strengthen stability using feature flags, chaos experiments, or security testing.

Expected Outcomes for Technology Leaders
When migration is guided by automation and governance, enterprises experience fewer failures and smoother transitions, and faster time-to-value. Timelines become more predictable because infrastructure and pipelines follow consistent patterns. Security and compliance improve as policy enforcement becomes automated. Cost visibility allows leaders to justify business cases and track savings. Most importantly, engineering teams end up with a more modern, efficient, and unified operating model in the target cloud.
What Comes Next
The next blog in this series will examine how to design target environments using Harness IaCM, including patterns for enforcing consistent, compliant baseline configurations. Later entries will explore pipeline modernization, cloud deployment patterns, cost governance, and reliability practices for post-migration operations.
Terraform Variable Management at Scale: Centralizing IaC with Variable Sets and Provider Registry in Harness IaCM
Infrastructure as Code (IaC) has made provisioning infrastructure faster than ever, but scaling it across hundreds of workspaces and teams introduces new challenges. Secrets get duplicated. Variables drift. Custom providers become hard to share securely.
That’s why we’re excited to announce two major enhancements to Harness Infrastructure as Code Management (IaCM):
Variable Sets and Provider Registry built to help platform teams standardize and secure infrastructure workflows without slowing developers down.
Variable Sets: Centralized Configuration Without the Chaos
Variables in Infrastructure as Code store configuration values like credentials and environment settings so teams can reuse and customize deployments without hardcoding. However, once teams operate dozens or hundreds of workspaces, variables quickly become fragmented and hard to govern. Variable Sets provide a single control plane for configuration parameters, secrets, and variable files used across multiple workspaces. In large organizations, hundreds of Terraform or OpenTofu workspaces share overlapping credentials and configuration keys such as Terraform variable sets or OpenTofu variable sets. Traditionally, these are duplicated, making credential rotation, auditing, and drift prevention painful.
Harness IaCM implements Variable Sets as first-class resources within its workspace model that are attachable at the account, organization, or project level. The engine dynamically resolves variable inheritance based on a priority ordering system, ensuring the highest-priority set overrides conflicting keys at runtime.
.png)
Core Capabilities
- Hierarchical Inheritance Graph: Workspaces resolve variables based on an explicit priority order defined by the platform team, with the highest-priority Variable Set taking precedence. Conflicts are clearly surfaced in the UI, showing overridden values and the exact source of each variable.
- Type and Scope Support: Handles both regular key-value pairs and .tfvars files. Variables can reference Harness Connectors (e.g., Vault or AWS Secrets Manager) for secure retrieval at execution. Both Terraform variable sets and OpenTofu variable sets can also be attached to Workspace Templates.
- Change Propagation: When a variable changes, Harness automatically lists all affected workspaces via reference tracking, allowing controlled rollouts or bulk updates.
- Access Control and Auditing: Only users with workspace edit permissions can change precedence; future RBAC plans extend granular edit and view rights. Every modification is recorded in IaCM audit logs.
- Runtime Execution: Conflict resolution occurs at Terraform runtime for variable files but design-time for inline variables giving predictable behavior and faster validation.
For enterprises running hundreds of Terraform workspaces across multiple regions, Variable Sets give platform engineers a single, authoritative home for Vault credentials. When keys are rotated, every connected workspace automatically inherits the update by eliminating manual edits, reducing risk, and ensuring compliance across the organization. It’s a fundamental capability for terraform variable management at scale.
Provider Registry: Secure Distribution for Custom Providers
Provider Registry introduces a trusted distribution mechanism for custom Terraform registry and OpenTofu provider registry. While the official Terraform registry and OpenTofu Provider Registry caters to public providers, enterprise teams often build internal providers to integrate IaC with proprietary APIs or on-prem systems. Managing these binaries securely is non-trivial.
Harness IaCM solves this with a GPG-signed, multi-platform binary repository that sits alongside the Module Registry under IaCM > Registry. Each provider is published with platform-specific artifacts (macOS, Linux, Windows), SHA256 checksums, and signature files.
.png)
Core Capabilities
- Integration with Policy as Code: Platform teams can enforce which providers are allowed within configurations using OPA-based policy checks in the pipeline.
- Secure by Default: Each provider binary is signed with a GPG key and verified during download to prevent tampering.
- Cross-Platform Resolution: At tofu init or terraform init, Harness detects the OS/architecture and automatically delivers the correct binary without manual setup.
- Version Consistency: Strict semantic version matching (v1.0.0 ≠ v1.0.1) prevents runtime mismatches and enforces dependency integrity
- Faster Internal Integrations: Publish internal APIs or custom integrations as reusable providers.
- No Manual Management: Developers can seamlessly use approved providers directly in configurations without managing binaries locally.
For any enterprise teams that build a custom provider to integrate OpenTofu with their internal API. Using Harness Provider Registry, they sign and publish binaries for multiple platforms. Developers simply declare the provider source in code, Harness handles signature verification, delivery, and updates automatically. Together with the Module Registry and Testing for Modules, Provider Registry completes the picture for trusted, reusable infrastructure components helping organizations scale IaC with confidence.
Why These Features Matter
Harness IaCM already provides governed-by-default workflows with centralized pipelines, policy-as-code enforcement, and workspace templates that reduce drift. Now, with Variable Sets and Provider Registry, IaCM extends that governance deeper into how teams manage configuration and custom integrations. These updates make Harness IaCM not just a Terraform or OpenTofu orchestrator, but a secure, AI infrastructure management platform that unifies visibility, control, and collaboration across all environments.
Harness’s broader IaCM ecosystem includes:
- Multi-IaC support: Terraform, OpenTofu, Terragrunt, Ansible (with more coming soon).
- Cost visibility: Pre-deployment cost estimation and post-deployment tracking.
- GitOps-native workflows: Approvals and policy checks built into pull requests.
- AI-powered policy generation: Intelligent guardrails to accelerate standards enforcement.
- AI-driven pipeline generation and failure analysis: leveraging the same intelligent capabilities used across Harness pipelines to streamline authoring and troubleshoot issues faster.
How IaCM is different
Unlike standalone tools today, Harness IaCM brings a unified, end-to-end approach to infrastructure delivery, combining:
- A single workspace model for every IaC tool
- Centralized variable and provider management giving platform teams consistent governance and control.
- AI-native governance with policy generation
- Native security scanning through integrated STO and SCS, ensuring misconfigurations and vulnerabilities are caught early in the SDLC.
- A unified SDLC pipeline experience, where infrastructure, application, security, and compliance checks all run through the same pipeline model.
- A developer-friendly experience with Harness IDP, offering self-service templates, golden paths, and standardized guardrails that make infrastructure safe and accessible for every team.
This all-in-one approach means fewer tools to manage, tighter compliance, and faster onboarding for developers while maintaining the flexibility of open IaC standards. Harness is the only platform that brings policy-as-code, cost insight, and self-service provisioning together into a single developer experience.
Get Started Today
Explore how Variable Sets and Provider Registry can streamline your infrastructure delivery all within the Harness Platform. Request a Demo to see how your team can standardize configurations, improve security, and scale infrastructure delivery without slowing down innovation.
You’re Late to the OpenTofu Party. Here’s Why That’s a Problem.
Are you still using Terraform without realizing the party has already moved on?
For years, Terraform was the default language of Infrastructure as Code (IaC). It offered predictability, community, and portability across cloud providers. But then, the music stopped. In 2023, HashiCorp changed Terraform’s license from Mozilla Public License (MPL) to the Business Source License (BSL), a move that put guardrails around what users and competitors could do with the code.
That shift opened a door for something new and truly open.
That “something” is OpenTofu.
And if you’re not already using or contributing to it, you’re missing your chance to help shape the future of infrastructure automation.
The fork that changed IaC forever
OpenTofu didn’t just appear out of thin air. It was born from community demand, a collective realization that Terraform’s BSL license could limit the open innovation that made IaC thrive in the first place.
So OpenTofu forked from Terraform’s last open source MPL version and joined the Linux Foundation, ensuring that it would remain fully open, community-governed, and vendor-neutral. A true Terraform alternative.
Unlike Terraform’s now-centralized governance, OpenTofu’s roadmap is decided by contributors, people building real infrastructure at real companies, not by a single commercial entity.
That means if you depend on IaC tools to build and scale your environments, your voice actually matters here.
Why OpenTofu is gaining momentum
OpenTofu is not a “different tool.” It’s a continuation, the same HCL syntax, same workflows, and same mental model, but under open governance and a faster, community-driven release cadence.
Let’s break down the Terraform vs OpenTofu comparison:
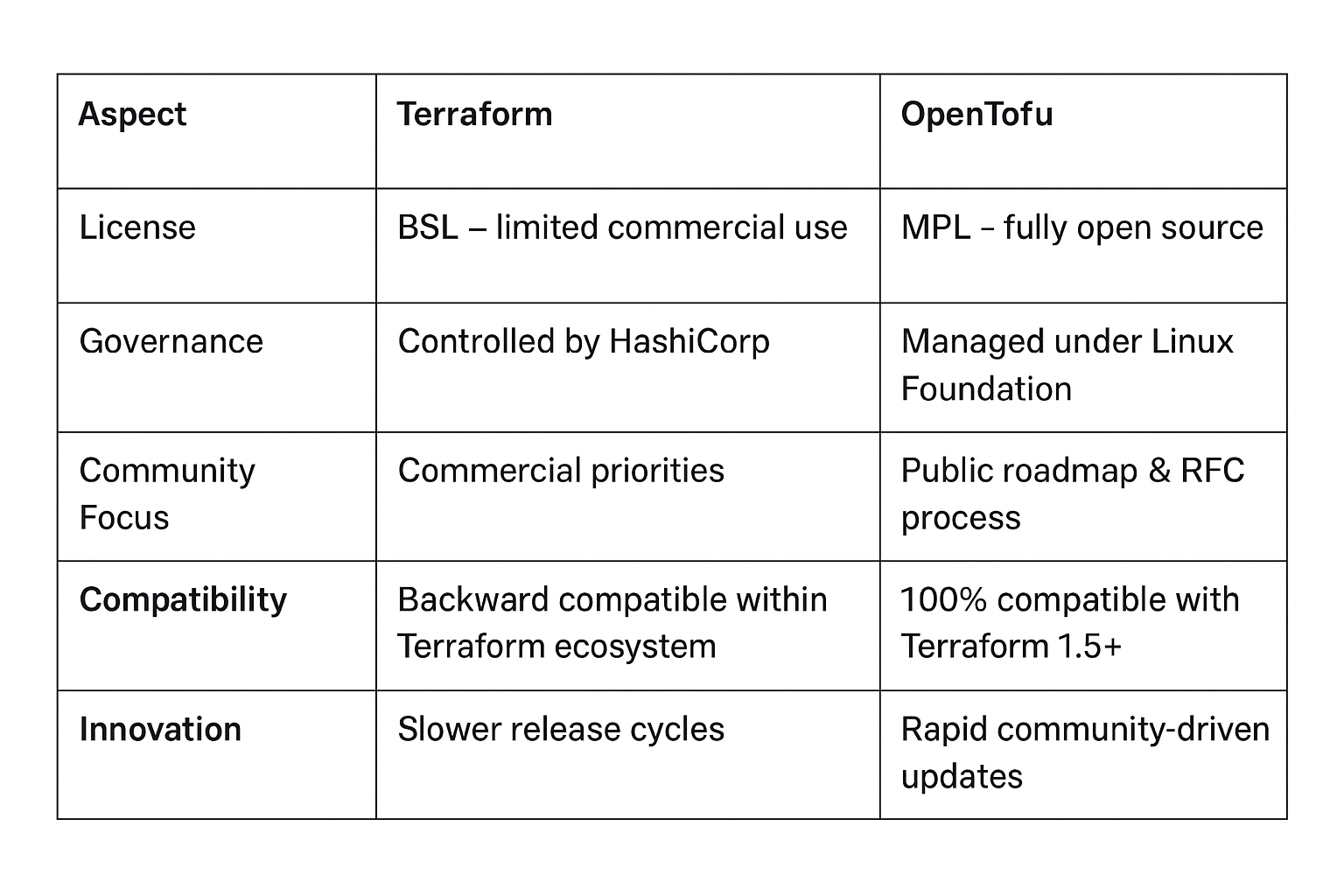
It’s still Terraform-compatible. You can take your existing configurations and run them with OpenTofu today. But beyond compatibility, OpenTofu is already moving faster and more freely, prioritizing developer-requested features that a commercial model might not. Some key examples of it's true power and longevity include:
1. Standardized distribution with OCI registries
Packaging and sharing modules or providers privately has always been clunky. You either ran your own registry or relied on Terraform Cloud.
OpenTofu solves this with OCI Registries, i.e. using the same open container standard that Docker uses.
It’s clean, familiar, and scalable.
Your modules live in any OCI-compatible registry (Harbor, Artifactory, ECR, GCR, etc.), complete with built-in versioning, integrity checks, and discoverability. No proprietary backend required.
For organizations managing hundreds of modules or providers, this is a big deal. It means your IaC supply chain can be secured and audited with the same standards you already use for container images.
2. True security with encryption at rest
Secrets in your Terraform state have always been a headache.
Even with remote backends, you’re still left with the risk of plaintext credentials or keys living inside the state file.
OpenTofu is the only IaC framework with built-in encryption at rest.
You can define an encryption block directly in configuration:
This encrypts the state transparently, no custom wrapper scripts or external encryption logic.
It also supports multiple key providers (AWS KMS, GCP KMS, Azure Key Vault, and more).
Coming soon in OpenTofu 1.11 (beta): ephemeral resources.
This feature lets providers mark sensitive data as transient so it never touches your state file in the first place. That’s a security level no other mainstream IaC tool currently offers.
3. A community-driven future
OpenTofu’s most powerful feature isn’t in its code, it’s in its process.
Every proposal goes through a public RFC. Every contributor has a say. Every decision is archived and transparent.
If you want a feature, you can write a proposal, gather community feedback, and influence the outcome.
Contrast that with traditional vendor-driven roadmaps, where features are often prioritized by product-market fit rather than user need.
That’s what “being late to the party” really means: you miss your seat at the table where the next decade of IaC innovation is being decided.
Why you don’t want to miss this party
Being early in an open-source ecosystem isn’t about bragging rights, it’s about influence.
OpenTofu is already gaining serious traction:
- Major cloud providers and IaC platforms are integrating it.
- Contributors from across the industry are shaping releases.
- Security and compliance enhancements (like encryption and OCI support) are coming faster than ever.
If you join later, you’ll still get the code. But you won’t get the same opportunity to shape it.
The longer you wait, the more you’ll be reacting to other people’s decisions instead of helping make them.
Ready to switch? The OpenTofu migration path is smooth.
Migrating is a one-liner!
The OpenTofu migration guide shows that most users can simply install the tofu CLI and reuse their existing Terraform files:
It’s the same commands, same workflow, but under an open license. You can even use your existing Terraform state files directly; no conversion step required.
For teams already managing infrastructure at scale, the move to OpenTofu doesn’t just preserve your workflow, it future-proofs it.
How Harness IaCM supports OpenTofu
When you’re ready to bring OpenTofu into a managed, collaborative environment, Harness Infrastructure as Code Management (IaCM) has you covered.
Harness IaCM natively supports both Terraform and OpenTofu. You can create a workspace, select your preferred binary, and run init, plan, and apply pipelines without changing your configurations.
That means you can:
- Experiment safely with OpenTofu while retaining version control.
- Store and share modules through a managed environment.
- Adopt OpenTofu’s features (like encryption and OCI) inside CI/CD pipelines.
- Gradually migrate Terraform workspaces without breaking production.
Harness essentially gives you the sandbox to explore OpenTofu’s potential, whether you’re testing ephemeral resource behavior or building private OCI registries for module distribution.
So while the OpenTofu community defines the standards, Harness ensures you can implement them securely and at scale.
Contribute, don’t just consume
The real magic of OpenTofu lies in participation.
If you’ve ever complained about Terraform limitations, this is your moment to shape the alternative.
You can:
- Test new features.
- Submit issues or RFCs.
- Contribute code or docs.
- Influence what the next release includes.
Everything lives in the open on the OpenTofu Repository.
Even reading a few discussions there shows how open, constructive, and fast-moving the community is.
Final thoughts
The IaC landscape is changing, and this time, the direction isn’t being set by a vendor, but by the community.
OpenTofu brings us back to the roots of open-source infrastructure: collaboration, transparency, and freedom to innovate.
It’s more than a fork, it’s a course correction.
If you’re still watching from the sidelines, remember: the earlier you join, the more your voice matters.
The OpenTofu party is already in full swing.
Grab your seat at the table, bring your ideas, and help build the future of IaC, before someone else decides it for you.
A 5-step enterprise guide to IaCM
Ever felt like managing your infrastructure is less like engineering and more like trying to herd cats through a perpetually changing obstacle course?
You’re not alone. In the glorious, chaotic world of modern IT, where microservices evolve constantly and scale pushes the limits of complexity, traditional approaches to managing infrastructure simply don’t keep pace. This is where Infrastructure as Code (IaC), and more importantly, Infrastructure as Code Management (IaCM) come in, enabling organizations to bring consistency, automation, and governance to even the most complex environments.
What is Infrastructure as Code (IaC)?
At its heart, IaC is the practice of defining and provisioning infrastructure resources. Think servers, databases, networks, and all their configurations, through code. Instead of clicking endlessly through cloud provider consoles or manually configuring settings, you write declarative configuration files. These files become the single source of truth for your infrastructure. Just like your application code, these infrastructure definitions can be versioned, reviewed, tested, and deployed, bringing software development best practices to infrastructure operations.
The advantages are transformative:
- Consistency: Say goodbye to “it works on my machine” for infrastructure. IaC ensures identical environments across development, staging, and production.
- Speed & Agility: Automate the provisioning process, drastically reducing the time it takes to spin up new environments or scale existing ones.
- Reliability: Automated, repeatable deployments minimize human error. If it works once, it will work again.
- Scalability: Easily replicate and scale infrastructure resources up or down, responding to demand with unprecedented elasticity.
- Traceability & Auditability: Every change to your infrastructure is tracked in version control, providing a clear audit trail and simplifying compliance.
Why IaCM is Vital for Enterprise Infrastructure at Scale
While IaC is a monumental leap forward, simply writing code for your infrastructure isn't enough when you're operating at an enterprise scale. Imagine hundreds of teams, thousands of infrastructure resources, multiple cloud providers, and strict regulatory requirements. This is where Infrastructure as Code Management (IaCM) becomes not just beneficial, but absolutely vital.
IaCM is the overarching strategy and set of tools designed to effectively manage your IaC across the entire organization. It addresses the inherent complexities and challenges that arise when scaling IaC practices:
- The “IaC Sprawl” Problem: Without IaCM, enterprises often end up with a fragmented landscape of IaC scripts, templates, and modules scattered across various repositories, lacking standardization and central oversight. IaCM brings order to this chaos.
- Centralized Control and Visibility: IaCM provides a unified platform to manage all your IaC configurations, irrespective of the underlying tools (OpenTofu or Terraform, CloudFormation, Ansible, Kubernetes manifests, etc.). This gives you a single pane of glass for all infrastructure definitions and deployments.
- Policy Enforcement and Compliance at Scale: Enterprises operate under stringent compliance mandates and internal governance policies. IaCM allows you to define these policies as code and automatically enforce them across all infrastructure deployments. This prevents unapproved configurations, ensures security best practices, and streamlines audit processes.
- Secure Secrets Management: Infrastructure often requires access to sensitive information like API keys, database credentials, and certificates. IaCM platforms integrate with dedicated secrets management solutions, ensuring that these secrets are never hardcoded and are securely injected only when needed, minimizing exposure.
- Advanced Workflow Orchestration and Automation: Enterprise-grade deployments are rarely simple. They involve complex sequences of provisioning, testing, approvals, and rollbacks. IaCM orchestrates these intricate workflows, automating the entire deployment pipeline and providing guardrails for safe, consistent, and compliant releases.
- Cost Management and Optimization: IaCM can help track and optimize infrastructure costs by ensuring that resources are provisioned according to policies, preventing over-provisioning, and identifying orphaned resources.
- Enhanced Collaboration and Governance: IaCM facilitates secure and efficient collaboration among diverse teams (developers, operations, security) while maintaining strict governance. It ensures that changes are reviewed, approved, and deployed consistently, reducing friction and improving team synergy.
- Consistency Across Hybrid and Multi-Cloud Environments: For enterprises leveraging hybrid cloud or multi-cloud strategies, IaCM provides the necessary abstraction and management capabilities to apply consistent practices and policies across disparate environments.
Without a robust IaCM strategy, large organizations risk turning the promise of IaC into a new form of operational headache – one where inconsistencies, security gaps, and manual oversight creep back in, negating the very benefits IaC aims to deliver. IaCM elevates IaC from a technical practice to a strategic operational model, essential for controlling and managing infrastructure at enterprise scale with speed, security, and precision.
Implement IaCM at Enterprise Scale: A 5-Step Guide
Implementing IaCM across an enterprise might seem daunting, but by breaking it down into a structured approach, organizations can successfully adopt and leverage its full potential. Here’s a 5-step guide to help you get started:
Step 1: Assess Your Current State & Define Your Vision
Before you start, understand where you are.
- Audit Existing Infrastructure: Document your current infrastructure, identifying what’s already managed by IaC (if anything), what’s manual, and where inconsistencies lie.
- Identify Pain Points: Pinpoint the challenges your teams face with current infrastructure management (e.g., slow provisioning, manual errors, compliance issues, lack of visibility).
- Define Your IaCM Vision: Clearly articulate what success looks like. What are your key objectives for implementing IaCM? (e.g., 90% automated provisioning, consistent environments, centralized policy enforcement).
- Stakeholder Alignment: Engage key stakeholders from development, operations, security, and compliance to ensure buy-in and align on the vision and goals.
Step 2: Choose Your IaC Tools & Platform
Selecting the right tools is crucial, but remember, IaCM is about managing them all.
- Evaluate IaC Tools: Based on your current infrastructure and future needs, choose your primary IaC tools such as OpenTofu or Terraform for infrastructure provisioning, Ansible for configuration management, Kubernetes for orchestration, CloudFormation for AWS-native).
- Select an IaCM Platform: This is the heart of your enterprise strategy. Consider platforms that offer centralized control, policy enforcement, secrets management, and workflow orchestration across your chosen IaC tools. Look for features like module registries, variable sets, and GitOps integration.
- Pilot Project: Start with a small, contained project to test your chosen IaC tools and IaCM platform. This allows you to iron out initial challenges and gather valuable feedback.
Step 3: Standardize & Centralize IaC Artifacts
Bringing order to chaos is a core benefit of IaCM.
- Develop Standardized Modules & Templates: Create reusable IaC modules and templates for common infrastructure components (e.g., standard VPCs, database configurations, application environments). Store these in your IaCM platform’s module registry.
- Centralize Variable Management: Utilize your IaCM platform’s variable sets to manage environment-specific configurations and sensitive data securely, preventing hardcoding and ensuring consistency.
- Implement Version Control: Enforce strict version control (e.g., Git) for all IaC code. This provides an audit trail, enables collaboration, and supports rollback capabilities.
- Establish Naming Conventions & Tagging: Implement clear naming conventions and tagging strategies for all infrastructure resources to improve visibility, cost tracking, and governance.
Step 4: Implement Policy-as-Code & Security Controls
Security and compliance are non-negotiable at the enterprise level.
- Define Policies as Code: Translate your organization’s security, compliance, and governance policies into code (e.g., using Open Policy Agent (OPA)).
- Automate Policy Enforcement: Integrate these policies into your IaCM platform to automatically enforce them during IaC deployments, preventing non-compliant infrastructure from being provisioned.
- Integrate Secrets Management: Connect your IaCM platform with an enterprise-grade secrets manager (e.g., HashiCorp Vault, AWS Secrets Manager) to securely inject credentials and sensitive data at runtime.
- Implement Role-Based Access Control (RBAC): Configure fine-grained RBAC within your IaCM platform to ensure that only authorized individuals and teams can initiate, approve, or modify infrastructure deployments.
- Drift Detection: Leverage your IaCM platform’s capabilities to detect and remediate configuration drift, ensuring that your deployed infrastructure always matches its defined state.
Step 5: Automate Workflows & Foster a GitOps Culture
Embrace automation and treat your infrastructure like application code.
- Automate CI/CD for Infrastructure: Integrate your IaCM platform with your existing CI/CD pipelines to fully automate the testing, approval, and deployment of IaC changes.
- Embrace GitOps: Drive all infrastructure changes through Git. Your Git repository becomes the single source of truth, and automated processes ensure that the actual infrastructure converges to the desired state defined in Git.
- Establish Review & Approval Processes: Implement peer review and automated approval gates for all IaC changes before deployment to production environments.
- Monitor & Optimize: Continuously monitor your IaCM pipelines and deployed infrastructure. Use data from your IaCM platform to identify bottlenecks, optimize costs, and refine your IaC and IaCM practices over time.
- Training & Education: Provide comprehensive training to your teams on IaC tools, IaCM platform usage, and the new GitOps-driven workflows. Foster a culture of learning and continuous improvement.
By following these steps, enterprises can systematically transition to a fully managed, automated, and compliant infrastructure environment, unlocking the true potential of Infrastructure as Code.
Take the Next Step with Harness IaCM
To truly operationalize IaCM at scale, enterprises need a platform built for governance, automation, and collaboration. Harness IaCM brings these capabilities together, enabling teams to manage infrastructure securely and efficiently across the organization.
Harness IaCM empowers teams to leverage reusable, enterprise-grade tooling designed to maximize consistency and speed, including:
- Module and Provider Registries: Centralize and share reusable infrastructure modules and providers, ensuring standardization and reducing duplication across teams.
- Workspace Templates: Define and reuse workspace configurations that maintain consistent setup and governance across all IaC projects.
- Default Pipelines: Streamline deployment workflows with preconfigured, best-practice CI/CD pipelines that accelerate infrastructure delivery.
With Harness IaCM, your organization can move beyond simply writing infrastructure code to managing it as a governed, automated, and scalable system—empowering teams to innovate faster and operate with confidence.


Confidently Ship Reusable OpenTofu and Terraform Modules
If there’s one thing we all care deeply about, it’s not fame, fortune or perfect HCL formatting; it’s reusability.
Whether you're a seasoned practitioner or new to Infrastructure as Code (IaC), Reusable modules are fast becoming the backbone of modern platform engineering. That's why modern platforms introduced Module Registries, central systems for publishing and consuming OpenTofu/Terraform modules across your organization.
They promote the DRY principle ("Don't Repeat Yourself") by codifying best practices, reducing duplication, and helping teams ship faster by focusing on what’s unique to their workload
But as teams scale, so does the risk: a misconfigured or buggy module can break dozens of environments in seconds.
Enter testing for infrastructure modules.
Real-world example: How one bug could have taken out everything
A few years ago, a platform engineering team learned a painful lesson: one bad Terraform command can destroy everything.
This real incident describes how a single misconfigured module and an unguarded Terraform destroy wiped out an entire staging environment, dozens of services gone in minutes. Recovery took days.
Now imagine your team building a reusable VPC module. Without testing, a single overlooked bug, say, a missing region variable or a misconfigured ACL that leaves an S3 bucket public, could silently make it into your registry. Every environment using that module would be exposed.
Here’s how to prevent it:
Before publishing, the platform team runs an integration pipeline that provisions a real test workspace with actual cloud credentials. On the first run, the missing region is caught. On the second, the public S3 bucket is flagged. Both are fixed before the module ever touches the registry.
The single step of testing modules in isolation before release turns potential outages into harmless build failures, protecting every downstream environment.
Why test your modules?
When you publish a shared module to your registry, you're trusting that it works now, and will continue to work later. Without dedicated testing, it's easy to miss:
- Required variables that aren't defined
- Breaking changes introduced by new commits
- Inadvertent updates that change resource behaviour across all consumers
- Cross-module dependency conflicts
- Security misconfigurations that expose resources publicly
Testing modules addresses these risks by validating them in isolation before they’re promoted to the registry.
How module tests work
A dedicated Integration pipeline is added to your module’s development branch. This pipeline:
- Provisions a real test environment.
- Executes real init, plan, and apply commands using OpenTofu (or Terraform).
- Validates cross-module compatibility and runtime behaviour.
✅ Tip: You define test inputs just like consumers would, using actual variables, connectors, and real infrastructure.
Only after the module passes this pipeline should it be promoted to the main branch and published.
Key Benefits
- Confidence in Reuse: Prevent broken or misconfigured modules from being published to your shared registry
- Safe Promotion Workflow: Validate modules in feature branches before promoting to main
- Catch Critical Misconfigurations: Detect missing variables, logic bugs, or public exposure risks early
- Governance and Drift Control: Enforce testing standards for modules, protecting downstream workspaces
- Auditable Changes: Avoid disaster-level rollouts by validating before any code touches production
- Encourages Reusability: With confidence in test coverage, teams are more likely to standardize on shared modules
CI/CD Integration and Testing Approaches
Testing modules complements traditional IaC testing techniques like the following methods:
tflint,validate- Syntax, formatting, and static checks
Terratest- Unit tests & mocks
Checkov,tfsec- Static security scanning
- Registry testing
- Real-world integration and runtime testing
Example CI/CD flow:
The integration testing stage spins up real infrastructure to validate that your modules work as expected before they reach production consumers.
Advanced Use Cases
Multi-Environment Testing
Test your modules across different cloud regions or account configurations to ensure portability:
Dependency Chain Validation
Test complex module hierarchies where modules depend on outputs from other modules:
Compliance and Security Validation
Integrate security scanning directly into your integration tests:
Rollback Testing
Validate that module updates can be safely rolled back by testing both upgrade and downgrade paths.
Implementation Considerations
Setting up tests for your modules requires some initial overhead, but the investment pays dividends as your module ecosystem grows:
Resource Costs: Integration tests provision real infrastructure, so factor in cloud costs for test environments. Use short-lived resources and automated cleanup to minimize expenses.
Test Environment Management: Establish dedicated sandbox accounts or subscriptions for integration testing to avoid conflicts with production resources.
Pipeline Execution Time: Real infrastructure provisioning takes longer than unit tests, so optimize your pipeline for parallel execution where possible.
Where to find Module Registry and Module Testing
Testing modules is becoming a core best practice in the OpenTofu ecosystem. But finding a platform that natively integrates registry management and test pipelines can be challenging.
If you’re looking for a platform that natively integrates module registries with testing pipelines, Harness Infrastructure as Code Management (IaCM) has you covered:
- ✅ Manage reusable modules with a built-in Module Registry
- ✅ Validate them using Integration pipelines before publishing
- ✅ Promote only tested, trusted modules to your consumers
Check out how to create and register your IaC modules and configure module tests to get started with pipeline setup and test inputs.
Conclusion
If you value stability, reusability, and rapid iteration, then testing your modules is more than a nice-to-have; it’s your safeguard against chaos.
By combining traditional CI/CD validation with real infrastructure testing, you get the best of both worlds: fast feedback and real-world assurance.
Start small. Iterate. And as your registry grows, let testing give you the confidence to scale.


Harness Expands Infrastructure as Code Management with Powerful Reusability Features for Greater Scalability
When we launched Harness Infrastructure as Code Management (IaCM), our goal was clear: help enterprises scale infrastructure automation without compromising on governance, consistency, or developer velocity. One year later and we’re proud of the progress we’ve made when it comes to delivering this solution with unmatched capabilities for templatization and enterprise scalability.
Today we’re announcing a major expansion of Harness IaCM with two new features: Module Registry and Workspace Templates. Both are designed to drive repeatability, security, and control with a common foundation: reusability.
In software development we talk quite a bit about the DRY principle, aka “Don’t Repeat Yourself.” These new capabilities bring that mindset to infrastructure, giving teams the tools to define once and reuse everywhere with built-in governance.
Bringing Reusability to Infrastructure
During customer meetings one theme came up over and over again – the need to define infrastructure once and reuse it across the platform in a secure and consistent manner, at scale. Our latest expansion of Harness IaCM was built to solve exactly that.
The DRY principle has long been a foundational best practice in software engineering. Now, with the launch of Module Registry and Workspace Templates, we’re bringing the same mindset to infrastructure – enabling platform teams to adopt a more standardized approach while reducing risk.
From a security and compliance perspective, these features allow teams to define infrastructure patterns once, test them thoroughly, and then reuse them with confidence across teams and environments. This massively improves consistency across teams and reduces the risk of human error — without slowing down delivery.
Here’s how each feature works.
Module Registry: Centralized Reusability for Tested Infrastructure Modules
Module Registry empowers users to create, share, and manage centrally stored “golden templates” for infrastructure components. By registering modules centrally, teams can:

- Reuse proven infrastructure patterns across projects without repeating code.
- Accelerate deployments by giving developers access to pre-approved and well-tested modules.
- Enforce governance through centralized oversight, ensuring only compliant, secure modules are used.
By making infrastructure components standardized, discoverable, and governed from a single location, Module Registry dramatically simplifies complexity and empowers teams to focus on building value, not reinventing the wheel.
The potential is already generating excitement among early adopters:
"The new Module Registry is exactly what we need to scale our infrastructure standards across teams,” said John Maynard, Director of Platform Engineering at PlayQ. “Harness IaCM has already helped us cut provisioning times dramatically – what used to take hours in Terraform Cloud now takes minutes – and with Module Registry, we can drive even more consistency and efficiency."
With Module Registry, we’re not just improving scalability, we’re simplifying the way teams manage their infrastructure.
Workspace Templates: Standardized Blueprints for Every New Project
Workspace Templates allow teams to predefine essential variables, configuration settings, and policies as reusable templates. When new workspaces are created, this approach:

- Enables teams to “start from template” and quickly spin up new projects with consistent, organization-approved settings.
- Reduces manual effort and accelerates onboarding by eliminating repetitive setup tasks and avoiding common misconfigurations.
- Keeps standards current by ensuring that any updates or improvements to a template automatically apply to all new workspaces created from it.
By embedding best practices into every new project, Workspace Templates help teams move faster while maintaining alignment, control, and repeatability across the organization.
How IaCM Has Transformed Infrastructure Management
Traditional Infrastructure as Code (IaC) solutions laid the foundation for how teams manage their cloud resources. But as organizations scale, many run into bottlenecks caused by complexity, drift, and fragmented tooling. Without built-in automation, repeatability, and visibility, teams struggle to maintain reliable infrastructure across environments.
Harness IaCM was built to solve these challenges. As a proud sponsor and contributor to the OpenTofu community, Harness also supports a more open, community-driven future for infrastructure as code. IaCM builds on that foundation with enterprise-grade capabilities like:
- Policy-aware pipelines that bake in governance and security from the start
- Change review workflows that catch issues early and enable safe collaboration
- Developer self-service with automated guardrails
- Reusable templates, modules, and variable sets that reduce duplication and enforce standards
- Tight integration with Harness CI/CD and Cloud Cost Management for full lifecycle automation and insight
Together, these capabilities help teams to:
- Move faster with flexible, standardized infrastructure workflows
- Minimize risk by enforcing best practices automatically
- Accelerate developer productivity without compromising on controls
- Streamline operations while maintaining visibility and accountability across teams
Since its GA launch last year, Harness IaCM has gained strong traction with several dozens of enterprise customers already on board – including multiple seven-figure deals. In financial services, one customer is managing dozens of workspaces using just a handful of templates, with beta users averaging more than 10 workspaces per template. In healthcare, another team now releases 100% of their modules with pre-configured tests, dramatically improving reliability. And a major banking customer has scaled to over 4,000 workspaces in just six months, enabled by standardization and governance patterns that drive consistency and confidence at scale.
With a focus on automation, reusability and visibility, Harness IaCM is helping enterprise teams rethink how they manage and deliver infrastructure at scale.
What’s Next for IaCM?
Harness’ Infrastructure as Code Management (IaCM) was built to address a massive untapped opportunity: to merge automation with deep capabilities in compliance, governance, and operational efficiency and create a solution that redefines how infrastructure code is managed throughout its lifecycle. Since launch, we’ve continued to invest in that vision – adding powerful features to drive consistency, governance, and speed. And we’re just getting started.
As we look ahead, we’re expanding IaCM in three key areas:
- Expanded Support for IaC Tools: We’re expanding support to tools like Ansible and Terragrunt. Teams can manage infrastructure provisioning, configuration, and application deployment all within a single Harness pipeline.
- Standardization at Scale: We’re rolling out reusable variable sets and a centralized provider registry to make it easier for teams to standardize configuration and onboard new projects quickly.
- Developer Experience: We’re significantly improving how teams create and manage ephemeral workspaces for testing, iteration, and experimentation in isolated, secure environments.
I invite you to sign up for a demo today and see firsthand how Harness IaCM is helping organizations scale infrastructure with greater speed, consistency, and control.
.svg)