Featured Blogs

Today, Harness is announcing the General Availability of Artifact Registry, a milestone that marks more than a new product release. It represents a deliberate shift in how artifact management should work in secure software delivery.
For years, teams have accepted a strange reality: you build in one system, deploy in another, and manage artifacts somewhere else entirely. CI/CD pipelines run in one place, artifacts live in a third-party registry, and security scans happen downstream. When developers need to publish, pull, or debug an artifact, they leave their pipelines, log into another tool, and return to finish their work.
It works, but it’s fragmented, expensive, and increasingly difficult to govern and secure.
At Harness, we believe artifact management belongs inside the platform where software is built and delivered. That belief led to Harness Artifact Registry.
A Startup Inside Harness
Artifact Registry started as a small, high-ownership bet inside Harness and a dedicated team with a clear thesis: artifact management shouldn’t be a separate system developers have to leave their pipelines to use. We treated it like a seed startup inside the company, moving fast with direct customer feedback and a single-threaded leader driving the vision.The message from enterprise teams was consistent: they didn’t want to stitch together separate tools for artifact storage, open source dependency security, and vulnerability scanning.
So we built it that way.
In just over a year, Artifact Registry moved from concept to core product. What started with a single design partner expanded to double digit enterprise customers pre-GA – the kind of pull-through adoption that signals we've identified a critical gap in the DevOps toolchain.
Today, Artifact Registry supports a broad range of container formats, package ecosystems, and AI artifacts, including Docker, Helm (OCI), Python, npm, Go, NuGet, Dart, Conda, and more, with additional support on the way. Enterprise teams are standardizing on it across CI pipelines, reducing registry sprawl, and eliminating the friction of managing diverse artifacts outside their delivery workflows.
One early enterprise customer, Drax Group, consolidated multiple container and package types into Harness Artifact Registry and achieved 100 percent adoption across teams after standardizing on the platform.
As their Head of Software Engineering put it:
"Harness is helping us achieve a single source of truth for all artifact types containerized and non-containerized alike making sure every piece of software is verified before it reaches production." - Jasper van Rijn
Why This Matters: The Registry as a Control Point
In modern DevSecOps environments, artifacts sit at the center of delivery. Builds generate them, deployments promote them, rollbacks depend on them, and governance decisions attach to them. Yet registries have traditionally operated as external storage systems, disconnected from CI/CD orchestration and policy enforcement.
That separation no longer holds up against today’s threat landscape.
Software supply chain attacks are more frequent and more sophisticated. The SolarWinds breach showed how malicious code embedded in trusted update binaries can infiltrate thousands of organizations. More recently, the Shai-Hulud 2.0 campaign compromised hundreds of npm packages and spread automatically across tens of thousands of downstream repositories.
These incidents reveal an important business reality: risk often enters early in the software lifecycle, embedded in third-party components and artifacts long before a product reaches customers.When artifact storage, open source governance, and security scanning are managed in separate systems, oversight becomes fragmented. Controls are applied after the fact, visibility is incomplete, and teams operate in silos. The result is slower response times, higher operational costs, and increased exposure.
We saw an opportunity to simplify and strengthen this model.

By embedding artifact management directly into the Harness platform, the registry becomes a built-in control point within the delivery lifecycle. RBAC, audit logging, replication, quotas, scanning, and policy enforcement operate inside the same platform where pipelines run. Instead of stitching together siloed systems, teams manage artifacts alongside builds, deployments, and security workflows. The outcome is streamlined operations, clearer accountability, and proactive risk management applied at the earliest possible stage rather than after issues surface.
Introducing Dependency Firewall: Blocking Risk at Ingest
Security is one of the clearest examples of why registry-native governance matters.
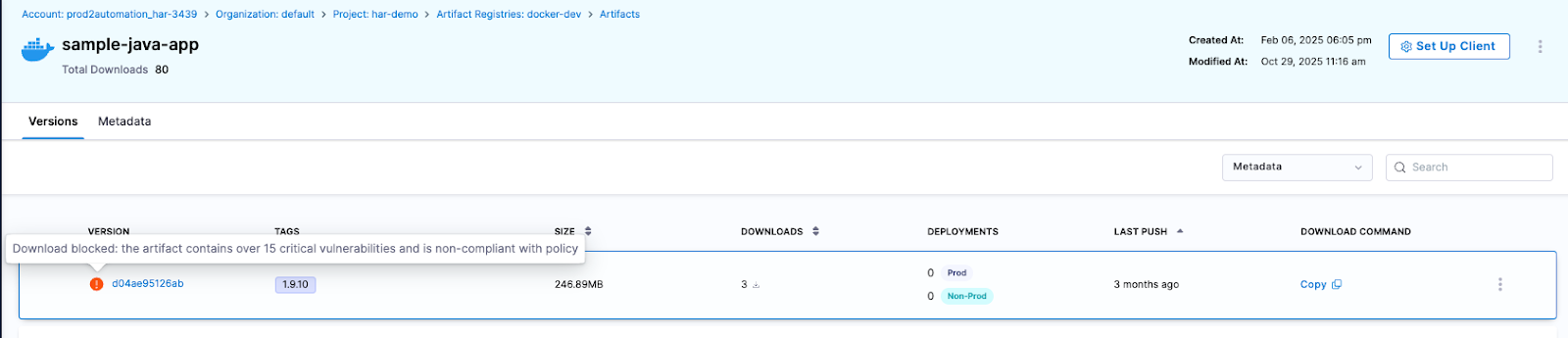
Artifact Registry delivers this through Dependency Firewall, a registry-level enforcement control applied at dependency ingest. Rather than relying on downstream CI scans after a package has already entered a build, Dependency Firewall evaluates dependency requests in real time as artifacts enter the registry. Policies can automatically block components with known CVEs, license violations, excessive severity thresholds, or untrusted upstream sources before they are cached or consumed by pipelines.
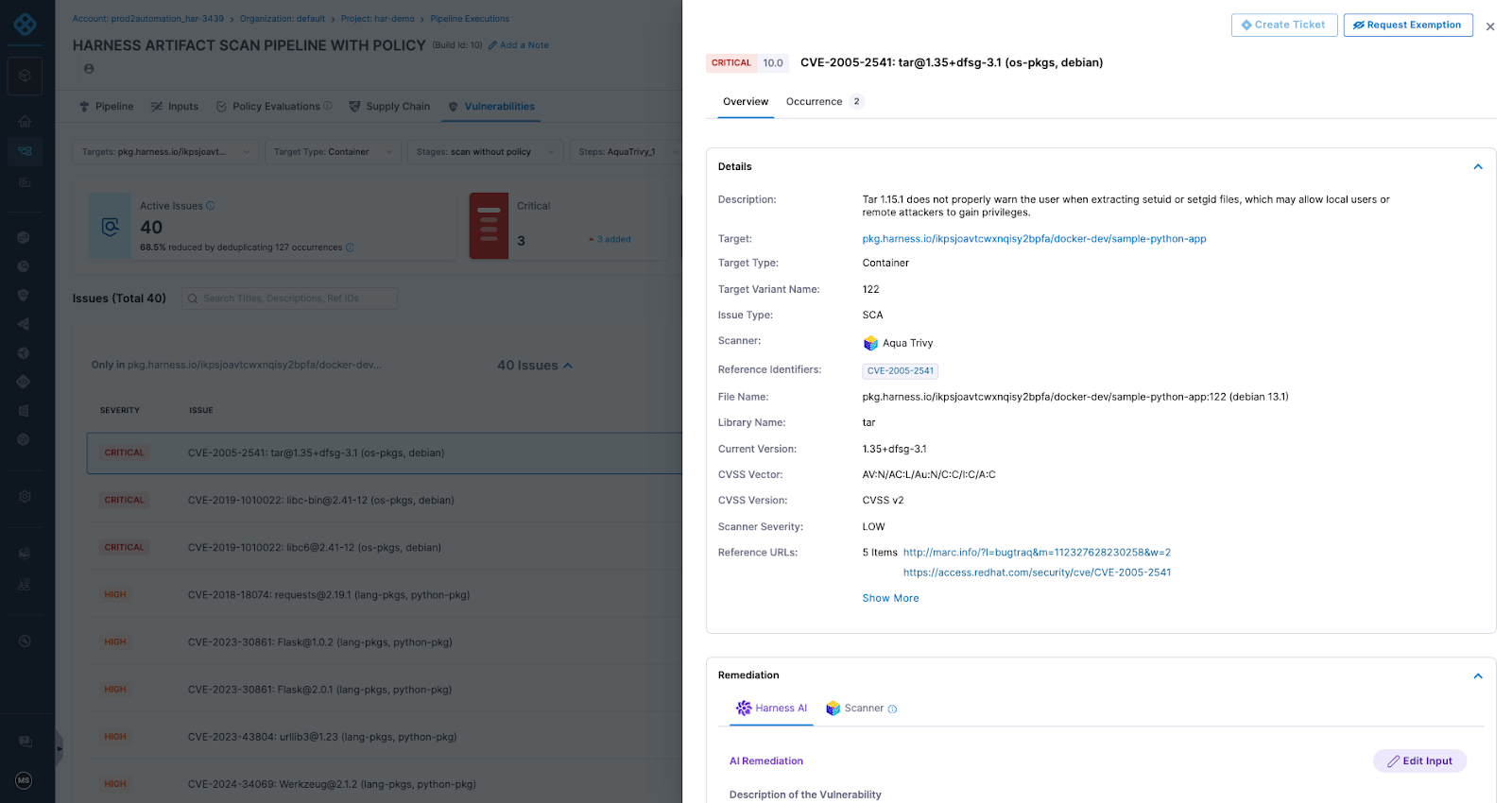
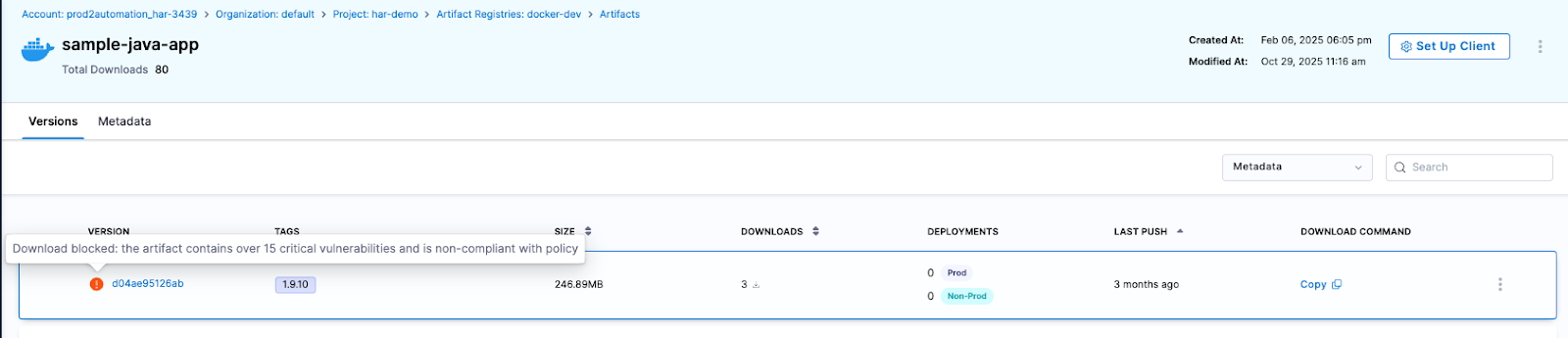
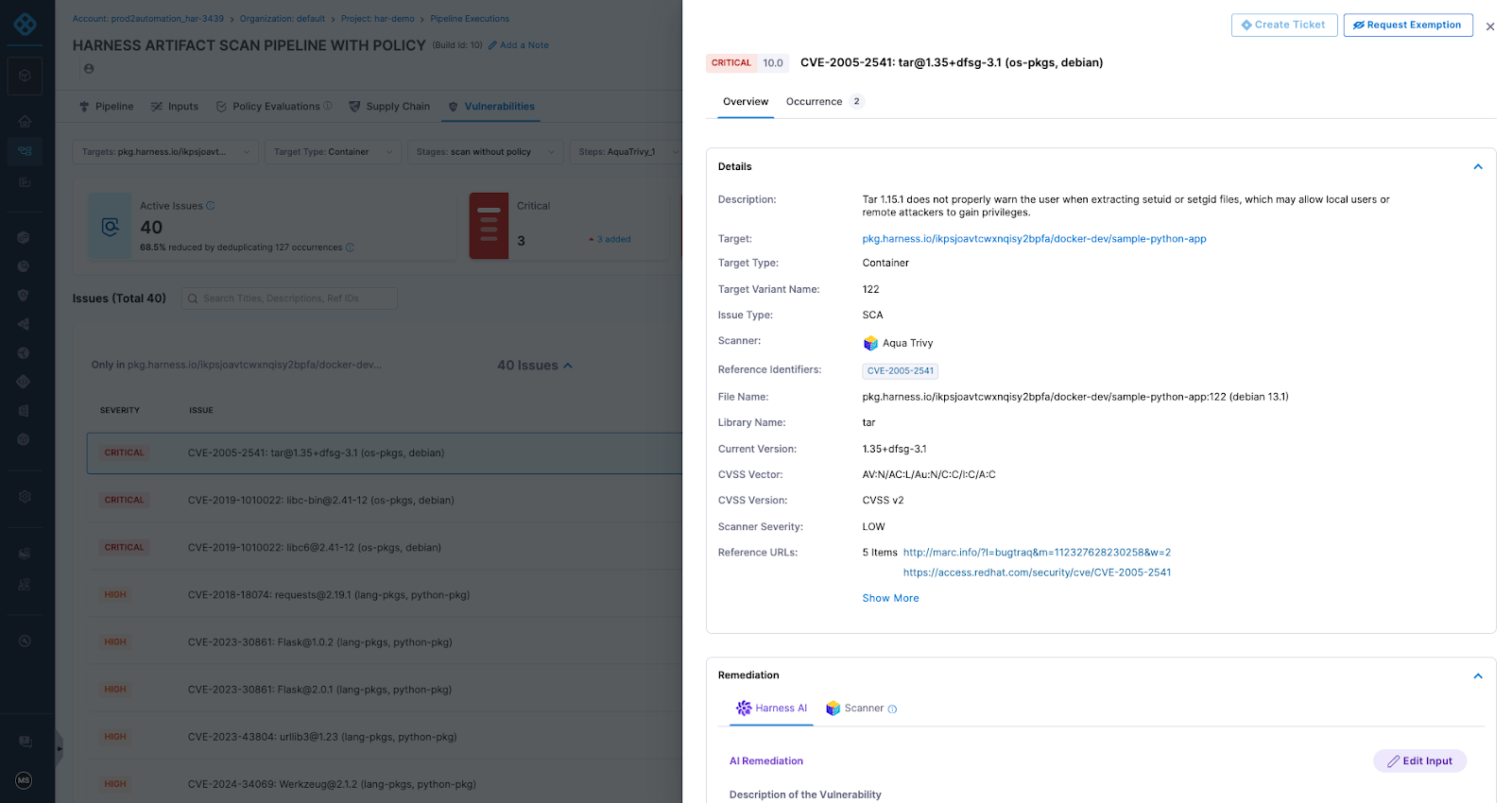
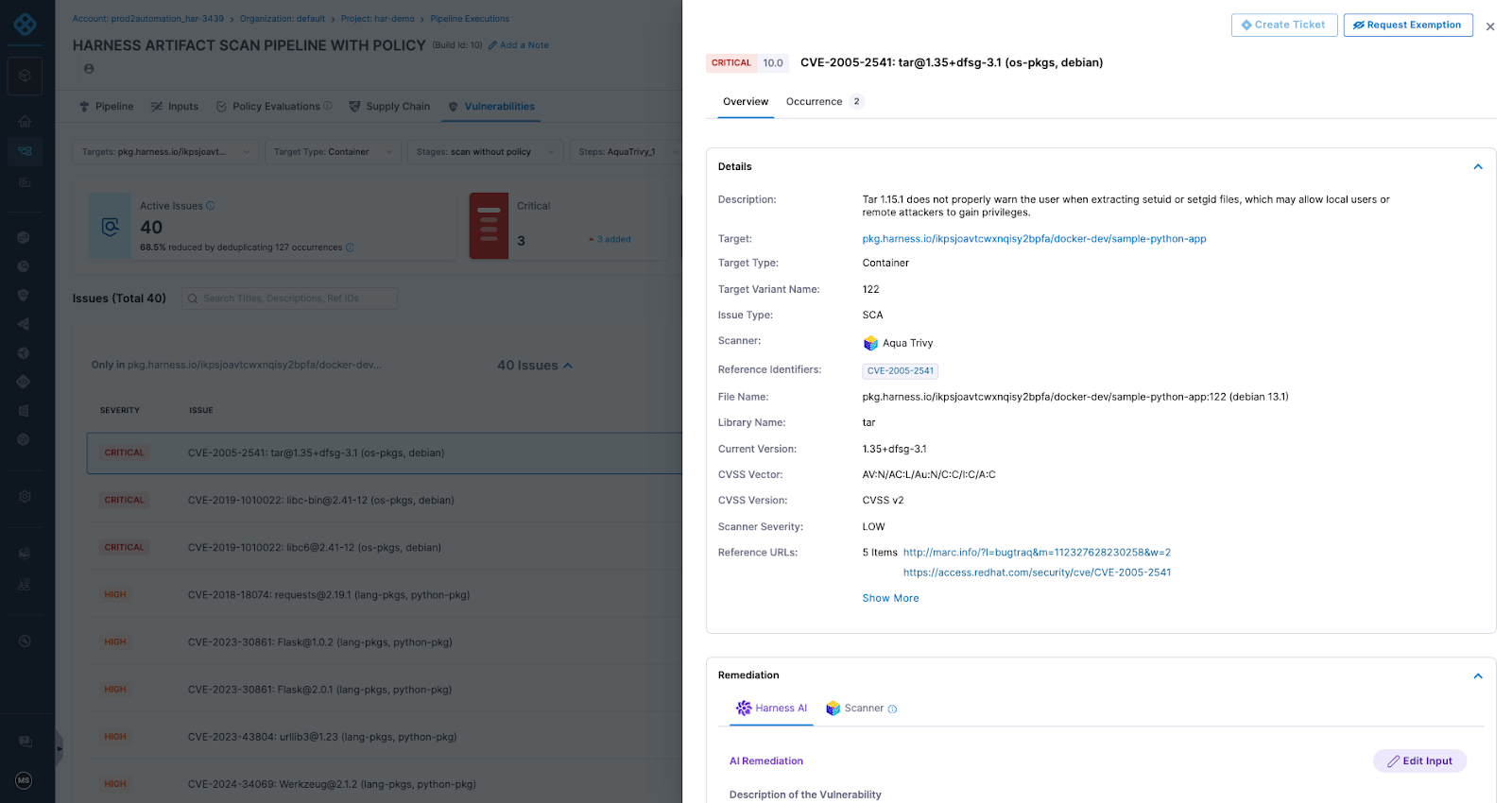
Artifact quarantine extends this model by automatically isolating artifacts that fail vulnerability or compliance checks. If an artifact does not meet defined policy requirements, it cannot be downloaded, promoted, or deployed until the issue is addressed. All quarantine and release actions are governed by role-based access controls and fully auditable, ensuring transparency and accountability. Built-in scanning powered by Aqua Trivy, combined with integrations across more than 40 security tools in Harness, feeds results directly into policy evaluation. This allows organizations to automate release or quarantine decisions in real time, reducing manual intervention while strengthening control at the artifact boundary.
The result is a registry that functions as an active supply chain control point, enforcing governance at the artifact boundary and reducing risk before it propagates downstream.
The Future of Artifact Management is here
General Availability signals that Artifact Registry is now a core pillar of the Harness platform. Over the past year, we’ve hardened performance, expanded artifact format support, scaled multi-region replication, and refined enterprise-grade controls. Customers are running high-throughput CI pipelines against it in production environments, and internal Harness teams rely on it daily.
We’re continuing to invest in:
- Expanded package ecosystem support
- Advanced lifecycle management, immutability, and auditing
- Deeper integration with Harness Security and the Internal Developer Portal
- AI-powered agents for OSS governance, lifecycle automation, and artifact intelligence
Modern software delivery demands clear control over how software is built, secured, and distributed. As supply chain threats increase and delivery velocity accelerates, organizations need earlier visibility and enforcement without introducing new friction or operational complexity.
We invite you to sign up for a demo and see firsthand how Harness Artifact Registry delivers high-performance artifact distribution with built-in security and governance at scale.
Latest Blogs
Why Artifact Repository Sprawl Slows Down Software Delivery
Three weeks into a platform modernization project, this question landed in my inbox: "Why does our deployment pipeline take 40 minutes instead of four?"
This is artifact repository sprawl in practice, and it does more than slow pipelines. It fragments your security posture, your compliance evidence, and your ability to answer basic questions like "what's actually running in production right now?"
How Artifact Repository Sprawl Creates CI/CD Bottlenecks
Modern software delivery pipelines consume and produce artifacts at every stage. A typical microservices application might pull base container images, install language-specific packages, bundle compiled binaries, and push versioned containers, all before a single integration test runs. When each artifact type lives in a separate registry, every pipeline stage authenticates separately, fetches metadata independently, and logs access in disconnected audit systems.
The operational cost compounds quickly. Build jobs that should complete in minutes stall while waiting for credential rotation across four registry providers. Terraform modules reference hardcoded repository URLs that break when teams migrate between vendors. Developers waste hours debugging "works on my machine" issues that trace back to different registries serving different cached versions in CI versus local environments.
Container registry management alone doesn't solve this. You can centralise Docker images perfectly and still have sprawl across Maven Central proxies, PyPI mirrors, and npm registries that each handle authentication, scanning, and access policies differently. The sprawl persists even when every tool works correctly in isolation.
What this actually looks like in a pipeline:
# A typical fragmented pipeline - four different auth mechanisms, four different APIs
stages:
- name: Pull Base Image
spec:
connectorRef: docker_hub_connector # Registry 1: Docker Hub
image: node:20-alpine
- name: Install Dependencies
spec:
command: npm install # Registry 2: npm registry (or private Verdaccio)
- name: Build Java Service
spec:
command: mvn package # Registry 3: Maven Central / Artifactory
- name: Push Container
spec:
connectorRef: ecr_connector # Registry 4: Amazon ECR
repo: my-app
tags: <+pipeline.sequenceId>Four registries, four sets of credentials to rotate, four places to check when something breaks. Now multiply that by every microservice in your org.
How Registry Consolidation Reduces Security Blind Spots
Software supply chain governance requires knowing what entered your build process, who approved it, and whether it matches what shipped to production. Artifact repository sprawl makes that visibility nearly impossible without building custom integration layers that inevitably lag behind the registries they monitor.
Consider a realistic scenario: your security team needs to answer whether a new CVE affects any production workload. With fragmented registries, you're querying Docker Hub for container manifests, Artifactory for Java dependencies, a separate S3 bucket for ML models, and hoping the correlation logic catches every transitive dependency. Miss one registry in the sweep and you've got an incomplete answer. Get the timing wrong and you're correlating artifacts from different build windows.
Unified artifact management changes the equation. When containers, packages, and models flow through a single governance boundary, you can enforce consistent policies at ingestion time rather than auditing violations after deployment. Access control becomes auditable in one place instead of five.
This matters for supply chain attacks targeting package managers, which increasingly exploit the trust developers place in upstream dependencies. When every language ecosystem has its own registry with different security scanning capabilities and policy enforcement mechanisms, attackers optimize for the weakest link. A malicious npm package that wouldn't pass container scanning slips through because the npm registry didn't apply the same controls.
How a unified registry changes incident response:
# Fragmented approach: check each registry separately
1. Query Docker Hub for affected container manifests (minutes)
2. Query Artifactory for affected Java dependencies (minutes)
3. Query npm registry for affected Node packages (minutes)
4. Cross-reference results manually (hours)
5. Hope you didn't miss a registry (uncertainty)
# Consolidated approach: one query, full picture
1. Search artifact registry for component with CVE ID (seconds)
2. View which artifacts contain the dependency (SBOM) (seconds)
3. Check Deployments tab for production exposure (seconds)
4. Full answer with audit trail (confidence)The Hidden Cost of Sprawl on Platform Teams
Platform engineering teams building internal developer portals face a choice: abstract away registry complexity or force application teams to manage it themselves. Neither option works well with artifact sprawl. Abstraction requires maintaining integration code for every registry type, each with different APIs for search, versioning, and access control. Forcing teams to manage it themselves guarantees inconsistent practices and duplicate effort across squads.
The operational burden shows up in unexpected places. Onboarding a new service means provisioning credentials across multiple registries. Rotating secrets means updating pipelines in every repository that publishes or consumes artifacts. And when you need to answer "who pulled what and when" for a compliance audit, you're stitching together logs from disconnected systems with different formats and retention windows.
DevOps toolchain efficiency suffers because fragmented registries create artificial boundaries in automation workflows. Teams end up building brittle orchestration logic that breaks whenever registry APIs change or network partitions separate previously co-located systems.
Why Sprawl Compounds in Hybrid and Multicloud Environments
Running workloads across on-premises data centres and multiple cloud providers amplifies every artifact sprawl problem. Each environment tends to accumulate its own preferred registries: Amazon ECR for AWS workloads, Google Artifact Registry for GCP services, a self-hosted Harbor instance in the data centre. What started as practical deployment choices hardens into infrastructure that's expensive to consolidate and risky to migrate.
Software delivery pipeline consistency becomes nearly impossible. A feature branch tested against artifacts from the on-prem registry might behave differently in production pulling from ECR because different proxy cache timing introduced a version skew. Compliance auditors asking for artifact lineage get stitched-together spreadsheets instead of queryable attestations because no single system has the full picture.
Registry consolidation doesn't mean forcing everything into one physical location. It means establishing a logical control plane that can proxy, cache, and govern artifacts regardless of where they're ultimately stored. The governance layer stays consistent even when artifacts need to live close to compute for latency or compliance reasons.
How Harness Artifact Registry Addresses Sprawl
Harness Artifact Registry was designed to centralise artifact storage and enforce governance across engineering teams dealing with exactly these sprawl problems. It supports 16+ package types natively, including Docker, Helm, Maven, npm, PyPI, NuGet, Go, Cargo, Dart, Swift, RPM, Conda, Hugging Face (for ML models), and generic files, so teams don't need a separate registry for each language ecosystem.
Upstream proxy and caching is where consolidation starts in practice. Instead of every developer and CI job pulling directly from Docker Hub, Maven Central, PyPI, or npm, they pull through Harness AR's proxy layer. The proxy caches artifacts locally, so external registry downtime doesn't break your builds, and every fetch is subject to the same governance policies.
# Before: Direct pulls from multiple external registries
developer laptop --> Docker Hub
CI runner --> Maven Central
CI runner --> npm registry
CI runner --> PyPI
# After: Everything routes through Harness AR upstream proxies
developer laptop --> Harness AR (Docker proxy) --> Docker Hub
CI runner --> Harness AR (Maven proxy) --> Maven Central
CI runner --> Harness AR (npm proxy) --> npm registry
CI runner --> Harness AR (Python proxy) --> PyPIUpstream proxies are available for all 16+ supported package types, so the governance boundary is genuinely universal rather than limited to containers.
The Dependency Firewall gates what enters your registry from upstream sources. Currently, OPA policies apply only to artifacts fetched through upstream proxies. Direct pushes to hosted registries are not yet subject to Dependency Firewall policies; that capability is coming soon.
For now, governance for direct pushes relies on Security Tests policy sets (Docker/Helm only) or post-ingestion scanning via STO/SCS. There are some built-in policy templates that cover the most common scenarios:
- CVSS Threshold - Block packages with vulnerability scores above a threshold
- License Policy - Block packages with non-compliant licenses (e.g., GPL in a proprietary codebase)
- Package Age - Block packages published too recently (a common indicator of typosquatting attacks)
Each evaluation results in one of three statuses: Passed, Warning, or Blocked. Blocked artifacts are never cached in your registry. You can write custom Rego policies beyond the built-in templates.
# Example: Block any npm package published less than 7 days ago
package artifact
deny[msg] {
input.metadata.published_days_ago < 7
msg := sprintf("Package %s was published %d days ago (minimum: 7)",
[input.metadata.name, input.metadata.published_days_ago])
}
Currently, the Dependency Firewall's OPA policies apply to upstream proxy fetches. Support for applying these policies across all registry types, including direct pushes to hosted registries, is coming soon.
Role-based access control provides three pre-built roles (Viewer, Contributor, Admin) that can be assigned to users, user groups, or service accounts at the registry level.
Security scanning and quarantine work through two layers. First, the Dependency Firewall evaluates upstream artifacts against OPA policies at fetch time, blocking anything that fails before it ever enters your registry. Second, for artifacts already in the registry, Harness integrates with Security Testing Orchestration (STO) and Supply Chain Security (SCS) to scan for vulnerabilities and generate SBOMs. Registries can be configured with Security Tests policy sets that evaluate artifacts during ingestion via a scan pipeline (currently supported for Docker and Helm registries). Artifacts that violate policies are automatically quarantined, preventing them from being pulled or used in any downstream pipeline. This requires enabling the relevant policy configuration on your registry.
Quarantine can also be applied manually through the UI on any artifact (three-dot menu > Quarantine), with a required reason for audit purposes. Quarantined artifacts can be released via "Remove from Quarantine" once the issue is resolved.
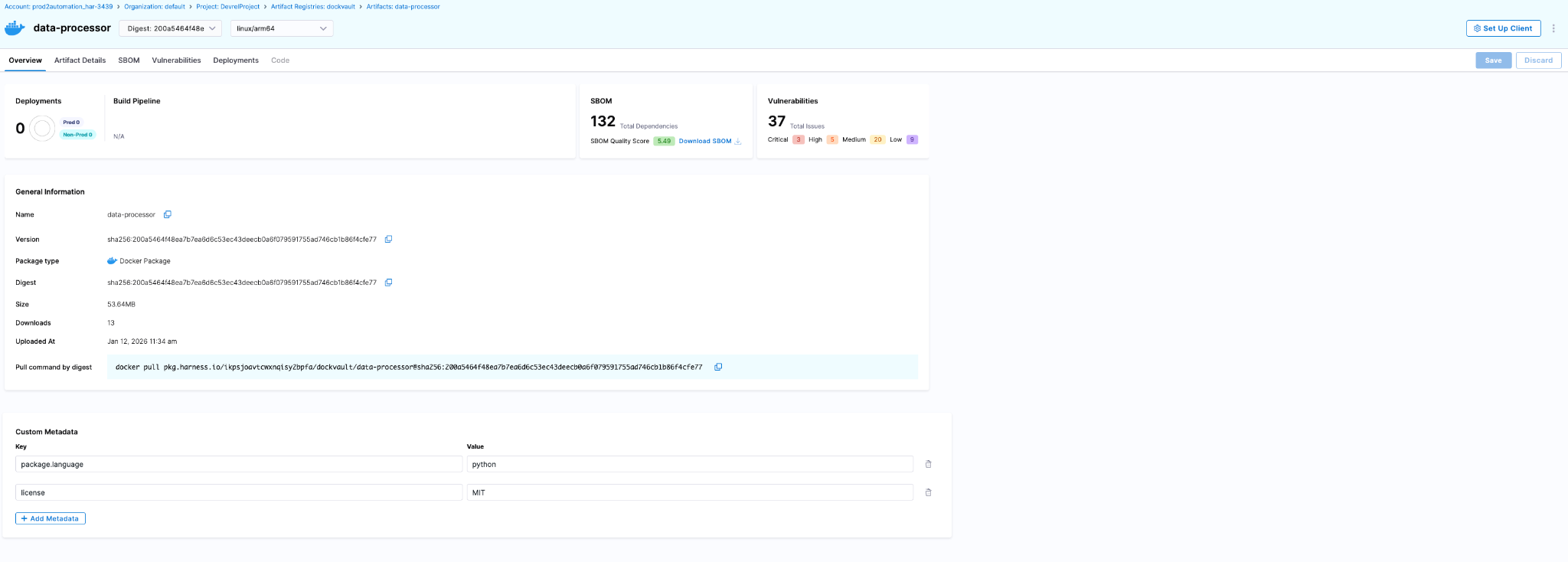
The artifact details page surfaces security and deployment data directly:
- SBOM tab - Dependency lists, suppliers, package managers (requires SCS module)
- Vulnerabilities tab - Scan results from STO (requires STO module)
- Deployments tab - Which environments this artifact is deployed to and instance counts (requires CD module)
Audit trails are built into the Harness platform. Every artifact action is tracked with the actor, timestamp, and context. You can query these via the UI (Account Settings > Audit Trail, filter by Artifact Registry) or the API.
Teams serious about software supply chain governance end up implementing these controls eventually. Harness AR packages upstream proxy caching, Dependency Firewall, RBAC, security scanning via STO/SCS, and platform-wide audit trails into a single registry that covers the breadth of package types modern engineering teams actually use. The alternative is maintaining a constellation of registry-specific integrations that break whenever vendors deprecate APIs or security requirements tighten.
You can explore the platform or review implementation patterns in the Artifact Registry documentation.
Reducing Artifact Sprawl Starts with Visibility
Fixing artifact repository sprawl doesn't require ripping out every existing registry overnight. It requires establishing a control plane that can answer basic questions reliably: what artifacts exist, where they came from, who has access, and what depends on them. Once you have that visibility, you can start enforcing policies consistently and eliminating redundant tooling incrementally.
The teams that move fastest at scale treat artifact management as infrastructure that enables speed rather than a storage problem that needs solving registry by registry. They consolidate governance boundaries, route external dependencies through proxy layers with policy enforcement, and build confidence that what passed security checks is actually what reached production.
If your deployment pipelines feel slower than they should, or your security team struggles to answer supply chain questions confidently, artifact sprawl is worth examining. The operational debt compounds quietly until it doesn't, usually during an incident when you need answers fast and discover your artifact lineage spans five disconnected systems with inconsistent audit logs.
FAQ
Do I have to migrate all my artifacts to Harness AR at once?
No. Start with upstream proxies (no migration needed), then migrate hosted artifacts incrementally per team/package type.
What if I'm already using JFrog Artifactory?
Harness AR can proxy Artifactory as an upstream source while you migrate, or coexist indefinitely if you need Artifactory-specific features.
Does this lock me into Harness for CI/CD?
No. Harness AR works with any CI/CD tool that can authenticate to a registry. The integrations with Harness CD/STO/SCS are optional add-ons.


Where Artifacts Find Their Home


The Dangerous Myth: “We Have SCA, So We’re Covered”
- SCA provides visibility into open source risk but leaves artifacts, pipelines, containers, and AI components exposed.
- CI/CD pipelines are privileged infrastructure and must be treated as zero-trust environments.
- Build systems are a critical trust boundary; artifact attestation and registry gating are essential.
- Container images, third-party integrations, and AI models are now active supply chain attack vectors.
- True supply chain security requires control at ingest, build, promotion, and runtime — not just scanning.
Most organizations begin their software supply chain journey the same way: they implement Software Composition Analysis (SCA) to manage open source risk. They scan for vulnerabilities, generate SBOMs, and remediate CVEs. For many teams, that feels like progress—and it is.
But it is not enough.
As discussed in the webinar conversation with Information Security Media Group, open-source visibility is necessary, but it is not sufficient. Modern applications are no longer just collections of third-party libraries. They are built, packaged, signed, stored, promoted, deployed, and increasingly augmented by AI systems. Each stage introduces new dependencies and new trust boundaries.
Events like Log4j made open source risk impossible to ignore. However, the evolution of the threat landscape has demonstrated that attackers are no longer limited to exploiting known vulnerabilities in libraries. They are targeting the mechanics of delivery itself—ingestion, build pipelines, artifact storage, and CI/CD automation. Organizations that stop at SCA are securing one layer of a much broader system.
Where Modern Supply Chains Actually Get Compromised
Artifact Integrity and Registry Blind Spots
Artifacts are the final outputs of the build process—container images, binaries, scripts, Helm charts, JAR files. They are what actually run in production. Yet many organizations treat artifact management as operational plumbing rather than a security control point.
The webinar highlighted how focusing exclusively on source code can obscure the reality that artifacts may be tampered with after build, altered during promotion, or stored in misconfigured registries. Visibility into open source dependencies does not automatically guarantee artifact integrity. An attacker who compromises a registry or intercepts promotion workflows can distribute malicious artifacts at scale.
The key risk lies in assuming that once an artifact is built, it is trustworthy. Without signing, provenance tracking, and gating at the registry level, artifacts become one of the most exploitable surfaces in the supply chain.
CI/CD Pipelines as Privileged Infrastructure
CI/CD systems hold credentials, secrets, deployment paths, and signing keys. They connect development directly to production. As one of the speakers noted during the discussion, pipelines should be treated as privileged infrastructure and assumed to be potential targets of compromise.
A compromised runner can publish malicious artifacts, exfiltrate secrets, or promote unauthorized builds. This is not theoretical. Attacks involving poisoned GitHub Actions and manipulated build systems demonstrate how easily the pipeline itself can become the distribution mechanism.
Security must therefore extend beyond scanning artifacts to enforcing strict governance within pipelines. This includes least privilege access, ephemeral credentials, audit trails, and Policy as Code enforcement to ensure required security checks cannot be bypassed.
Containers and Upstream Image Poisoning
Container ecosystems introduce additional risk vectors. Malicious images uploaded to public registries, typosquatting packages, and compromised upstream components can all infiltrate environments through seemingly legitimate pulls.
Organizations that implicitly trust external registries transfer vendor risk into their own infrastructure. Without upstream proxy controls, cool-off periods, or quarantine mechanisms, container ingestion becomes another blind spot.
The supply chain does not stop at internal code repositories. It extends to every external source that feeds into the build.
Vendor and Third-Party Integration Risk
Modern delivery pipelines integrate numerous third-party services. Vendors often have privileged access to environments or automated integrations into CI/CD workflows. If a vendor is compromised, that risk propagates downstream.
The webinar discussion emphasized that the supply chain must be viewed as a “trust fabric.” Pipelines, registries, and vendors are all part of that fabric. A weakness in any one node can cascade across the system.
Build Systems Are the New Trust Boundary
Build systems represent one of the most underestimated attack surfaces in modern software delivery. A source tree may pass review and scanning, yet small modifications in the build process can fundamentally alter the resulting artifact.
Examples discussed during the session included pre-install hooks, registry overrides, runtime installers, or seemingly minor shell script changes that introduce malicious behavior before artifacts are signed or scanned. These changes can bypass traditional SCA tools because the underlying source code appears clean.
This is why build integrity must be verifiable. Provenance should be recorded and tied to specific systems and identities. Build steps should be signed and attested. Promotion gates should require verification of those attestations before artifacts move forward.
Trust must be anchored in the build output, not assumed from the source input.
Why Pipelines Must Be Treated as Untrusted
CI/CD pipelines are often viewed as automation tools, but they are in fact highly privileged systems that bridge development and production. They hold secrets, manage deployment logic, and often operate with broad permissions across infrastructure.
The webinar discussion stressed that pipelines must be treated as untrusted environments by default. This does not imply mistrust of developers, but rather recognition that any high-privilege system is an attractive target.
Policy-as-code frameworks, strict RBAC, auditability, and enforcement of mandatory security checks ensure that controls cannot be disabled under pressure to ship. Developers may unintentionally bypass safeguards when under deadlines. Governance mechanisms must therefore be systemic, not optional.
In complex environments where multiple tools—GitHub Actions, Jenkins, Docker, Kubernetes—are integrated together, misconfiguration becomes another source of risk. Each tool has its own security model. Without centralized governance, complexity compounds vulnerability.
AI Is Expanding the Supply Chain Attack Surface
As if artifacts, pipelines, and containers were not enough, AI-native applications are adding an entirely new dimension to supply chain security.
Modern applications increasingly rely on Large Language Models, prompt libraries, embeddings, model weights, and training datasets. These components influence runtime behavior in ways that traditional code does not. Yet they are rarely tracked or governed with the same rigor as open-source dependencies.
The concept of an “AI Bill of Materials” is emerging, but no standardized framework currently exists. Organizations are integrating AI features faster than governance standards can keep pace.
The risks differ from traditional CVEs. Poisoned training data can subtly manipulate model behavior. Backdoored model weights can introduce hidden functionality. Prompt injection attacks can trick systems into exposing sensitive information. Shadow AI systems may be deployed without formal oversight.
Unlike deterministic software, AI systems produce probabilistic outputs. Static security testing does not fully address this unpredictability. Security teams must now consider model provenance, data lineage, vendor trust, and runtime behavior monitoring as part of the supply chain equation.
Even the build-versus-buy decision for LLMs becomes a supply chain governance choice. Building offers control but introduces operational burden and long-term responsibility. Buying accelerates deployment but increases trust dependency on external vendors. In both cases, AI components extend the trust fabric and must be governed accordingly.
A Practical Framework for End-to-End Supply Chain Security
Moving beyond SCA requires structured controls across the full lifecycle of delivery.
Ingest-Time Controls ensure that risky packages and images are prevented from entering developer workflows in the first place through dependency firewalls, upstream proxy governance, and vendor controls.
Build-Time Integrity requires signed environments, provenance attestations, and enforcement of SLSA-style compliance so that artifacts can be cryptographically tied to verified build processes.
Promotion-Time Governance introduces artifact registry gating, quarantine workflows, and policy enforcement to prevent unauthorized or tampered artifacts from advancing to production.
Runtime Verification ensures continuous monitoring of deployment health, secret usage, and, increasingly, AI behavior to detect anomalous activity after release.
This layered approach transforms supply chain security from a reactive scanning function into an operational control system embedded directly into software delivery workflows.
From Visibility to Control
Software supply chain security has evolved.
It is no longer an open-source vulnerability problem alone. It is a trust management challenge spanning artifacts, pipelines, containers, vendors, and AI components.
Organizations that succeed will not stop at generating reports. They will enforce policy at every stage. They will treat CI/CD as privileged infrastructure. They will require attestations before promotion. They will govern ingestion and monitor runtime behavior. They will extend security controls into AI-native systems.
Supply chain security must move beyond visibility. It must deliver enforceable control across the entire software delivery lifecycle. Software supply chain security isn’t about scanning more. It’s about governing every stage of software delivery from code to artifact to pipeline to production to AI.
Ready to see how Harness embeds supply chain security directly into CI/CD, artifact governance, and AI-powered verification?
Explore Harness Software Supply Chain Security solutions and secure your delivery pipeline end-to-end.
FAQs
Is SCA enough for software supply chain security?
No. SCA provides visibility into open-source vulnerabilities but does not protect CI/CD pipelines, artifact integrity, container ecosystems, or AI components.
Why are CI/CD pipelines considered high-risk?
Pipelines hold credentials, signing keys, and deployment paths. A compromised runner can inject malicious artifacts or exfiltrate secrets.
What is artifact governance?
Artifact governance includes registry gating, quarantine workflows, attestation verification, and policy enforcement before artifacts are promoted or deployed.
What is an AI Bill of Materials (AI-BOM)?
An AI-BOM would catalog AI components such as models, prompts, embeddings, and training data. Standards are still emerging.
How do supply chain attacks bypass SCA?
They exploit ingestion workflows, build steps, compromised pipelines, or malicious container images — rather than known CVEs.
Should organizations build or buy LLMs?
Build offers control but high cost and operational burden. Buy offers speed and vendor expertise but introduces trust and governance risks.


From Artifact Storage to Supply Chain Control: Rethinking Artifact Management with Harness
From Artifact Storage to Supply Chain Control: Rethinking Artifact Management with Harness
Harness Artifact Registry marks an important milestone as it evolves from universal artifact management into an active control point for the software supply chain. With growing enterprise adoption and new security and governance capabilities, Artifact Registry is helping teams block risky dependencies before they reach the pipeline, reduce supply chain exposure, and scale artifact management without slowing developers down.
In little over a year, Harness Artifact Registry has grown from early discovery to strong enterprise adoption, supporting a wide range of artifact formats, enterprise-scale storage, and high-throughput CI/CD pipelines across both customers and internal teams. What started as a focused initiative inside Harness has evolved into a startup within a startup, quickly becoming a core pillar of the Harness platform.
Today, we’re sharing how Artifact Registry is helping organizations scale software delivery by simplifying artifact management, strengthening supply chain security, and improving developer experience and where we’re headed next.
Building a Modernized, Cloud Native Artifact Management
In customer conversations, one theme came up repeatedly: as organizations scale CI/CD, artifacts multiply fast. Containers, packages, binaries, Helm charts, and more end up spreading across fragmented tools with inconsistent controls. Teams don't want just another registry. They want one trusted system, deeply integrated with CI/CD, that can scale globally and enforce policy by default. That's exactly what the Artifact Registry was built to be. By embedding artifact management directly into the Harness platform, it reduces tooling sprawl while giving platform engineering, DevOps, and AppSec teams centralized visibility and control, without slowing developers down.
Artifact Registry: A Unified Home for Every Artifact
Today, Artifact Registry supports a growing ecosystem of artifact types, with Docker, Helm (OCI), Generic, Python, npm, Go, NuGet, Dart, Conda, PHP Composer, and AI artifacts now available, and more on the way. With Artifact Registry, teams can:
- Centralize all artifacts across CI and CD in one platform-native registry
- Scale globally with multi-region replication for performance and resilience
- Simplify migration with built-in tooling to move from existing registries
- Deliver faster, more reliable artifact pulls across environments
The business impact is already clear. Artifact Registry has quickly gained traction with several enterprise customers, driven by strong platform integration, low-friction adoption, and the advantage of having artifact management natively embedded within the CI/CD platform.

One early customer managing artifacts across Docker, Helm, Python, NPM, Go, and more has standardized on Harness Artifact Registry, achieving 100% CI adoption across teams and pipelines.
“Harness Artifact Registry is stable, performant, and easy to trust at scale, delivering faster and more reliable artifact pulls than our previous vendor”
— SRE Lead
By unifying artifact storage with the rest of the software delivery lifecycle, Artifact Registry simplifies operations while helping teams focus on shipping software.
Shifting from Passive Storage to Active Governance
Software supply chain threats have become both more frequent and more sophisticated. High-profile incidents like the SolarWinds breach, where attackers injected malicious code into trusted update binaries affecting thousands of organizations, exposed how deeply a compromised artifact can penetrate enterprise systems. More recently, the Shai-Hulud 2.0 campaign saw self-propagating malware compromise hundreds of npm packages and tens of thousands of downstream repositories, harvesting credentials and spreading automatically through development environments.
As these attacks show, risk doesn’t only exist after a build, it can be embedded long before artifacts reach CI/CD pipelines. That’s why Harness Artifact Registry was designed with governance at its core.
Blocking Risky Dependencies Before They Reach Your Pipeline
Harness Artifact Registry includes Dependency Firewall, a control point that allows organizations to govern which dependencies are allowed into their environment in the first place. Rather than relying on downstream scans after a package has already been pulled into CI/CD, Dependency Firewall evaluates dependency requests at ingest using policy-based controls.
This allows teams to proactively block risky artifacts before they are ever downloaded. Organizations can prevent the use of dependencies with known CVEs or license violations, blocking risky dependencies before they reach your pipeline, and restrict access to untrusted or unsafe upstream sources by default. The result is earlier risk reduction, fewer security exceptions later in the pipeline, and stronger alignment between AppSec and development teams without slowing delivery.
[Dependency Firewall Explainer Video]
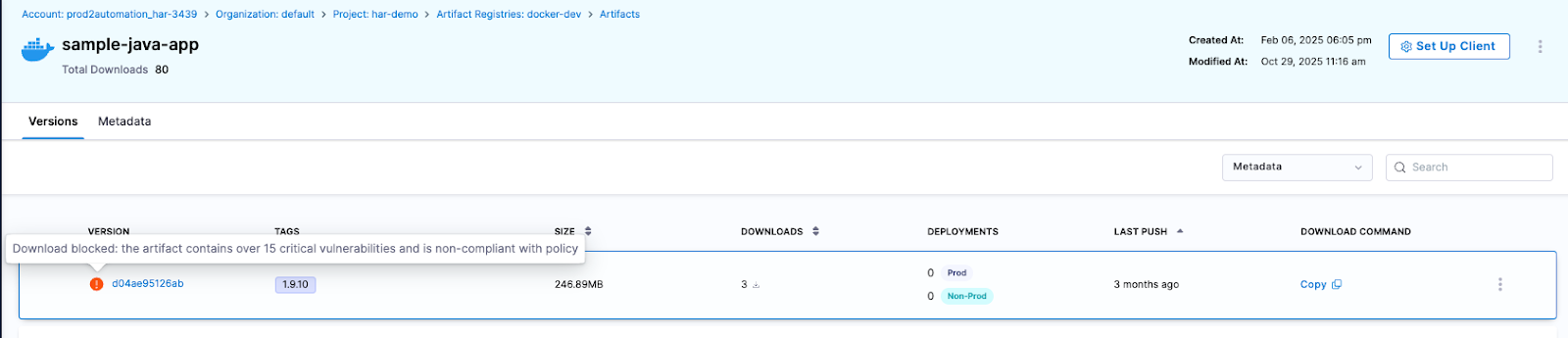
Automatically Blocking Risky Artifacts Before Deployment
To further strengthen supply chain protection, Artifact Registry provides built-in artifact quarantine, allowing organizations to automatically block artifacts that fail security or compliance checks. Quarantined artifacts cannot be downloaded or deployed until they meet defined policy requirements, helping teams stop risk before it moves downstream. All quarantine actions are policy-driven, fully auditable, and governed by RBAC, ensuring that only authorized users or systems can quarantine or release artifacts.
Integrating Security into Existing Scanning Workflows
Rather than forcing teams to replace the tools they already use, Harness Artifact Registry is built to fit into real-world security workflows by unifying scanning and governance at the registry layer. Today, Artifact Registry includes built-in scanning powered by Aqua Trivy for vulnerabilities, license issues, and misconfigurations, and integrates with over 40 security scanners, including tools like Wiz, for container, SCA, and compliance checks. Teams can orchestrate these scans directly in their CI pipelines, with scan results feeding into policy evaluation to automatically determine whether an artifact is released or quarantined.
Artifact Registry also exposes APIs that allow external security and ASPM platforms to trigger quarantine or release actions based on centralized policy decisions. Together, these capabilities enable organizations to enforce consistent, policy-driven controls early, stop risky artifacts before they move downstream, and connect artifact governance to broader enterprise security workflows all without slowing down developers.
How Artifact Registry Is Transforming Software Delivery
As organizations scaled, legacy registries have become bottlenecks disconnected from CI/CD, security, and governance workflows. Harness takes a different approach. Because Artifact Registry is natively integrated into the Harness platform, teams benefit from:
- Native CI/CD integration with no extra tooling
- Fast and seamless adoption for existing Harness customers
- Shared visibility across Platform, DevOps, and AppSec teams
- Security enforced early through built-in governance and Dependency Firewall
This tight integration has accelerated adoption by removing friction from day-to-day workflows. Teams are standardizing how artifacts are secured, distributed, and governed across the software delivery lifecycle, while keeping developer workflows fast and familiar.
What’s Next for Artifact Registry?
Harness Artifact Registry was built to modernize artifact management for the enterprise, combining high-performance distribution with built-in security, governance, and visibility. We’ve continued to invest in a platform designed to scale with modern delivery pipelines and we’re just getting started.
Looking ahead, we’re expanding Artifact Registry in three key areas:
Package Ecosystem Expansion
Support is coming for Alpine, Debian, Swift, RubyGems, Conan, and Terraform packages, enabling teams to standardize more of their software supply chain on a single platform.
Governance, Security, and Operational Control
We’re investing in artifact lifecycle management, immutability, audit logging, storage quota controls, and deeper integration with Harness Security Solutions.
AI, Visibility, and Integrations
Upcoming capabilities include semantic artifact discovery, custom dashboards, AI-powered chat, OSS gatekeeper agents, and deeper integration with Harness Internal Developer Portal.
Modern software delivery demands clear control over how software is built, secured, and distributed. As supply chain threats increase and delivery velocity accelerates, organizations need earlier visibility and enforcement without introducing new friction or operational complexity.
We invite you to sign up for a demo and see firsthand how Harness Artifact Registry delivers high-performance artifact distribution with built-in security and governance at scale.


Harness Artifact Registry: Your Unified OCI-Compliant Gateway for Secure Artifact Management
If you've worked with builds and deployments, then you already know how central Docker images, dependencies, and containers are to modern software delivery. The introduction of Docker revolutionised how we package and run software, while the Open Container Initiative (OCI) brought much-needed standardisation to container formats and distribution. Docker made containers mainstream; OCI made them universal.
Even though Docker Hub and private registries have served us well, they often introduce challenges at scale:
- Limited governance and control — OCI defines standards, but managing how standardised images are used, updated, and secured across environments is often left to manual processes.
- Security at the edge instead of by design — vulnerability scans and policy checks typically happen after the fact, leaving pipelines exposed to build failures or compromised dependencies.
- Exposure to supply chain risks — even perfectly built artifacts can fall victim to typosquatting or malicious dependency injection, quietly introducing malware into trusted environments.
And even after every dependency and sanity check passes, one question remains:
How effectively can you integrate and deploy artifacts through your CI/CD supply chain, without risking credential leaks or losing end-to-end visibility?
The Problems Are Clear — So Is the Solution
This is exactly where Harness Artifact Registry comes in.
Harness Artifact Registry is a cloud-native, secure artifact storage and management platform built for the future. Unlike traditional Docker registries or basic container registries, it's designed not just to store your Docker images and artifacts but also to actively secure and govern them. It's fully OCI-compliant, supporting Docker containers and other container formats natively, whilst integrating directly with CI/CD pipelines, policy engines, and vulnerability scanners.
Let me walk you through the complete journey of how an artifact moves through Harness Artifact Registry, from the moment you build it to when it's deployed in production.
The OCI-Compliant Artifact Journey

Docker Registry Client Setup
It all begins with the very first step after you build your Docker image on your system: storing it in a secure artifact storage layer through your container registry. Harness Artifact Registry supports more than 16 registry types and is fully OCI-compliant. You can simply use Docker to push the artifacts into the registry or even use the Harness CLI for it.
It is as simple as pushing to Docker Hub. Once you've authenticated with your Harness Artifact Registry, you can use standard Docker commands to push Docker images:
# Step 1: Tag the existing image (using its digest) with a new tag
docker tag <REGISTRY_URL>/<REPOSITORY>/<IMAGE_NAME>@<DIGEST> <REGISTRY_URL>/<REPOSITORY>/<IMAGE_NAME>:<NEW_TAG>
# Step 2: Push the newly tagged image to the registry
docker push <REGISTRY_URL>/<REPOSITORY>/<IMAGE_NAME>:<NEW_TAG>
Because Harness Artifact Registry is fully OCI-compliant, it works seamlessly with any OCI-compatible client. This means you don't need to learn new tools or change your existing Docker workflows. Whether you're migrating from Google Artifact Registry, Azure Container Registry, AWS ECR, or Docker Hub, the experience remains consistent.
Pulling from External Resources
We understand that a build requires many dependencies and versioning, with some even pulling from open-source repositories. These sources can vary significantly for enterprises. That's why we've made it easy to integrate custom registries so you can cache artifacts via a proxy.
Harness Artifact Registry allows you to configure upstream registries as remote repositories. This means you can:
- Cache dependencies locally to reduce external network calls and improve build times
- Control access to external Docker registries and artifact repositories through a single point of entry
- Scan external artifacts before they enter your environment
Apart from Docker Hub, Google Artifact Registry, and AWS ECR, you can set up custom registries with just a Remote Registry URL and basic authentication using a username and password. This proxy capability ensures that even when your teams pull Docker images from public registries, everything flows through Harness Artifact Registry first, giving you complete visibility, governance, and unified artifact storage control.
Security by Design
This is where Harness Artifact Registry truly shines. Rather than treating security as an afterthought, it's baked into every layer of the artifact lifecycle.
Built-in Container Scanners
Container vulnerability scanners detect security issues in your Docker images and container images before they can cause problems. Harness Artifact Registry integrates with industry-leading scanners like Aqua Trivy and Snyk, allowing you to automatically scan every artifact that enters your registry.
Here's what makes this powerful: when a Docker image is pushed, Harness automatically triggers a security pipeline that scans the artifact and generates a complete Software Bill of Materials (SBOM) along with detailed vulnerability reports. You get immediate visibility into:
- Known CVEs (Common Vulnerabilities and Exposures) with severity ratings
- All packages and libraries included in the Docker image
- Outdated dependencies and their versions
- Licence compliance issues
- Configuration vulnerabilities
The SBOM and vulnerability details are displayed directly in the Harness interface, giving you complete transparency into what's inside your containers and their security posture. This level of container security goes beyond what traditional Docker registries offer.
Dependency Firewall
When you're pulling dependencies from external sources through the upstream proxy, the Dependency Firewall actively blocks risky or unapproved packages before they even enter your registry. You can configure it to either block suspicious dependencies outright or set it to warn mode for your team to review. This means malicious dependencies are stopped at the gate, not discovered later in your pipeline.
Policy Sets
Beyond vulnerability scanning, you can assign policy sets to be evaluated against each artifact. These policies act as automated gatekeepers, enforcing your organisation's security and compliance requirements.
For example, you might create policies that:
- Block Docker images with critical vulnerabilities from being deployed
- Require all container images to be signed
- Enforce naming conventions for artifacts
- Mandate specific base images for Docker containers
Policies are evaluated automatically, and non-compliant artifacts can be quarantined or blocked entirely.
Quarantine
When an artifact fails a security scan or violates a policy, it can be automatically quarantined. This prevents it from being used in deployments whilst still allowing your team to investigate and remediate the issues. This proactive approach significantly reduces your attack surface and ensures only verified artifacts make it to production.
Integrating with Harness CI/CD Pipelines
Your artifact is now ready, fully scanned for vulnerabilities, and stored securely in your container registry. This is where everything comes together for developers and platform engineers alike. The seamless integration between Harness Artifact Registry and Harness CI/CD pipelines means you can build Docker images, store artifacts, and deploy without context switching or managing complex credentials across multiple registry systems.

Building and Publishing with Harness CI
Harness CI is all about getting your code built, tested, and packaged efficiently. Harness Artifact Registry fits naturally into this workflow by providing native steps that eliminate the complexity of managing Docker registry credentials and connections.
Build and Push to Docker: This native CI step allows you to build your Docker images and push them directly to Harness Artifact Registry without any external connectors. The platform handles Docker registry authentication automatically, so you can focus on your build logic rather than credential management.
Upload artifacts: Beyond Docker images, you can publish Maven artifacts, npm packages, Helm charts, or generic files directly to Harness Artifact Registry. This unified artifact management approach means all your build outputs live in one place, with consistent vulnerability scanning and policy enforcement across every artifact type.
The essence here is simplicity: your CI pipeline produces artifacts and Docker containers, and they're automatically stored, scanned, and made available for deployment, all within the same platform.
Deploying with Harness CD
Every deployment needs an artifact. Whether you're deploying Docker containers to Kubernetes, AWS ECS, Google Cloud Run, or traditional VMs, your deployment pipeline needs to know which version of your application to deploy and where to get it from.
This is where Harness Artifact Registry becomes invaluable. Because it's natively integrated with Harness CD, your deployment pipelines can pull Docker images and artifacts directly without managing external Docker registry credentials or complex authentication flows.
Harness CD supports numerous deployment types (often called CD swimlanes), and Harness Artifact Registry works seamlessly with all of them. When you configure a CD service, you simply select Harness Artifact Registry as your artifact source, specify which container registry and artifact to use, and define your version selection criteria.
From there, the deployment pipeline handles everything: authenticating with the registry, pulling the correct Docker image version, verifying it's passed vulnerability scans and security checks, and deploying it to your target environment. You can deploy to production with strict version pinning for stability, or to non-production environments with dynamic version selection for testing. The choice is yours, and it's all configured through the same intuitive interface.
The real power lies in the traceability. Every deployment is logged with complete details: which artifact version was deployed, when, by whom, and to which environment. If you need to roll back, the previous Docker image versions are right there, ready to be redeployed.
Why This Matters
From the moment you build a Docker image to when it's running in production, Harness Artifact Registry provides a complete, secure, and governed artifact lifecycle. You get container security that prevents issues before they occur, complete visibility through SBOM generation and audit logs, and native CI/CD integration that eliminates the complexity of managing multiple Docker registries and credentials.
This isn't just about storing Docker images. It's about building confidence in your software supply chain with a secure, OCI-compliant container registry.
In a world where supply chain attacks are increasingly common and compliance requirements continue to grow, having a robust artifact management and container registry strategy is essential. Harness Artifact Registry delivers that strategy through a platform that's both powerful and intuitive.
Whether you're a developer pushing your first Docker image, a platform engineer managing deployment pipelines, or a security professional ensuring compliance, Harness Artifact Registry provides the tools you need to move fast without compromising on security.
Ready to experience a fully OCI-compliant Docker registry with built-in vulnerability scanning, dependency firewall, and seamless CI/CD integration? Explore Harness Artifact Registry and see how it transforms your software delivery pipeline with secure artifact management.


Reimagining Artifact Management for DevSecOps: Harness Artifact Registry GA
Today, Harness is announcing the General Availability of Artifact Registry, a milestone that marks more than a new product release. It represents a deliberate shift in how artifact management should work in secure software delivery.
For years, teams have accepted a strange reality: you build in one system, deploy in another, and manage artifacts somewhere else entirely. CI/CD pipelines run in one place, artifacts live in a third-party registry, and security scans happen downstream. When developers need to publish, pull, or debug an artifact, they leave their pipelines, log into another tool, and return to finish their work.
It works, but it’s fragmented, expensive, and increasingly difficult to govern and secure.
At Harness, we believe artifact management belongs inside the platform where software is built and delivered. That belief led to Harness Artifact Registry.
A Startup Inside Harness
Artifact Registry started as a small, high-ownership bet inside Harness and a dedicated team with a clear thesis: artifact management shouldn’t be a separate system developers have to leave their pipelines to use. We treated it like a seed startup inside the company, moving fast with direct customer feedback and a single-threaded leader driving the vision.The message from enterprise teams was consistent: they didn’t want to stitch together separate tools for artifact storage, open source dependency security, and vulnerability scanning.
So we built it that way.
In just over a year, Artifact Registry moved from concept to core product. What started with a single design partner expanded to double digit enterprise customers pre-GA – the kind of pull-through adoption that signals we've identified a critical gap in the DevOps toolchain.
Today, Artifact Registry supports a broad range of container formats, package ecosystems, and AI artifacts, including Docker, Helm (OCI), Python, npm, Go, NuGet, Dart, Conda, and more, with additional support on the way. Enterprise teams are standardizing on it across CI pipelines, reducing registry sprawl, and eliminating the friction of managing diverse artifacts outside their delivery workflows.
One early enterprise customer, Drax Group, consolidated multiple container and package types into Harness Artifact Registry and achieved 100 percent adoption across teams after standardizing on the platform.
As their Head of Software Engineering put it:
"Harness is helping us achieve a single source of truth for all artifact types containerized and non-containerized alike making sure every piece of software is verified before it reaches production." - Jasper van Rijn
Why This Matters: The Registry as a Control Point
In modern DevSecOps environments, artifacts sit at the center of delivery. Builds generate them, deployments promote them, rollbacks depend on them, and governance decisions attach to them. Yet registries have traditionally operated as external storage systems, disconnected from CI/CD orchestration and policy enforcement.
That separation no longer holds up against today’s threat landscape.
Software supply chain attacks are more frequent and more sophisticated. The SolarWinds breach showed how malicious code embedded in trusted update binaries can infiltrate thousands of organizations. More recently, the Shai-Hulud 2.0 campaign compromised hundreds of npm packages and spread automatically across tens of thousands of downstream repositories.
These incidents reveal an important business reality: risk often enters early in the software lifecycle, embedded in third-party components and artifacts long before a product reaches customers.When artifact storage, open source governance, and security scanning are managed in separate systems, oversight becomes fragmented. Controls are applied after the fact, visibility is incomplete, and teams operate in silos. The result is slower response times, higher operational costs, and increased exposure.
We saw an opportunity to simplify and strengthen this model.

By embedding artifact management directly into the Harness platform, the registry becomes a built-in control point within the delivery lifecycle. RBAC, audit logging, replication, quotas, scanning, and policy enforcement operate inside the same platform where pipelines run. Instead of stitching together siloed systems, teams manage artifacts alongside builds, deployments, and security workflows. The outcome is streamlined operations, clearer accountability, and proactive risk management applied at the earliest possible stage rather than after issues surface.
Introducing Dependency Firewall: Blocking Risk at Ingest
Security is one of the clearest examples of why registry-native governance matters.
Artifact Registry delivers this through Dependency Firewall, a registry-level enforcement control applied at dependency ingest. Rather than relying on downstream CI scans after a package has already entered a build, Dependency Firewall evaluates dependency requests in real time as artifacts enter the registry. Policies can automatically block components with known CVEs, license violations, excessive severity thresholds, or untrusted upstream sources before they are cached or consumed by pipelines.
Artifact quarantine extends this model by automatically isolating artifacts that fail vulnerability or compliance checks. If an artifact does not meet defined policy requirements, it cannot be downloaded, promoted, or deployed until the issue is addressed. All quarantine and release actions are governed by role-based access controls and fully auditable, ensuring transparency and accountability. Built-in scanning powered by Aqua Trivy, combined with integrations across more than 40 security tools in Harness, feeds results directly into policy evaluation. This allows organizations to automate release or quarantine decisions in real time, reducing manual intervention while strengthening control at the artifact boundary.
The result is a registry that functions as an active supply chain control point, enforcing governance at the artifact boundary and reducing risk before it propagates downstream.
The Future of Artifact Management is here
General Availability signals that Artifact Registry is now a core pillar of the Harness platform. Over the past year, we’ve hardened performance, expanded artifact format support, scaled multi-region replication, and refined enterprise-grade controls. Customers are running high-throughput CI pipelines against it in production environments, and internal Harness teams rely on it daily.
We’re continuing to invest in:
- Expanded package ecosystem support
- Advanced lifecycle management, immutability, and auditing
- Deeper integration with Harness Security and the Internal Developer Portal
- AI-powered agents for OSS governance, lifecycle automation, and artifact intelligence
Modern software delivery demands clear control over how software is built, secured, and distributed. As supply chain threats increase and delivery velocity accelerates, organizations need earlier visibility and enforcement without introducing new friction or operational complexity.
We invite you to sign up for a demo and see firsthand how Harness Artifact Registry delivers high-performance artifact distribution with built-in security and governance at scale.


Best Artifact Repository Tools
What are Artifact Repository Tools?
Artifact repository tools, also known as artifact registries and artifact management systems, are specialized software platforms designed to store and manage binary artifacts generated during the software development lifecycle. These artifacts can include compiled code, libraries, container images, and other deployable components. By providing a centralized location for these assets, artifact repository tools streamline the development process, enhance collaboration, and ensure consistency across different stages of software delivery.
Key features of artifact repository tools include:
Versioning Support
Robust versioning capabilities are a cornerstone of artifact repository tools. They allow teams to maintain multiple versions of artifacts, track changes over time, and easily roll back to previous versions if needed. This feature is crucial for maintaining software integrity and supporting concurrent development efforts.
Retention
Artifact repository tools offer configurable retention policies, enabling organizations to define how long artifacts should be stored. This helps in managing storage costs and complying with regulatory requirements while ensuring that critical artifacts remain accessible when needed.
Quality & Security Tracking
Artifact registries may integrate with CI/CD platforms, testing tools and (most notably) security scanning tools to understand how artifacts have been tested and scanned. The quality and security telemetry may be used to govern how the artifacts are used in the organization.
User Permissions
Granular access control is essential in artifact management. Repository tools provide sophisticated user permission systems, allowing administrators to define who can view, upload, or modify artifacts. This ensures that sensitive components are protected and that team members have appropriate levels of access.
Promotion
The ability to promote artifacts through different stages of the software lifecycle is a key feature of many repository tools. This functionality supports the progression of artifacts from development to testing, staging, and production environments, maintaining traceability and consistency throughout the process.
High Availability and Speed
To support mission-critical operations, artifact repository tools often offer high availability configurations. This ensures that artifacts remain accessible even in the event of hardware failures or other disruptions, minimizing downtime and maintaining productivity.
Benefits of Artifact Repository Tools
The adoption of artifact repository tools brings numerous advantages to development teams and organizations. Let's explore some of the key benefits:
Dependency Management
One of the primary benefits of artifact repository tools is their ability to streamline dependency management. By providing a centralized location for all artifacts, these tools simplify the process of resolving and retrieving dependencies. This leads to faster build times, reduced errors, and improved consistency across different development environments.
Efficient Builds
Artifact repository tools contribute significantly to build efficiency. By caching frequently used artifacts locally, they reduce network bandwidth consumption and accelerate build processes. This is particularly beneficial for large-scale projects or distributed teams working across different geographical locations.
Release Stability
By maintaining a clear history of artifact versions and their dependencies, repository tools enhance release stability. Teams can easily reproduce builds, track changes, and ensure that the correct versions of components are used in each release. This traceability is invaluable for troubleshooting issues and maintaining software quality.
Audit
Artifact repository tools provide comprehensive audit trails, recording who accessed or modified artifacts and when. This feature is crucial for compliance purposes, security reviews, and maintaining accountability within development teams. It allows organizations to track the usage of artifacts throughout their lifecycle and identify potential security risks or policy violations.
Artifact Repository Tools
The market offers a diverse range of artifact repository tools, each with its own strengths and specializations. Here's an overview of some popular options:
Amazon Elastic Container Registry (ECR)
Amazon ECR is a fully-managed Docker container registry that makes it easy for developers to store, manage, and deploy Docker container images. It integrates seamlessly with other AWS services, providing a scalable solution for container-based workloads.
Archiva
Apache Archiva is an extensible repository management software that helps managing your binary artifacts. It's designed to be a central repository for project artifacts, providing features like security and configuration management.
Bower
Bower, while primarily a package manager for web projects, also serves as a repository for front-end components. It simplifies the process of managing and versioning client-side dependencies.
CloudRepo
CloudRepo offers a cloud-based artifact repository solution, supporting various package formats including Maven, npm, and Docker. It provides a user-friendly interface and integrates with popular CI/CD tools.
Cloudsmith
Cloudsmith is a cloud-native package management platform that supports a wide range of package formats. It offers advanced features like vulnerability scanning and license compliance checks.
Dist
Dist is a lightweight, open-source artifact repository that focuses on simplicity and ease of use. It's particularly well-suited for small to medium-sized teams looking for a straightforward solution.
Docker
Docker Hub, while primarily known as a container registry, also serves as an artifact repository for Docker images. It offers both public and private repositories, making it a popular choice for container-based workflows.
Harness Artifact Registry
Harness Artifact Registry is an AI-native, universal artifact management solution designed to streamline software delivery. It offers centralized artifact management, tightly integrated with CI/CD pipelines and security scans, supporting multiple artifact types in a secure, unified platform. The registry provides robust security features, including fine-grained access control, comprehensive auditing, and supply chain security measures such as SBOM generation and policy enforcement. With end-to-end traceability, automated cleanup policies, and API-driven automation, Harness Artifact Registry enables organizations to manage the full lifecycle of their artifacts while boosting developer productivity and enhancing build reliability.
JFrog Artifactory
JFrog Artifactory is a comprehensive binary repository manager that supports all major packaging formats. It offers enterprise-grade features like high availability, replication, and advanced security controls.
MyGet
MyGet provides hosted package repositories for various package types, including NuGet, npm, and Maven. It offers both public and private feeds, making it suitable for open-source projects and enterprise use cases.
Nexus
Sonatype Nexus is a popular repository manager that supports multiple artifact formats. It offers both open-source and commercial versions, providing scalable solutions for organizations of all sizes.
npm
While primarily known as the package manager for JavaScript, npm also serves as a repository for JavaScript packages. It's an essential tool for managing dependencies in Node.js projects.
NuGet
NuGet is the package manager for .NET, providing a centralized repository for .NET libraries and tools. It's deeply integrated with Visual Studio and the .NET ecosystem.
Packagecloud
Packagecloud offers a cloud-based package repository service that supports multiple formats, including DEB, RPM, and RubyGem. It provides features like automatic dependency resolution and package signing.
ProGet
ProGet, developed by Inedo, is an enterprise-grade package management solution. It supports various package types and offers advanced features like license filtering and vulnerability scanning.
PyPI
The Python Package Index (PyPI) is the official repository for Python packages. While primarily a public repository, it can also be mirrored or used as a model for private Python package repositories.
Quay
Quay, owned by Red Hat, is a container registry that provides secure storage, distribution, and management of container images. It offers features like vulnerability scanning and fine-grained access controls.
Yarn
Yarn, while primarily a package manager for JavaScript, also includes a package repository component. It offers fast, reliable, and secure dependency management for JavaScript projects.
Conclusion
Artifact repository tools are indispensable components of modern software development infrastructures. They provide a centralized, secure, and efficient means of managing software artifacts throughout the development lifecycle. By leveraging these tools, organizations can streamline their build processes, enhance collaboration, and maintain better control over their software components. As the software development landscape continues to evolve, the role of artifact repository tools in supporting agile, DevOps, and cloud-native practices will only grow in importance.
When selecting an artifact repository tool, consider factors such as supported package formats, scalability, integration capabilities, and specific features that align with your organization's workflow. Whether you opt for a cloud-based solution or an on-premises deployment, implementing a robust artifact repository tool can significantly improve your software development and delivery processes.
FAQ
What are the main features of artifact repository tools?
Artifact repository tools offer features like versioning support, configurable retention policies, quality and security tracking, granular user permissions, artifact promotion through lifecycle stages, and high availability to ensure efficient and secure management of software artifacts.
How do artifact repository tools improve dependency management?
By centralizing all artifacts, these tools simplify the resolution and retrieval of dependencies, leading to faster build times, reduced errors, and consistent environments across different development stages.
Why is versioning important in artifact repositories?
Versioning allows teams to maintain multiple artifact versions, track changes over time, and easily revert to previous versions, ensuring software integrity and supporting concurrent development efforts.
What are the benefits of using Harness Artifact Registry?
Harness Artifact Registry provides an AI-native, universal solution with centralized management, robust security features, seamless CI/CD integration, end-to-end traceability, and automated lifecycle management, enhancing developer productivity and build reliability.
How do artifact repository tools enhance security in software development?
They integrate with security scanning tools, enforce access controls, provide comprehensive audit trails, and support supply chain security measures, ensuring that artifacts are secure and compliant throughout their lifecycle.
Which artifact repository tool is best for container images?
Amazon Elastic Container Registry (ECR) and Docker Hub are excellent choices for managing container images, offering seamless integration with AWS services and robust features for storing and deploying Docker containers.
Learn more: Streamline CI/CD efficiency with artifact registry automation tools
Introducing AI-Native Harness Artifact Registry
The Power of a Universal Artifact Registry
Harness Artifact Registry is a universal hub for all your artifacts, regardless of type. By centralizing artifact management in one secure location, we're streamlining the process of handling multiple registries across various platforms and tools. This consolidation brings significant advantages to your DevOps workflow:
Key Benefits:
- Centralized Management: One place for all your artifacts.
- Simplified Workflow: Reduce complexity and streamline operations
- Enhanced Visibility: Gain a comprehensive view of all your artifacts
Supercharging Build Reliability and Developer Productivity
Harness Artifact Registry is designed to improve build reliability and speed significantly. Its strategic integration within the Harness ecosystem ensures:
- Lightning-Fast Builds: Experience faster, more consistent builds that accelerate your development cycles
- Reduced External Dependencies: Minimize reliance on external registries, improving stability and security
- Seamless Platform Integration: Enjoy effortless integration with Harness CI and CD modules for a streamlined workflow
This translates to unparalleled ease of use and traceability for developers and DevOps engineers. With the industry's most intuitive configuration process, your productivity will soar to new heights.
Fortress-Level Security and Compliance

In an era where security breaches can be catastrophic, the Harness Artifact Registry offers robust protection:
- Fine-grained Role-Based Access Control (RBAC): Ensure the right people have the proper access
- Leading Security Scanner Integrations: Proactively identify and mitigate vulnerabilities
- Advanced Supply Chain Security: Harness Supply Chain Security offers out-of-the-box integrations to safeguard your entire software supply chain.
- Comprehensive Audit Trails: Maintain visibility and accountability
These features don't just centralize your artifacts; they fortify them against threats while ensuring compliance with industry standards.
Unprecedented End-to-End Traceability
Harness Artifact Registry's end-to-end traceability is a game-changer. Track the complete journey of your artifacts from initial code commits through testing and into production release. This level of visibility is crucial for:
- Maintaining software quality
- Enhancing security measures
- Ensuring regulatory compliance
- Facilitating faster issue resolution
The Future is AI-Native

We're just getting started. Our roadmap includes AI integration throughout the Artifact Registry experience, beginning with AI-assisted search. Imagine the power of asking:
"What artifacts do I have that are insecure and deployed in production?"
And receiving instant, accurate answers. This is the future of artifact management.
Take the Next Step in Your DevOps Evolution
Harness Artifact Registry is available commercially and as part of Harness Open Source. Whether you're aiming to:
- Simplify your artifact management
- Boost DevOps efficiency
- Strengthen software supply chain security
Harness Artifact Registry is your solution.
Ready to revolutionize your artifact management and accelerate your DevOps workflow?
Sign up for a demo today and experience the power of the Harness Artifact Registry firsthand.
Join us in shaping the future of artifact management. The next chapter of your DevOps success story starts here, with the Harness Artifact Registry. If you would like to participate in our Beta program, click here: Artifact Registry.
Learn more: Streamline CI/CD efficiency with artifact registry automation tools
Checkout Harness Artifact Registry
.svg)