Key takeaway
This guide explores how modern Artifact Registries like Harness AR enhance developer productivity by streamlining artifact management, accelerating CI/CD pipelines, and strengthening software supply chain security. Learn practical strategies to optimize your development workflow with efficient binary repository management.
Why does Artifact Registry developer experience matter when a single missing dependency can cascade into hours of blocked builds across twenty teams?
Last Tuesday at 2 PM, your CI pipeline pulled a Python package from PyPI. This morning at 9 AM, that exact same package version disappeared from the upstream registry. Your build now fails. Your team scrambles. Your release date slips. This scenario plays out daily in engineering organizations that treat artifact management as an afterthought rather than a foundational pillar of DevOps developer productivity.
Artifacts—the versioned, immutable outputs of your CI/CD pipelines including container images, application binaries, libraries, Helm charts, and configuration files—are the building blocks of modern software delivery. When these artifacts become unavailable or unreliable, the entire development workflow grinds to a halt.
The problem extends beyond availability. Without proper artifact versioning best practices, teams cannot reproduce builds from six months ago. Without container registry performance optimization, developers wait minutes for layers that should take seconds. Without CI/CD artifact management guardrails, anyone can publish anything, introducing supply chain risks that security teams discover only after production deployment.
Developer experience suffers most when artifact workflows create friction at every step: publishing requires manual approval processes, consuming means navigating inconsistent package formats across different repositories, and debugging dependency issues becomes archaeological work through scattered logs and undocumented version changes.
The Real Cost of Poor Artifact Management
Consider a typical mid-sized engineering team:
- 150 developers across 8 teams
- 300 microservices deployed daily
- 1,200 builds executed per day
- 5 different artifact types (containers, npm, Maven, Python, Helm)
If each developer loses just 15 minutes daily to artifact-related friction:
- 37.5 hours lost per day across the team
- 187.5 hours lost per week
- 9,750 hours lost annually (equivalent to 5 full-time engineers)
At an average engineering cost of $150/hour, that's $1.46 million annually in lost productivity. And this doesn't account for delayed releases, security incidents, or infrastructure waste.
Why Artifact Management Directly Shapes Developer Productivity
Artifact management in DevOps is the practice of systematically storing, versioning, securing, and distributing software artifacts across the entire software delivery pipeline. It ensures that the same tested artifact moves through development, staging, and production environments without modification, enabling reproducible builds and reliable deployments.
Traditional binary repository management approaches assume artifacts are commodities. Store them. Retrieve them. Move on. This model collapses under modern development velocity where a single application might consume hundreds of dependencies from dozens of sources, rebuild multiple times daily, and deploy across hybrid cloud environments.
Developers lose time to predictable friction points. Builds fail because upstream registries rate-limit requests during peak hours. Deployments break because someone accidentally overwrote an artifact tag. Security scans block releases because nobody enforced immutability rules earlier in the pipeline. Each friction point compounds. A three-minute delay per build becomes thirty minutes daily when multiplied across a team. That scales to hours monthly, days annually.
The cognitive load matters as much as the time cost. When developers cannot trust that artifact dependencies remain stable, they build workarounds: local caches that drift from production, manual verification steps that slow automation, shadow repositories that bypass governance. These workarounds create technical debt that platform teams inherit.
Common Developer Pain Points
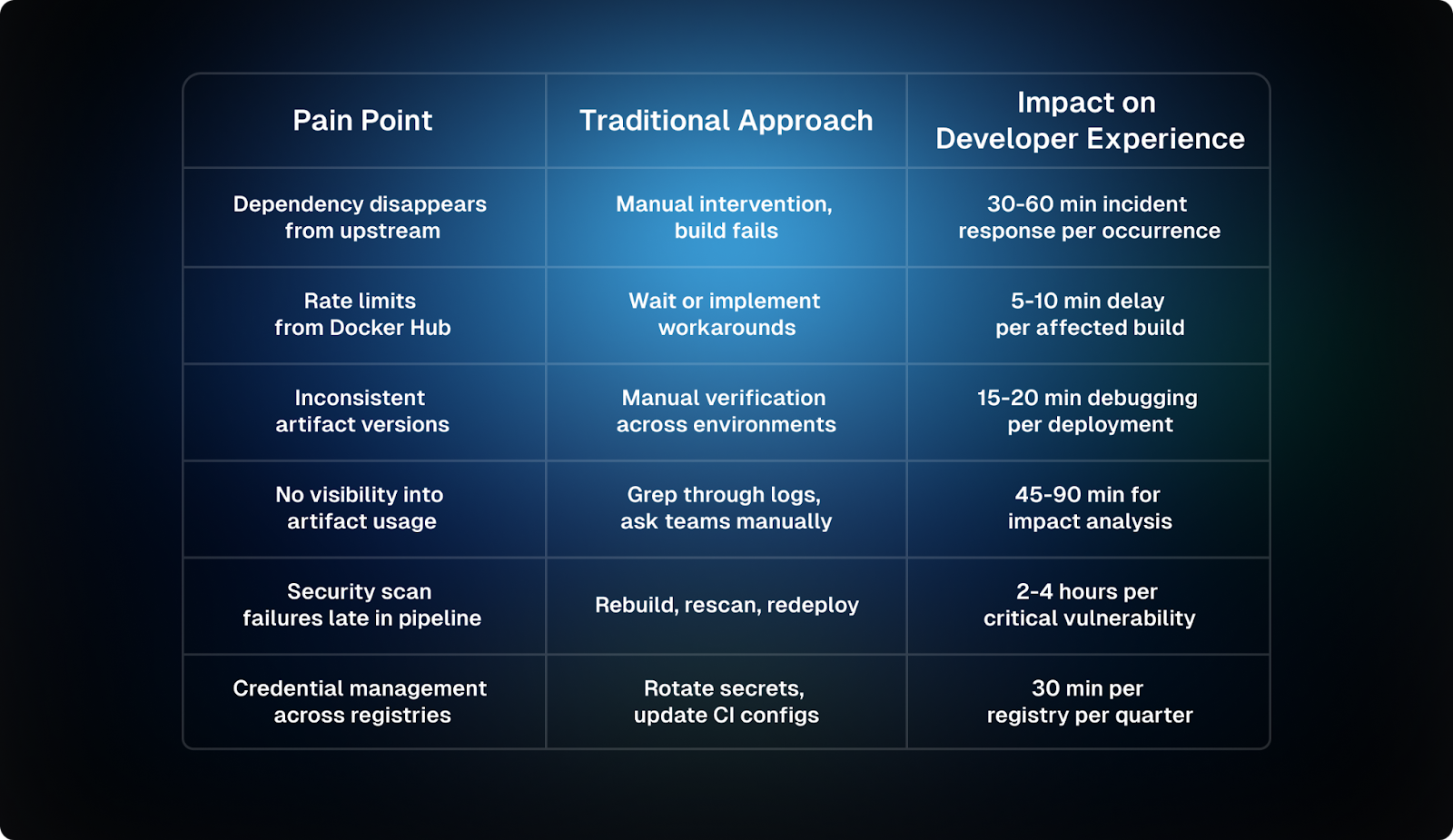
The Hidden Costs of Fragmented Artifact Registry Developer Experience
Software supply chain security begins at artifact ingestion, not during deployment scanning. Every external dependency represents a potential compromise vector. Without unified visibility across all artifact sources, security teams cannot answer basic questions: which teams consume this library, which versions exist in production, when did this artifact first appear in our systems.
Fragmentation creates operational blind spots. Development teams pull containers from Docker Hub. Data science teams install packages from PyPI. Infrastructure teams consume Terraform modules from GitHub. Platform teams manage Helm charts in separate registries. Each silo requires different access patterns, monitoring configurations, and compliance controls. The artifact management platform becomes fifteen disconnected tools rather than one cohesive system.
Performance degradation follows fragmentation. Developers in distributed teams pull the same multi-gigabyte container layers repeatedly because no caching layer exists between remote workers and upstream registries. CI runners download identical Maven artifacts hundreds of times daily because build isolation prevents cache sharing. These inefficiencies compound at scale, translating to measurable infrastructure costs and developer frustration.
The Infrastructure Cost of Fragmentation
Real-world example: A company with 500 daily builds pulling a 2GB base image:
# Without caching
500 builds × 2GB = 1,000GB (1TB) daily egress
1TB × 30 days = 30TB monthly
# AWS egress costs: $0.09/GB after first 10TB
30TB × $0.09 = $2,700/month = $32,400/year
# With intelligent caching (95% cache hit rate)
30TB × 5% × $0.09 = $135/month = $1,620/year
Annual savings: $30,780 on network costs aloneThis doesn't include:
- Reduced build times (faster developer feedback)
- Lower CI runner costs (less compute time)
- Decreased storage costs (layer deduplication)
The Security and Governance Gap
Beyond performance and cost, fragmented artifact management creates serious security vulnerabilities:
"One of the most overlooked aspects of DevSecOps is ensuring that artifact storage itself remains tamper-proof. When artifacts are stored insecurely or exposed to unauthorized access, various risks arise: supply chain attacks, data exfiltration, regulatory and compliance issues, and operational disruptions."
— Secure Artifact Storage Practices
The stakes are real:
Supply Chain Attacks: Attackers inject malicious code into legitimate artifacts within the registry, compromising downstream software components. The SolarWinds breach demonstrated how a single compromised artifact can cascade across thousands of organizations.
Regulatory Consequences: Organizations bound by HIPAA, PCI-DSS, SOC 2, or GDPR must protect artifacts containing sensitive data. A breach leads to legal consequences, financial penalties, and reputational damage.
Operational Disruptions: Even minor registry compromises or service downtime significantly disrupt CI/CD pipelines, hampering release cycles and impacting business continuity.
What Modern Artifact Management Requires
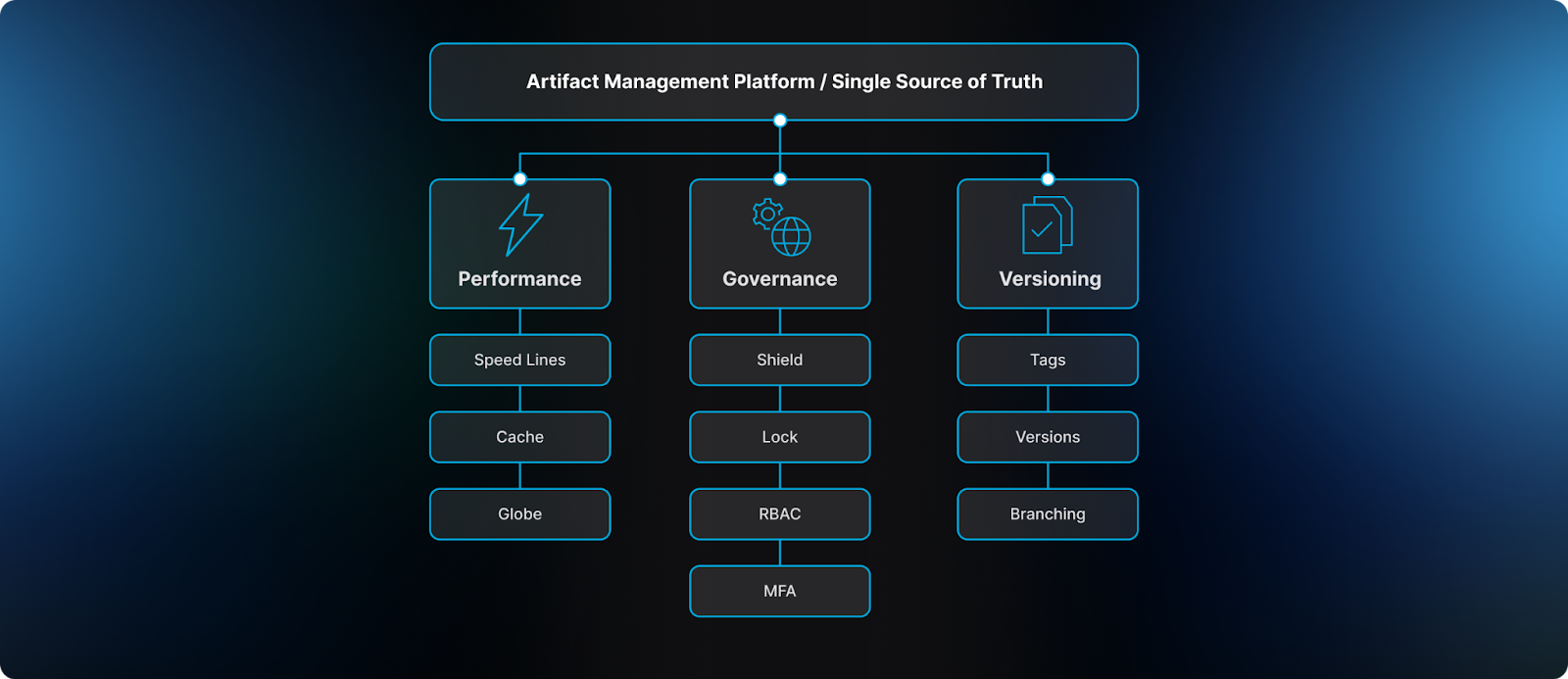
To solve these challenges, organizations need artifact management platforms—centralized systems that store, organize, and distribute software artifacts throughout the development lifecycle. These platforms act as a single source of truth for all build outputs, providing version control, access management, and security scanning for artifacts before they reach production.
Modern artifact management systems must provide:
1. High-Performance Artifact Operations
Container registry performance determines whether developers iterate quickly or wait. Layer caching strategies matter more than raw storage throughput. A well-designed Artifact Registry should deliver:
- Fast container layer pulls (seconds, not minutes)
- Efficient dependency resolution for Maven, npm, and Python packages
- Intelligent caching that reduces network costs
- Geographic distribution for global teams
2. Automated Governance Without Friction
Industry best practices recommend a "defense-in-depth" strategy, incorporating multiple layers of security controls:
Access Control and Authentication
"Access control is the cornerstone of secure artifact storage. Organizations should implement Role-Based Access Control (RBAC), mapping each user or service account to the minimal privileges required for their roles."
— Secure Artifact Storage Practices
Key principles:
- Least Privilege: Grant only minimal necessary permissions
- Federated Identity: Leverage existing identity providers (LDAP, Active Directory, SSO)
- Multi-Factor Authentication (MFA): Required for accessing critical artifacts
- Token Rotation: Short-lived tokens reduce the window for credential exploitation
Immutability and Artifact Integrity
Immutable artifacts prevent the category of bugs where "it worked yesterday" becomes an unsolvable mystery because someone silently updated a production artifact. Once published, artifacts should never change.
Encryption at Rest and in Transit
"Organizations should ensure that data remains encrypted not only when it is stored (encryption at rest) but also while it traverses networks (encryption in transit)."
— Secure Artifact Storage Practices
- TLS/SSL for data in transit: Protects against eavesdropping and tampering
- Encryption at rest: Stores artifacts on encrypted volumes
- Key management: Secure vaults, periodic rotation, limited access
Proactive Vulnerability Scanning
Security scans should happen before artifacts enter pipelines, not after they're already cached and consumed by builds.
3. Disciplined Artifact Versioning
Semantic versioning provides structure, but real-world artifact versioning requires additional discipline. Version management complexity grows with organization size. Microservices architectures generate hundreds of artifacts daily. Monorepo strategies create interdependencies between artifact versions. Without systematic artifact versioning best practices, teams lose the ability to reason about which artifact versions are compatible, which are production-eligible, and which should be deprecated.
How Harness Artifact Registry Delivers Complete Developer Experience
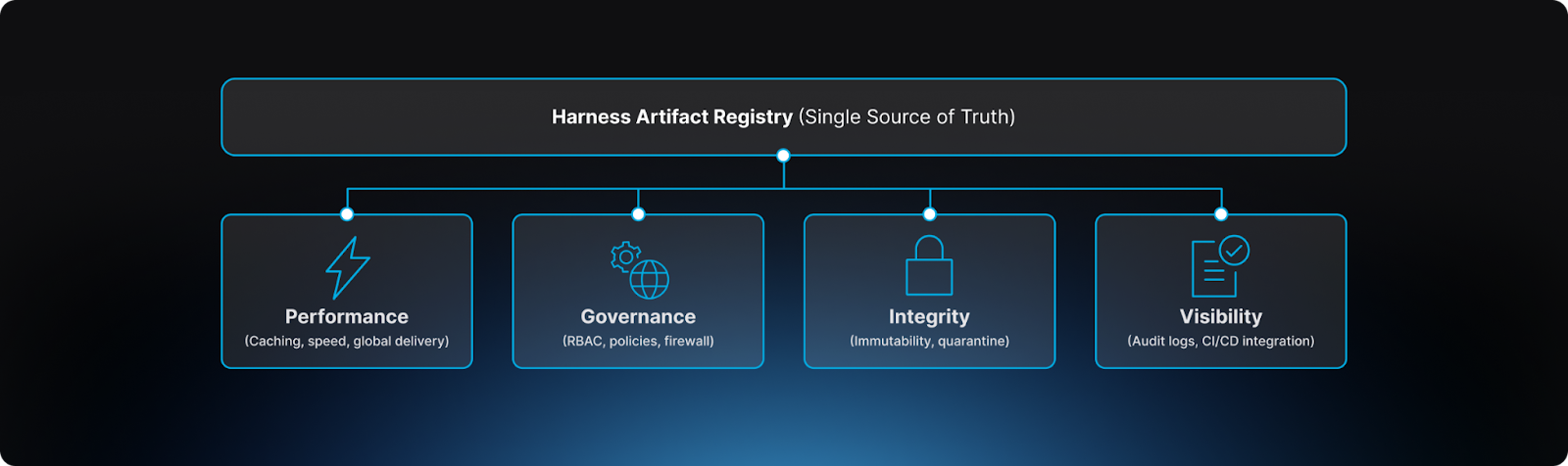
Harness Artifact Registry addresses every challenge discussed above through a unified platform designed to centralize artifact storage, enforce governance, and secure the software supply chain across engineering teams.
Unified Platform: One Registry for All Artifact Types
While organizations traditionally use various tools for artifact management—including JFrog Artifactory, Sonatype Nexus, AWS ECR, Google Artifact Registry, and Azure Container Registry—these solutions often require multiple separate registries for different artifact types or lack advanced security features like dependency firewall and automated quarantine.
Harness AR provides unified artifact management across:
- Container images (Docker, OCI-compliant)
- Helm charts for Kubernetes deployments
- Maven artifacts for Java applications
- npm packages for JavaScript projects
- Python packages (PyPI)
- Generic binaries and files
One platform. One authentication model. One security policy engine. One audit trail. This eliminates the complexity of managing multiple disconnected tools while providing enterprise-grade security and governance.
Performance: Intelligent Caching and Upstream Proxying
The platform's upstream proxy support solves the external dependency problem directly. When developers request a package from PyPI or npm, Harness AR caches it locally while maintaining the original metadata. This caching layer:
- Protects against upstream availability issues
- Eliminates Docker Hub rate limits
- Reduces network costs by 95%+
- Provides audit trail for all external dependencies
- Scans dependencies before they enter your environment
- Accelerates build times through intelligent caching
- Enables artifact lineage tracking for supply chain security
Platform teams gain visibility into all external dependencies without forcing developers to change their workflow.
Governance: Registry-Native Controls That Enable Velocity
Harness Artifact Registry transforms governance from a bottleneck into an enabler through registry-native controls that enforce policy at the artifact boundary—before dependencies enter builds, before vulnerable images reach production, before compliance violations propagate downstream.
1. Role-Based Access Control (RBAC)
Harness AR implements granular RBAC with three predefined roles:
This role-based approach enables developer workflow optimization by providing self-service capabilities while maintaining security boundaries.
2. Dependency Firewall: Blocking Risk at Ingest
"Rather than relying on downstream CI scans after a package has already entered a build, Dependency Firewall evaluates dependency requests in real time as artifacts enter the registry."
— Harness Artifact Registry GA Announcement
When a developer or CI pipeline requests an external dependency (from npm, PyPI, Maven Central, Docker Hub), Harness AR:
- Intercepts the request at the registry boundary
- Evaluates against configured policies (CVEs, license violations, severity thresholds)
- Blocks or allows based on policy results
- Caches approved dependencies for future use
- Logs all decisions for audit trails
This shifts security left without adding friction—developers get immediate feedback, security teams get enforcement guarantees, and platform teams eliminate manual review bottlenecks.
3. Immutable Repositories: Preventing Artifact Tampering
Harness AR enforces immutability at the repository level. Once an artifact is published with a specific tag or version, it cannot be modified, overwritten, or deleted outside of defined retention policies.
Benefits:
- Prevents accidental overwrites that break production
- Ensures build reproducibility (same tag = same artifact forever)
- Supports compliance requirements for artifact traceability
4. Artifact Quarantine: Automated Isolation and Remediation
When artifacts fail security or compliance checks, Harness automatically quarantines them:
"Artifact quarantine extends this model by automatically isolating artifacts that fail vulnerability or compliance checks. If an artifact does not meet defined policy requirements, it cannot be downloaded, promoted, or deployed until the issue is addressed."
— Harness Artifact Registry GA Announcement
Benefits:
- Unsafe artifacts cannot reach production
- Developers get clear remediation guidance
- Security team maintains oversight without manual gates
- Complete audit trail for compliance
5. Comprehensive Auditing and Compliance
Harness AR provides complete audit trails for every artifact operation:
Audit log captures:
- Who published which artifact, when, from which IP
- Who downloaded which artifact, when, for which deployment
- Which policies were evaluated, with what results
- Which artifacts were quarantined, by whom, and why
- Which exceptions were granted, with justification
Compliance support:
- SOC 2: Complete audit trails, access controls, encryption
- HIPAA: Data protection, access logging, retention policies
- PCI-DSS: Secure artifact storage, vulnerability management
- GDPR: Data encryption, access controls, audit trails
Native CI/CD Integration
Integration with CI/CD pipelines transforms Harness AR from a passive storage layer into an active participant in delivery workflows. Pipelines can publish artifacts to AR automatically after successful builds, consume artifacts as deployment inputs, and trigger downstream actions based on artifact availability. This integration pattern reduces manual coordination while maintaining the governance boundaries that platform teams require.
Conclusion: Artifact Management as a Competitive Advantage
Developer experience improves when infrastructure removes friction rather than adding process. Artifact Registries succeed when developers barely notice them: artifacts are always available, builds are consistently fast, dependencies are trustworthy, and workflows remain predictable. This invisibility requires deliberate platform engineering that prioritizes reliability, performance, and governance from the start.
The investment in proper binary repository management pays dividends across the development lifecycle. Faster builds mean faster feedback loops. Secure artifact pipelines mean fewer production incidents. Reproducible deployments mean confident releases. These benefits compound as teams scale, transforming artifact management from an operational cost center into a productivity multiplier.
Organizations that treat Artifact Registry developer experience as a strategic concern gain measurable advantages: reduced time to deployment, improved software supply chain security posture, lower infrastructure costs, and higher DevOps developer productivity. Those who treat it as a solved problem inherit the accumulated technical debt of fragmented tooling, manual processes, and preventable incidents. The choice determines whether artifact management enables velocity or constrains it.
Get Started with Harness Artifact Registry
Ready to transform your artifact management and reclaim $1.46 million in lost developer productivity?
Start your free trial: Get Started with Harness Artifact Registry
See it in action: Watch Demo
Talk to an expert: Schedule a Personalized Demo
Artifact Security: Closing the Gap in Your DevSecOps Strategy
Download this ebook to learn why artifacts are the missing layer in DevSecOps and how an artifact-aware approach helps close the gap between what is tested and what is ultimately deployed.
%2520copy.png)

